IDENTITY MANAGEMENT AND STUDENT RECORDS Andrea Beesing, Cornell
70 Slides3.36 MB
IDENTITY MANAGEMENT AND STUDENT RECORDS Andrea Beesing, Cornell University Jeff von Munkwitz-Smith, University of Connecticut Ann West, EDUCAUSE/Internet2/InCommon AACRAO Tech - July 19, 2009 1
Agenda Why Should We Care About Identity Management? Identity Management 101 Federated Identity Break Discussion Resources and Next Steps AACRAO Tech - July 19, 2009 2
Why Should We Care About Identity Management? The short answer is that we’ve always cared. AACRAO Tech - July 19, 2009 3
Directions to Prospective Students Connecticut Agricultural College, 1917 Write for the formal application blank, answer the questions it contains, and mail it as early as possible to the President in order to facilitate dormitory and dining room arrangements. Check trunks and send express packages to Willimantic. Address freight to Eagleville. Be sure to tag all packages and baggage with your name and correct destination. AACRAO Tech - July 19, 2009 4
Write to the Secretary of the Connecticut Agricultural College stating the date and time of your arrival. Upon arrival at the College, call at the office of the Registrar for registration and directions. Read carefully announcements on the bulletin board. AACRAO Tech - July 19, 2009 5
More Recently Movement from personal knowledge of individuals to physical identifiers (i.e., ID cards). Creation of pins and passwords for early touchtone registration and on-line access systems. Creation and maintenance of multiple IDs and passwords as services expanded (registration, email, course management systems, etc.) Identity Management on a system-by-system basis! AACRAO Tech - July 19, 2009 6
Why Should We Care More Now? The old models are not scalable. Students, faculty, and others need access to more services, sooner, and often remotely, than ever before. We may never even see the people using our services. AACRAO Tech - July 19, 2009 7
We aren’t always the provider of the service, but may still need to authenticate the users. There are heightened concerns for individual privacy. We may have contractual obligations to outside providers. AACRAO Tech - July 19, 2009 8
Developing and maintaining service-by-service mechanisms to managing identity is expensive. For individuals, managing multiple IDs and passwords for our institutions is a burden and often leads to weaker passwords or poor practices. Transitions from role to role or even within roles create problems unless they are managed well. AACRAO Tech - July 19, 2009 9
And Finally There are more regulatory requirements than ever before: Family Educational Rights and Privacy Act (FERPA) - 1974 Health Insurance Portability and Accountability Act (HIPAA) - 1996 Gramm-Leach-Bliley Act (GLB) - 1999 “Red flags Rule” – 2009 Revised FERPA regulations - 2009 AACRAO Tech - July 19, 2009 10

What’s New with FERPA? A few highlights: Authentication “Direct control” standard Access control Recommendations for Safeguarding Education Records AACRAO Tech - July 19, 2009 11
Authentication “The regulations in § 99.31(c) require educational agencies and institutions to use reasonable methods to identify and authenticate the identity of parents, students, school officials and other parties to whom the agency or institution discloses personally identifiable information from education records. The use of widely available information to authenticate identity, such as the recipient’s name, date of birth, SSN or student ID number, is not considered reasonable under the regulations.” – Department of Education analysis of regulations, December 2008 AACRAO Tech - July 19, 2009 12
“Direct Control” Standard “An agency or institution must ensure that an outside party providing institutional services or functions does not use or allow access to education records except in strict accordance with the requirements established by the educational agency or institution that discloses the information.” – Department of Education analysis of regulations, December 2008 AACRAO Tech - July 19, 2009 13
Access Control “The regulations in § 99.31(a)(1)(ii) will require an educational agency or institution to use reasonable methods to ensure that teachers and other school officials obtain access to only those education records in which they have legitimate educational interests. An educational agency or institution that chooses not to restrict access to education records with physical or technological controls, such as locked cabinets and role-based software security, must ensure that its administrative policy for controlling access is effective and that it remains in compliance with the legitimate educational interest requirement.” – Department of Education analysis of regulations, December 2008 AACRAO Tech - July 19, 2009 14
Safeguards “Although FERPA does not dictate requirements for safeguarding education records, the Department encourages the holders of personally identifiable information to consider actions that mitigate the risk and are reasonably calculated to protect such information.” – Department of Education analysis of regulations, December 2008 AACRAO Tech - July 19, 2009 15
Resources on Safeguarding Education Records Department of Education The National Institute of Standards and Technology (NIST) 800–100, “Information Security Handbook: A Guide for Managers” NIST 800–53, “Information Security” Office of Management and Budget May 22, 2007 memorandum on safeguards to protect personally identifiable information Federal Register / Vol. 73, No. 237 / Tuesday, December 9, 2008 / Rules and Regulations AACRAO Tech - July 19, 2009 16
Identity Management 101 AACRAO Tech - July 19, 2009 17
What is Identity Management (IdM)? Identity management is the term used to describe the business processes, standards, practices, and technologies which enable people to take full advantage of online resources in a way which balances the need for functionality with the need for data security and privacy. It is built upon the three cornerstones of policy, process and IT infrastructure. AACRAO Tech - July 19, 2009 18
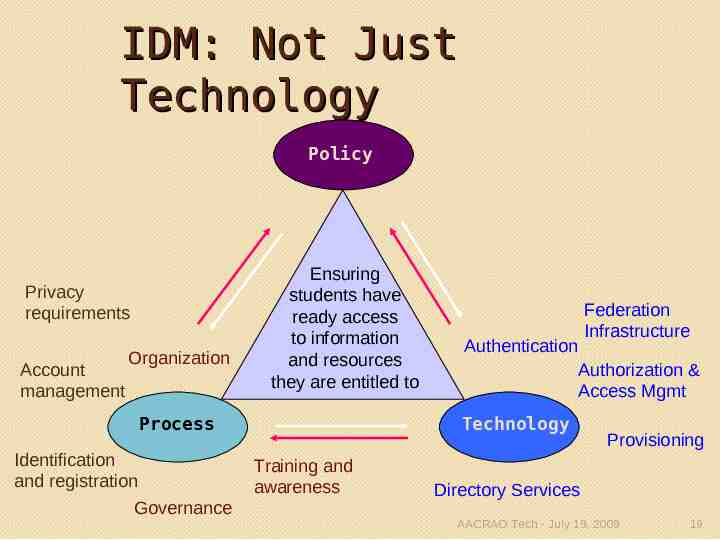
IDM: Not Just Technology Policy Privacy requirements Account management Organization Ensuring students have ready access to information and resources they are entitled to Process Identification and registration Governance Federation Infrastructure Authentication Authorization & Access Mgmt Technology Training and awareness Provisioning Directory Services AACRAO Tech - July 19, 2009 19
Policy & Identity Management “Cornell's policies connect the university's mission to the everyday actions of its community, clarify the institution's expectations of its individual members, mitigate institutional risk, enhance efficiency, and support the university's compliance with laws and regulations.” Policy is a key driver in determining how identity management is implemented. AACRAO Tech - July 19, 2009 20

University Policies 4.4 Access to Cornell Alumni Affairs Information 4.6 Ethical Conduct 4.5 Access to Student Information 4.12 Data Stewardship and Custodianship AACRAO Tech - July 19, 2009 21
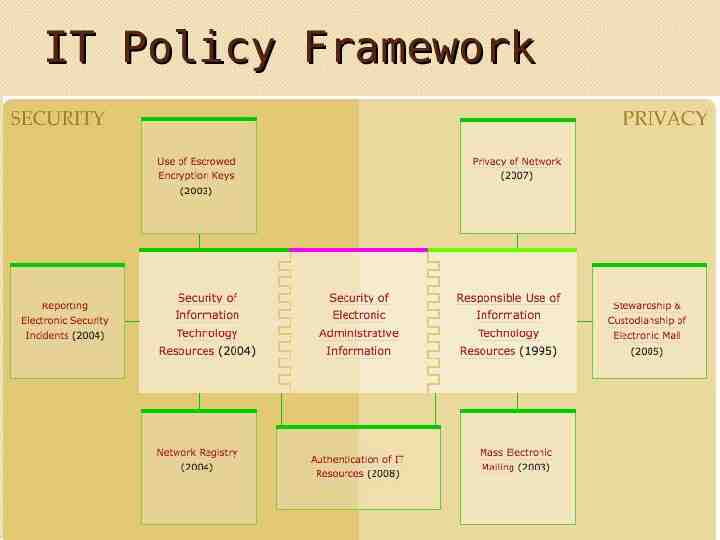
IT Policy Framework
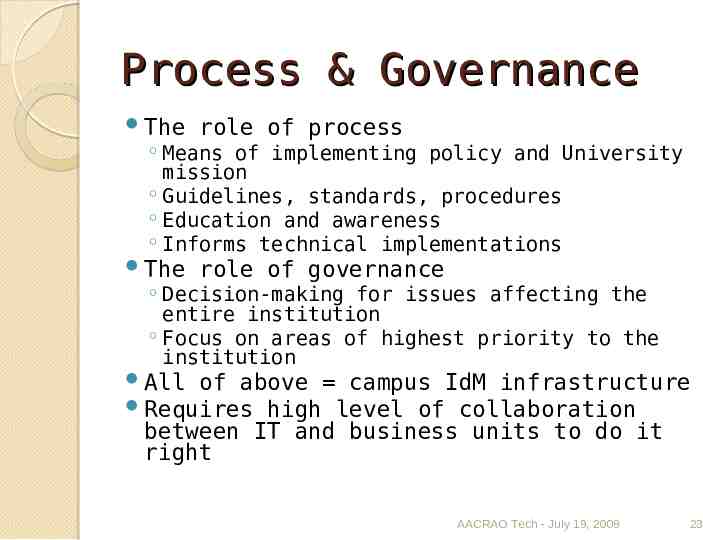
Process & Governance The role of process The role of governance Means of implementing policy and University mission Guidelines, standards, procedures Education and awareness Informs technical implementations Decision-making for issues affecting the entire institution Focus on areas of highest priority to the institution All of above campus IdM infrastructure Requires high level of collaboration between IT and business units to do it right AACRAO Tech - July 19, 2009 23
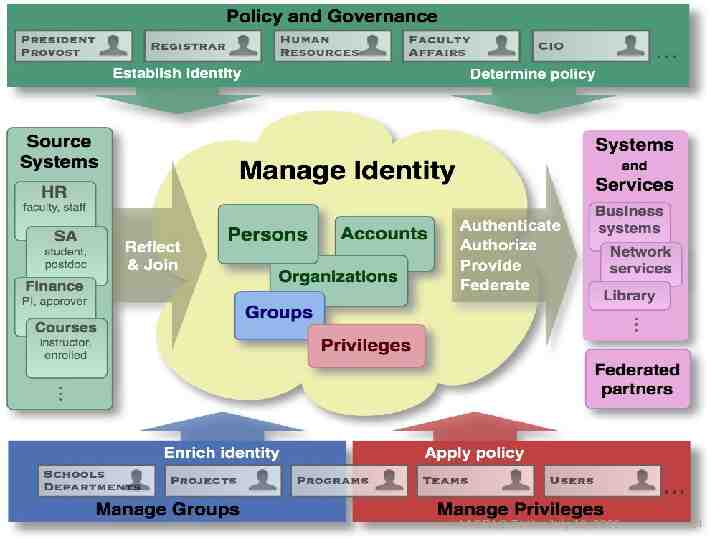
IT Policies AACRAO Tech - July 19, 2009 24
Case Study: Secure Access to Services An important goal of identity management is secure user access. Secure user access means that there is a high level of assurance that the people accessing the service are who they claim to be (authentication) and that they are entitled to use the service (authorization) based on their relationship with the institution. AACRAO Tech - July 19, 2009 25
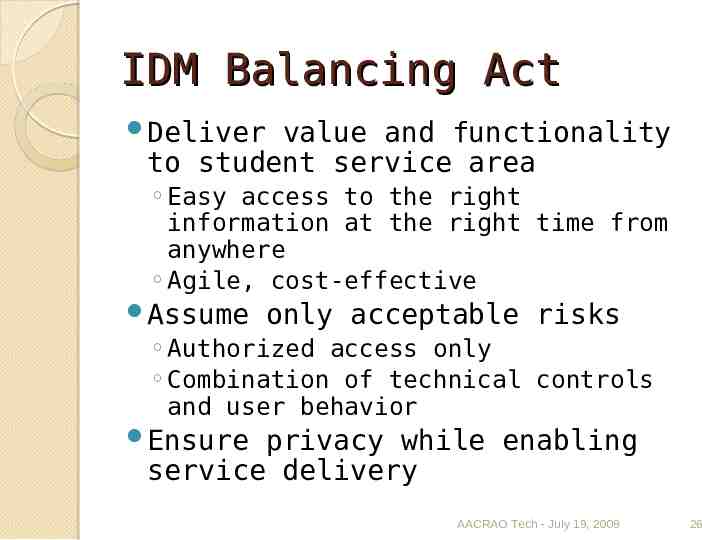
IDM Balancing Act Deliver value and functionality to student service area Easy access to the right information at the right time from anywhere Agile, cost-effective Assume only acceptable risks Authorized access only Combination of technical controls and user behavior Ensure privacy while enabling service delivery AACRAO Tech - July 19, 2009 26
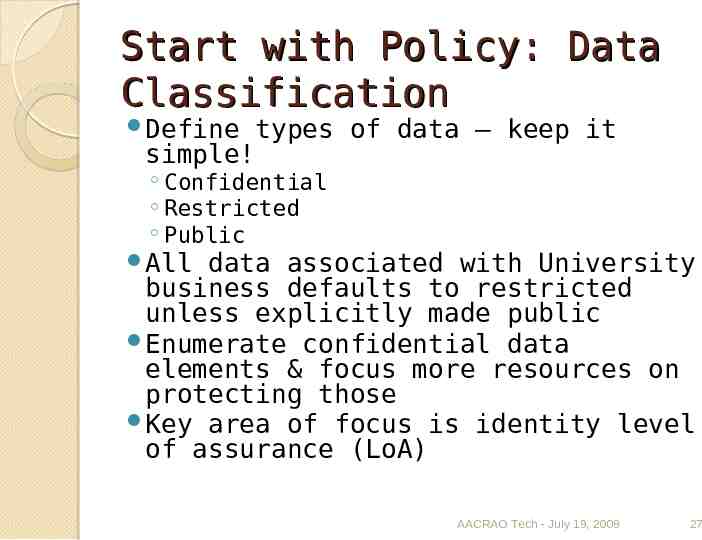
Start with Policy: Data Classification Define types of data – keep it simple! Confidential Restricted Public All data associated with University business defaults to restricted unless explicitly made public Enumerate confidential data elements & focus more resources on protecting those Key area of focus is identity level of assurance (LoA) AACRAO Tech - July 19, 2009 27
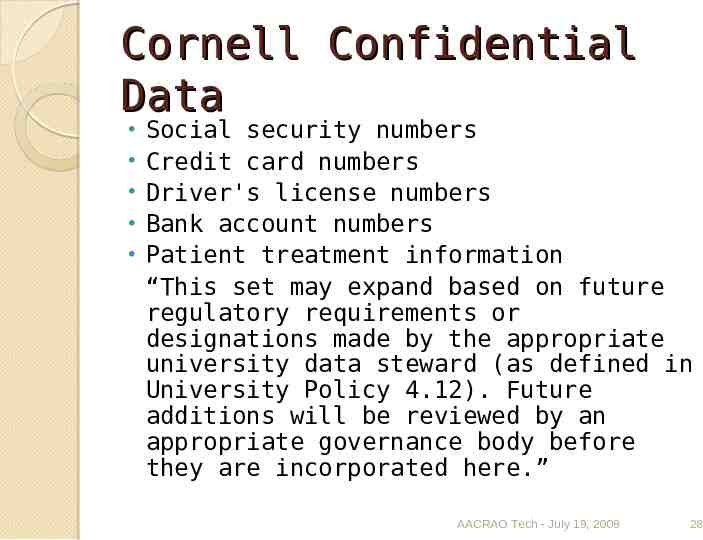
Cornell Confidential Data Social security numbers Credit card numbers Driver's license numbers Bank account numbers Patient treatment information “This set may expand based on future regulatory requirements or designations made by the appropriate university data steward (as defined in University Policy 4.12). Future additions will be reviewed by an appropriate governance body before they are incorporated here.” AACRAO Tech - July 19, 2009 28
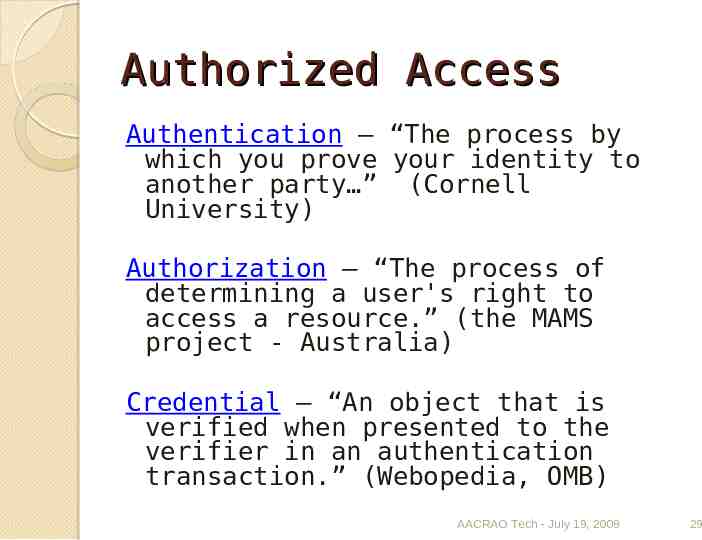
Authorized Access Authentication – “The process by which you prove your identity to another party ” (Cornell University) Authorization – “The process of determining a user's right to access a resource.” (the MAMS project - Australia) Credential – “An object that is verified when presented to the verifier in an authentication transaction.” (Webopedia, OMB) AACRAO Tech - July 19, 2009 29
Authorized Access: Authentication Not just the credential—NetID and password for example Processes matter—beware the weak link! ID proofing Record maintenance Distribution of initial password User awareness – managing user behavior The parent challenge/recredentialing AACRAO Tech - July 19, 2009 30
Authorized Access: Authentication Robust, centralized infrastructure is also key One NetID for life Integrates with variety of applications Password resistance to guessing/cracking When and where is dual-factor authentication needed? Effectively managing risk vs. avoiding impacting user experience AACRAO Tech - July 19, 2009 31
All of Above Level of Assurance Level of Assurance (LoA) – “Describes the degree of certainty that the user has presented an identifier (a credential in this context) that refers to his or her identity.” (NMI-EDIT) Standards documents are valuable reference NIST Special Publication 800-63 InCommon Bronze & Silver Identity Assurance Profile AACRAO Tech - July 19, 2009 32
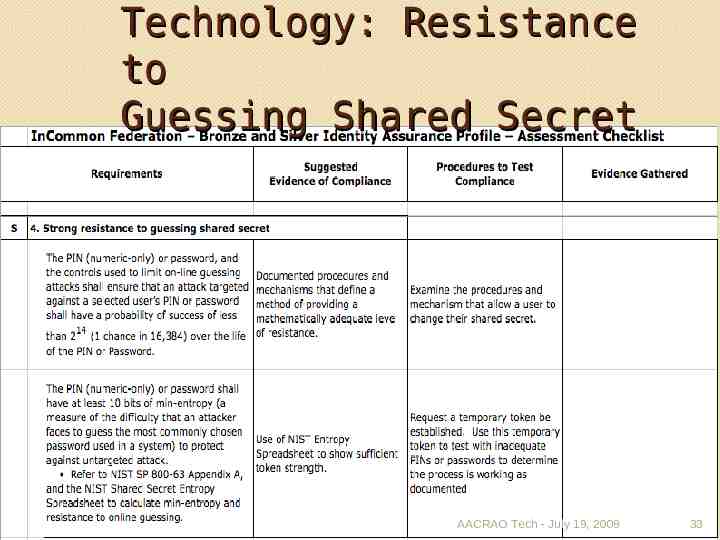
Technology: Resistance to Guessing Shared Secret AACRAO Tech - July 19, 2009 33
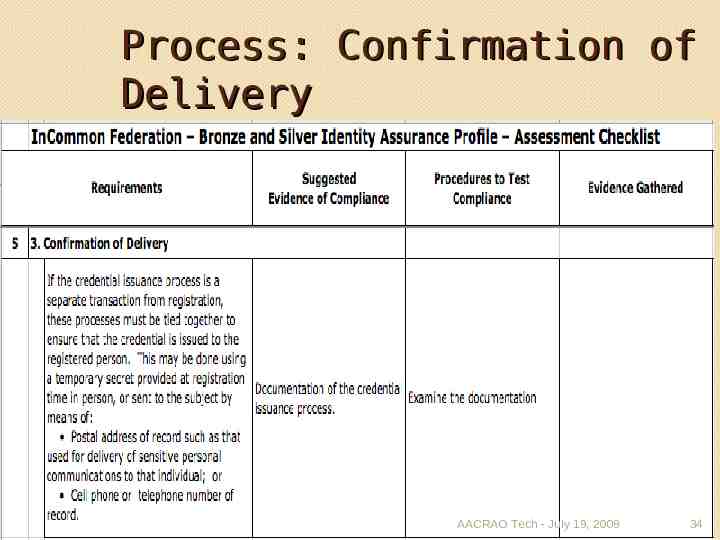
Process: Confirmation of Delivery AACRAO Tech - July 19, 2009 34
Process Drill-down: ApplicantID vs. NetID Differing business needs Temporary (use once & delete) vs. assigned for life Volume and cost of providing the service 38,000 undergraduate applicants (ApplicantIDs) 3,800 matrics (NetIDs) Differing risks based on data accessed Processes and technologies will probably differ Distribution of initial password: email vs. U.S. mail Stronger authentication technologies: single vs. dual -factor AACRAO Tech - July 19, 2009 35
Authorized Access: Authorization Risk plays a role here Authorization based on too Relationship to the University Role Assurance of identity Combination of above Role: “Collection of common requirements, tasks and business functions performed by individuals using an application support “system”. Based upon these common requirements, specific common services can be allocated.” (Indiana U.) AACRAO Tech - July 19, 2009 36
IDM Support for Authorized Access Centralized access management solutions with shared operational responsibility IT implements and maintains group and privilege management infrastructure Business units use them to assign access based on established policy Governance is result of collaboration between IT and business units Establishes authority for deciding who has access Assists in operational reflection of institutional decisions AACRAO Tech - July 19, 2009 37
Application Access IT staff are data custodians—can implement access but not determine (defined in policy 4.12) Process defined for access requests decisions Template to be filled out by customer with help from Data Administration staff DA staff works with data stewards to obtain decision AACRAO Tech - July 19, 2009 38
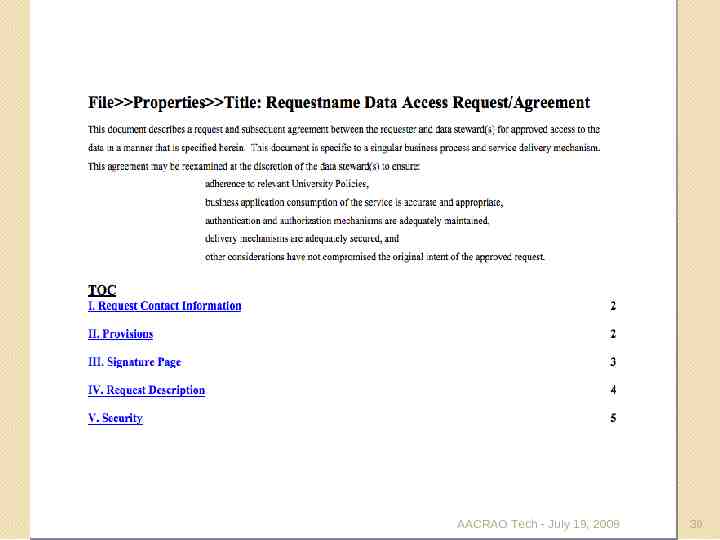
AACRAO Tech - July 19, 2009 39
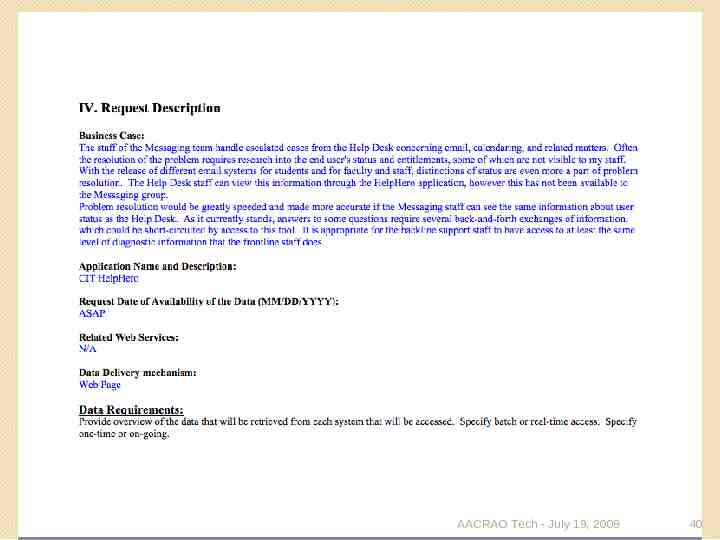
AACRAO Tech - July 19, 2009 40
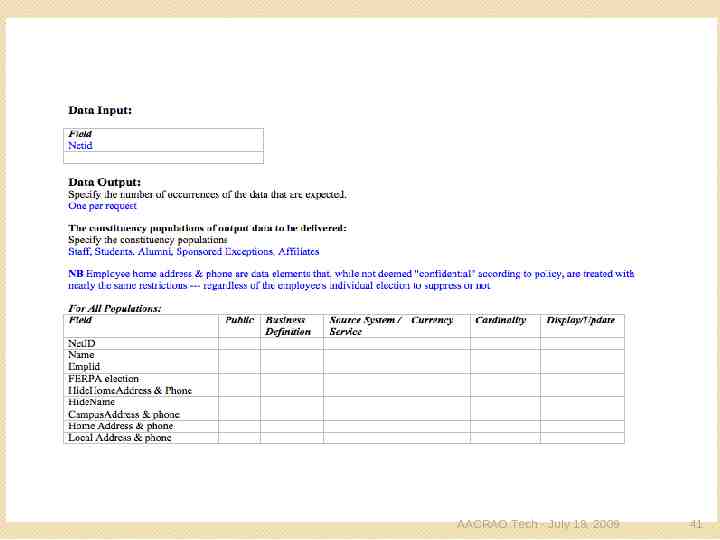
AACRAO Tech - July 19, 2009 41
Access for Individuals Point-to-point access management works for application access case and for some large, centralized services like Banner, PeopleSoft But many distributed systems are managed by many staff in many units Distributed model with governance needed Common set of access management tools Distributed and shared responsibility for daily operations AACRAO Tech - July 19, 2009 42
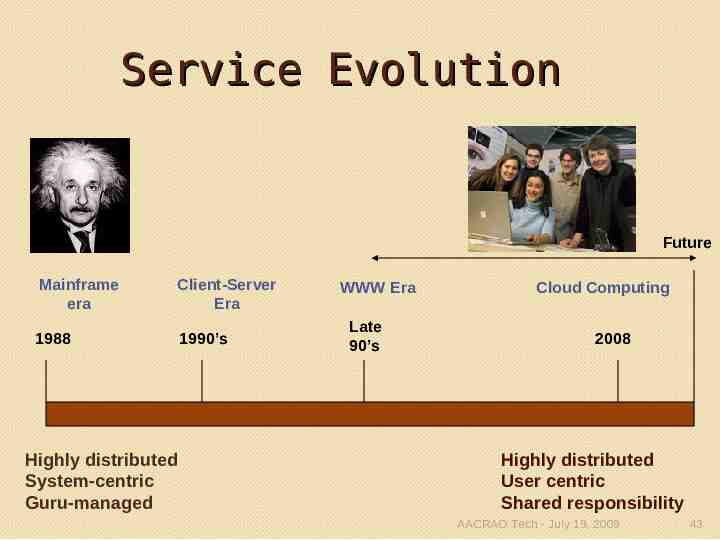
Service Evolution Future Mainframe era Client-Server Era 1988 1990’s Highly distributed System-centric Guru-managed WWW Era Late 90’s Cloud Computing 2008 Highly distributed User centric Shared responsibility AACRAO Tech - July 19, 2009 43
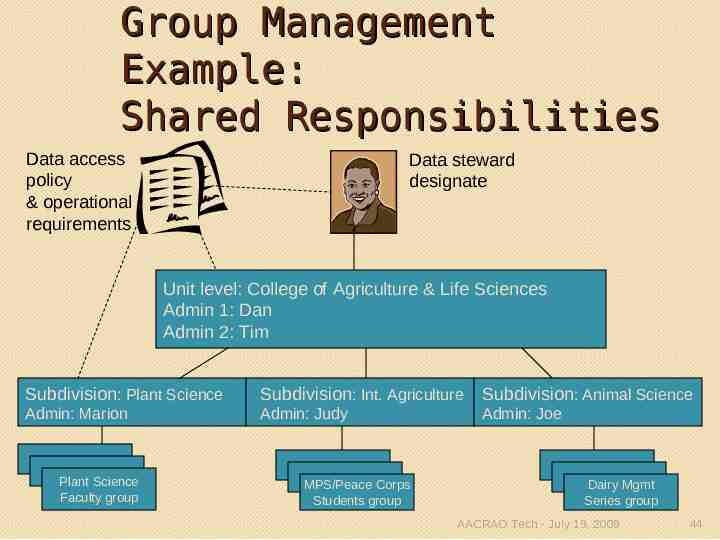
Group Management Example: Shared Responsibilities Data access policy & operational requirements Data steward designate Unit level: College of Agriculture & Life Sciences Admin 1: Dan Admin 2: Tim Subdivision: Plant Science Subdivision: Int. Agriculture Subdivision: Animal Science Admin: Marion Admin: Judy Admin: Joe Plant Science Faculty group MPS/Peace Corps Students group Dairy Mgmt Series group AACRAO Tech - July 19, 2009 44 44
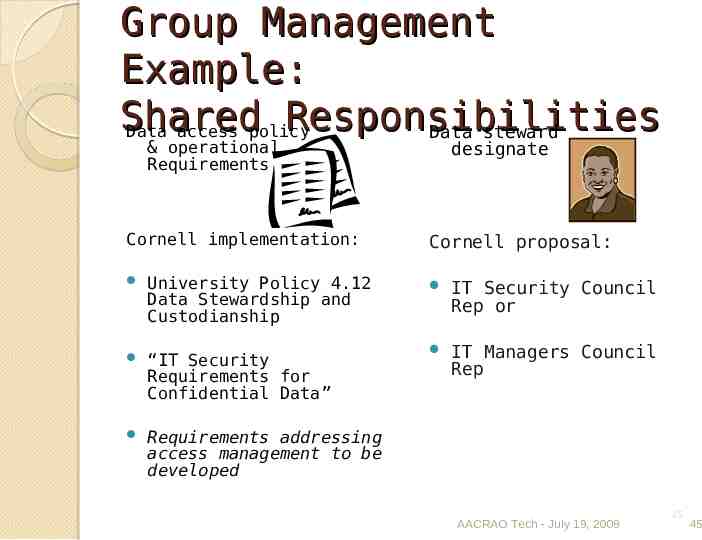
Group Management Example: Shared Responsibilities Data access policy Data steward & operational Requirements Cornell implementation: designate Cornell proposal: University Policy 4.12 Data Stewardship and Custodianship IT Security Council Rep or “IT Security Requirements for Confidential Data” IT Managers Council Rep Requirements addressing access management to be developed AACRAO Tech - July 19, 2009 45 45
Federated Identity Management: Off-campus Services AACRAO Tech - July 19, 2009 46
Bedtime Story It's 3:00 am and Bianca is sitting in a 24 hour Starbucks in the spring semester of her senior year, working on her Physics 456 homework. In a browser, she clicks on the link to the course management system, logs in with her University web single sign-on userid and password, and starts viewing the course information. Next, she clicks on the homework link hosted by a third-party provider and "Welcome Bianca" appears along with her new homework assignment for that class. After finishing that, she decides to check her loan status and surfs to the web site of her financing agent. She clicks "Access your record" and is presented with an aggregation of her loan liability without having to identify herself or login. In April, Bianca graduated. One day she was a student and the next, an alumna. She noticed her access changed too. She now could get to an alumni networking service where she put out a query about apartments in the Bay Area. Her loan status had changed on the financing agent's site. She now was out in the wide world of opportunity and responsibility. AACRAO Tech - July 19, 2009 47
The Problem How many off-campus applications do you have? How do these service providers Verify the identity of your students? Know who’s eligible to access the service? Know the student is active and hasn’t left school? How comfortable are you with the security and privacy of the identity data? AACRAO Tech - July 19, 2009 48
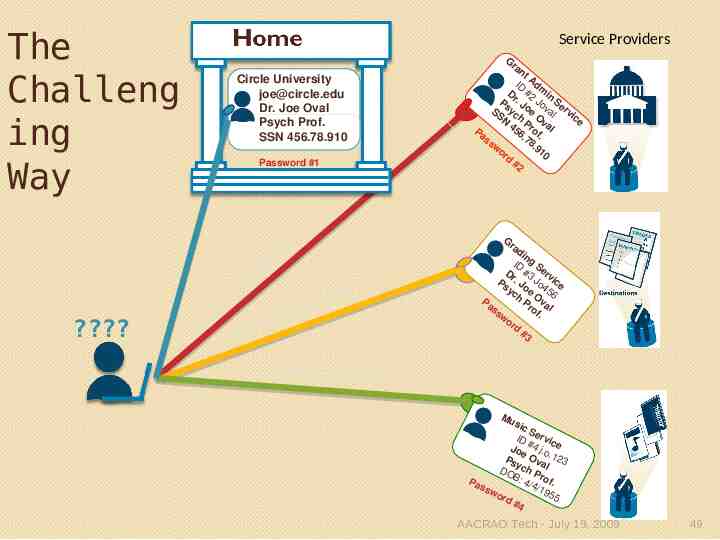
The Challeng ing Way ? Service Providers Circle University [email protected] Dr. Joe Oval Psych Prof. SSN 456.78.910 Password #1 No o co tio a in rd n ieta r p Pro de o c ry Gr an t ID Adm D #2 in Ps r. J Jo Se SS yc oe val rvi ce N h P Ov al 4 r o 5 Pa 6. f. 78 ss .9 w or 10 d #2 Gr ad in ID g S D #3 erv Ps r. Jo Jo ice yc e 456 h Ov Pa Pr a of l ss . wo rd #3 Batch uploads Mu sic S ID ervic # Jo 4 j.o e e Ps Ova .123 ych l DO B: Prof Pa 4/4 . ssw /19 55 ord #4 AACRAO Tech - July 19, 2009 49
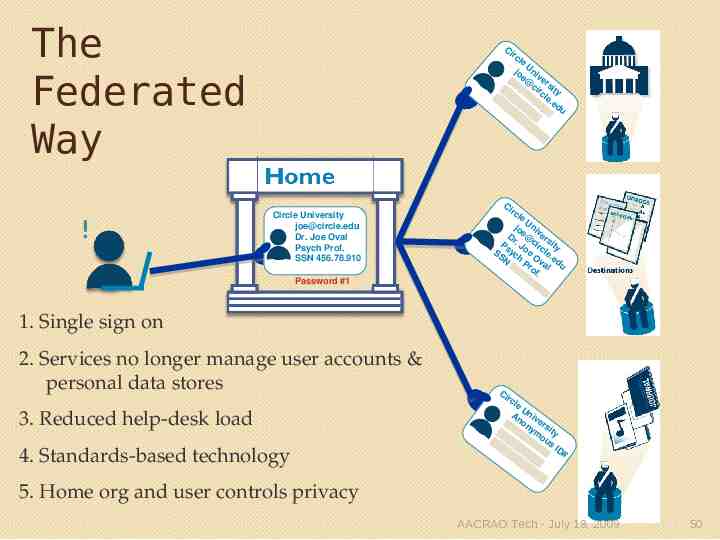
The Federated Way ! Ci rc le U jo niv Dr e@ er Ps . J cir sity SS ych oe O cle N v .e 4 5 P r o a l du 6. f. 78 .9 10 Circle University [email protected] Dr. Joe Oval Psych Prof. SSN 456.78.910 Password #1 Ci rc le U jo niv Dr e@ ers Ps . J cir ity SS yc oe O cle. N h P v a ed 45 ro l u 6. f. 78 .9 10 1. Single sign on 2. Services no longer manage user accounts & personal data stores 3. Reduced help-desk load 4. Standards-based technology Ci rc le U An niv Dr on ers Ps . Jo ymo ity SS ych e O us N P r v a ID # 45 of l 6. . 78 .91 0 5. Home org and user controls privacy AACRAO Tech - July 19, 2009 50
SAML and Shibboleth Security Assertion Markup Language (SAML) Standard for the formation and exchange of authentication, attribute, and authorization data as XML. Shibboleth Single Sign-on and Federating Software Open source software uses SAML to perform this exchange across boundaries AACRAO Tech - July 19, 2009 51
Shibboleth In Action AACRAO Tech - July 19, 2009 52
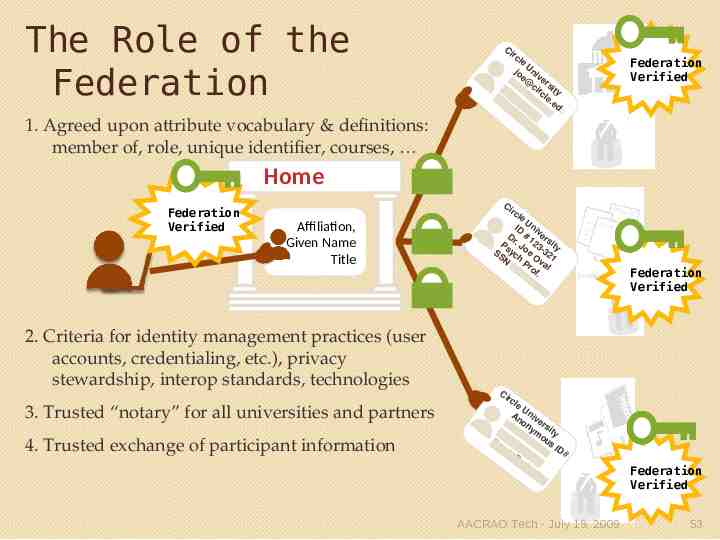
The Role of the Federation 1. Agreed upon attribute vocabulary & definitions: member of, role, unique identifier, courses, Ci rc le U jo niv Dr e@ er Ps . J cir sity SS ych oe O cle N v .e 4 5 P r o a l du 6. f. 78 .9 10 Federation Verified Home ! Federation Verified Affiliation, Given Name Title 2. Criteria for identity management practices (user accounts, credentialing, etc.), privacy stewardship, interop standards, technologies 3. Trusted “notary” for all universities and partners 4. Trusted exchange of participant information Ci rc le U ID niv Dr # 1 ers Ps . J 23 ity SS yc oe O -32 N h P va 1 45 ro l 6. f. 78 .9 10 Ci rc le U An niv on ers ym ity Dr ou Ps . Jo s yc e O ID h # Pr val of . AACRAO Tech - July 19, 2009 Federation Verified Federation Verified 53

Federations: Who’s Using This Approach? Higher-Education Systems U of TX, U of CA, U of MD Network Providers NJEdge, MCNC (North Carolina), Great Plains Network National UK, Switzerland, The Netherlands, Sweden, Norway, Denmark, France, Germany, Australia and US AACRAO Tech - July 19, 2009 54
Federations: Why? Minimizing distribution of PII Pass only what’s needed for access Privacy can be maintained Service tied to role and affiliation status Changes affect access: Security Ease of use Time and money savings SSO for on- and off-campus services Timely access Use of the same technologies and standards for each service partner AACRAO Tech - July 19, 2009 55
InCommon Federation US Research and Education Federation www.incommon.org LLC operated by Internet2 with separate governance 159 participants representing over 3 million individuals. Agree to a common participation rules that allows each to interoperate with the others Sets basic practices for identity providers and service providers 56 AACRAO Tech - July 19, 2009 56
InCommon Identity Assurance Specifies criteria used to assess the credential strength of identity providers: InCommon Bronze and Silver Identity Assurance Profiles Provides initial practices for authentication processes and technology Based on Foundational Government Standard: NIST 800-63 Electronic Authentication Guideline AACRAO Tech - July 19, 2009 57

InCommon Activities Collaboration InC-Library, InC-Student, InC-NIH, InC-Research, InC-Apple, Dreamspark National and International standards Co-wrote SAML spec Involved in WS-Fed, OASIS, Terena, ISOC, and Liberty Alliance and other standards and federation organizations Working with PESC Development Work Interfederation, Privacy and Consent, Evolution of Federations AACRAO Tech - July 19, 2009 58
FERPA Impacts on Federations Only available for services institution would otherwise provide “A contractor (or other outside service provider) that is given access to education records under this provision must be under the direct control of the disclosing institution and subject to the same conditions on use and redisclosure of education records that govern other school officials.” -- DOE Section-by-Section Analysis of Final Rule (12/08) AACRAO Tech - July 19, 2009 59
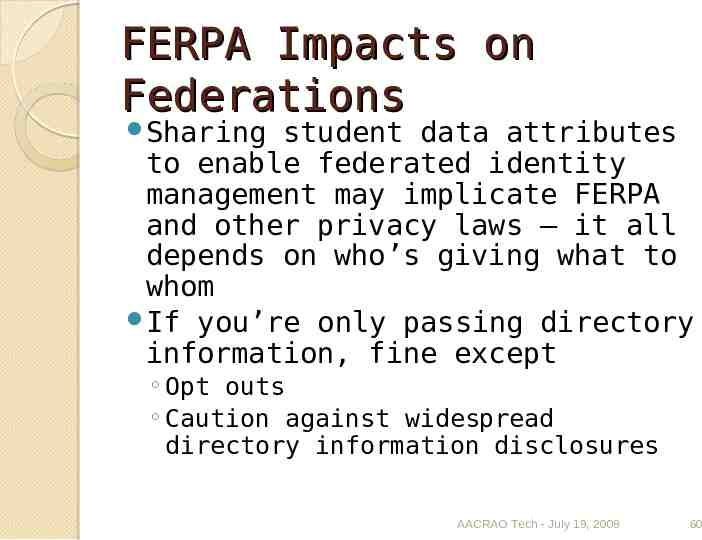
FERPA Impacts on Federations Sharing student data attributes to enable federated identity management may implicate FERPA and other privacy laws – it all depends on who’s giving what to whom If you’re only passing directory information, fine except Opt outs Caution against widespread directory information disclosures AACRAO Tech - July 19, 2009 60
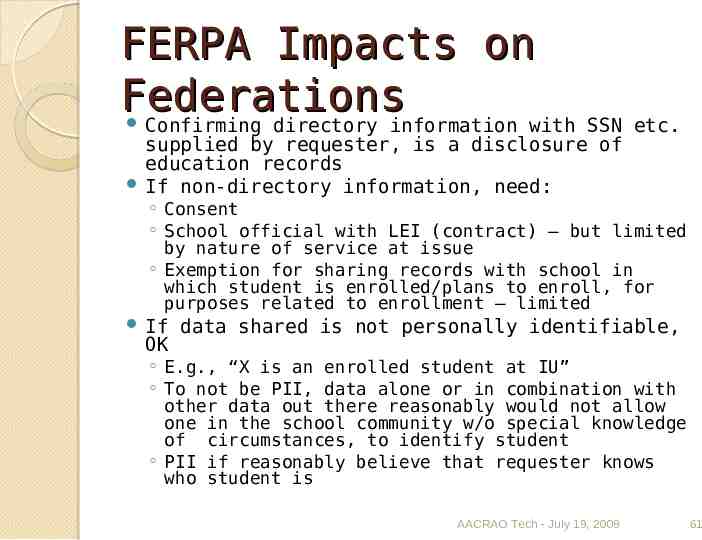
FERPA Impacts on Federations Confirming directory information with SSN etc. supplied by requester, is a disclosure of education records If non-directory information, need: Consent School official with LEI (contract) – but limited by nature of service at issue Exemption for sharing records with school in which student is enrolled/plans to enroll, for purposes related to enrollment – limited If OK data shared is not personally identifiable, E.g., “X is an enrolled student at IU” To not be PII, data alone or in combination with other data out there reasonably would not allow one in the school community w/o special knowledge of circumstances, to identify student PII if reasonably believe that requester knows who student is AACRAO Tech - July 19, 2009 61
BREAK AACRAO Tech - July 19, 2009 62
RESOURCES AACRAO Tech - July 19, 2009 63
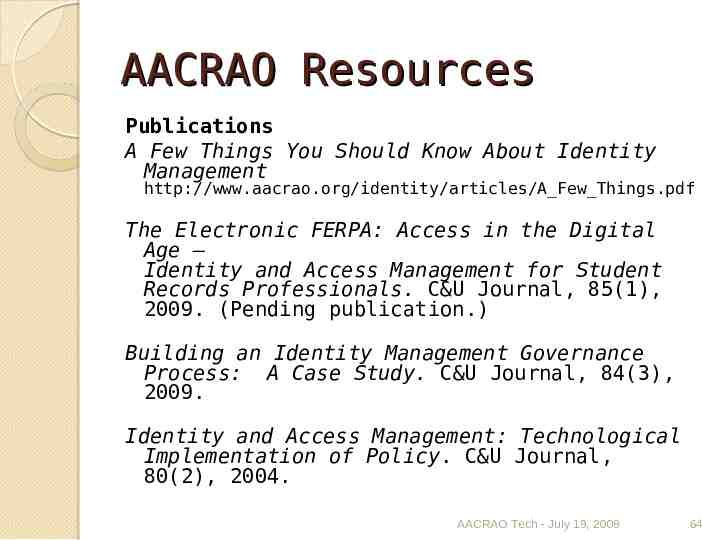
AACRAO Resources Publications A Few Things You Should Know About Identity Management http://www.aacrao.org/identity/articles/A Few Things.pdf The Electronic FERPA: Access in the Digital Age – Identity and Access Management for Student Records Professionals. C&U Journal, 85(1), 2009. (Pending publication.) Building an Identity Management Governance Process: A Case Study. C&U Journal, 84(3), 2009. Identity and Access Management: Technological Implementation of Policy. C&U Journal, 80(2), 2004. AACRAO Tech - July 19, 2009 64
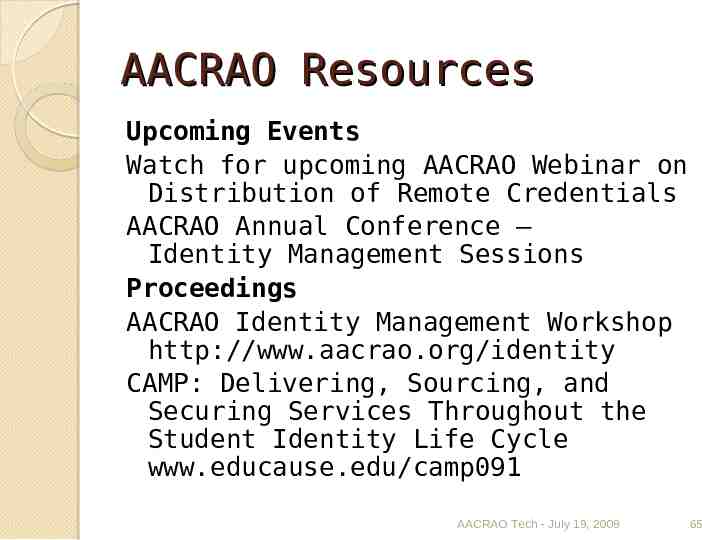
AACRAO Resources Upcoming Events Watch for upcoming AACRAO Webinar on Distribution of Remote Credentials AACRAO Annual Conference – Identity Management Sessions Proceedings AACRAO Identity Management Workshop http://www.aacrao.org/identity CAMP: Delivering, Sourcing, and Securing Services Throughout the Student Identity Life Cycle www.educause.edu/camp091 AACRAO Tech - July 19, 2009 65
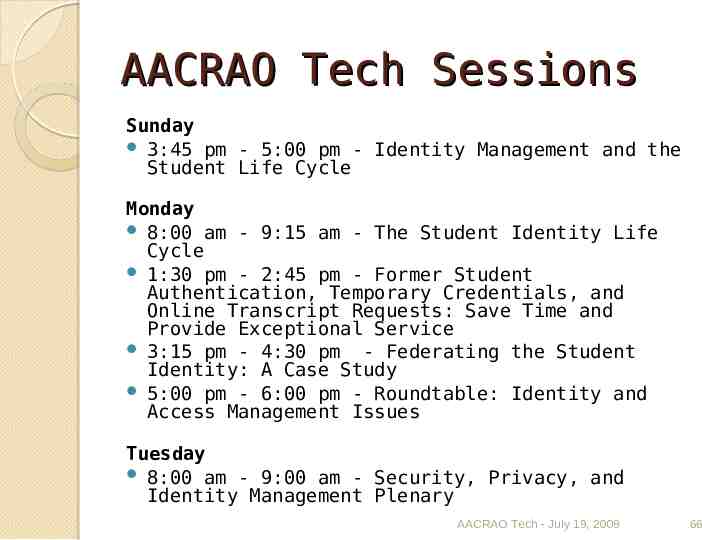
AACRAO Tech Sessions Sunday 3:45 pm - 5:00 pm - Identity Management and the Student Life Cycle Monday 8:00 am - 9:15 am - The Student Identity Life Cycle 1:30 pm - 2:45 pm - Former Student Authentication, Temporary Credentials, and Online Transcript Requests: Save Time and Provide Exceptional Service 3:15 pm - 4:30 pm - Federating the Student Identity: A Case Study 5:00 pm - 6:00 pm - Roundtable: Identity and Access Management Issues Tuesday 8:00 am - 9:00 am - Security, Privacy, and Identity Management Plenary AACRAO Tech - July 19, 2009 66
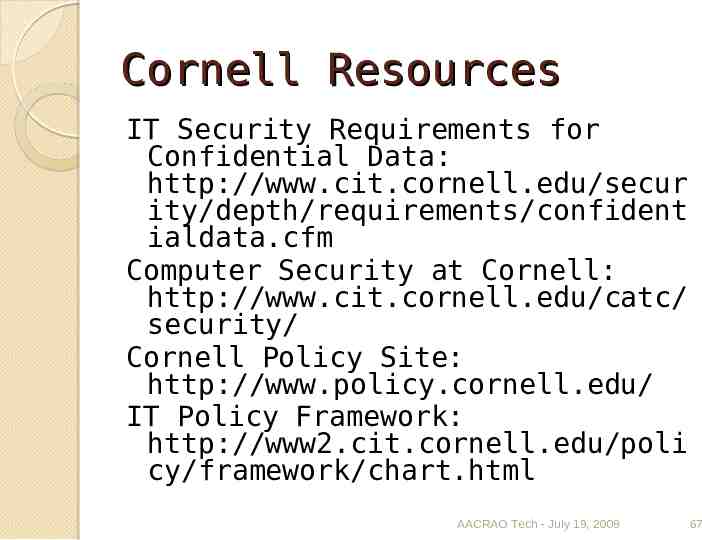
Cornell Resources IT Security Requirements for Confidential Data: http://www.cit.cornell.edu/secur ity/depth/requirements/confident ialdata.cfm Computer Security at Cornell: http://www.cit.cornell.edu/catc/ security/ Cornell Policy Site: http://www.policy.cornell.edu/ IT Policy Framework: http://www2.cit.cornell.edu/poli cy/framework/chart.html AACRAO Tech - July 19, 2009 67
Federation Resources NIST Special Publication 80063: http://www.cio.gov/eauthentic ation/ InCommon Federation: http://incommonfederation.org InCommon Identity Assurance: http://www.incommonfederation .org/assurance/ AACRAO Tech - July 19, 2009 68
Federation Case Studies Dreamspark Student Verification Through InCommon www.incommonfederation.org/docs/eg/InC CaseSt udy Dreamspark 2008.pdf Apple, InCommon Complete Pilot to Federate iTunes U www.incommonfederation.org/docs/eg/InC CaseSt udy iTunes 2008.pdf Small Colleges Benefit from Federated Services www.incommonfederation.org/docs/eg/InC CaseSt udy SmallCollege 2008.pdf Federating WebAssign Saves Time, Effort www.incommonfederation.org/docs/eg/InC CaseSt udy PSU WebAssign 2007.pdf Federating Simplifies Access to Symplicity Career Services www.incommonfederation.org/docs/eg/InC CaseSt udy PSU Symplicity 2007.pdf AACRAO Tech - July 19, 2009 69
Contacts Andrea Beesing Cornell University [email protected] Jeff von Munkwitz-Smith University of Connecticut [email protected] Ann West EDUCAUSE/Internet2/InCommon [email protected] AACRAO Tech - July 19, 2009 70