CSI 3140 WWW Structures, Techniques and Standards Web Essentials:
85 Slides1.61 MB
CSI 3140 WWW Structures, Techniques and Standards Web Essentials: Clients, Servers, and Communication
The Internet Technical origin: ARPANET (late 1960’s) One of earliest attempts to network heterogeneous, geographically dispersed computers Email first available on ARPANET in 1972 (and quickly very popular!) ARPANET access was limited to select DoD-funded organizations Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 2
The Internet Open-access networks Regional university networks (e.g., SURAnet) CSNET for CS departments not on ARPANET NSFNET (1985-1995) Primary purpose: connect supercomputer centers Secondary purpose: provide backbone to connect regional networks Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 3
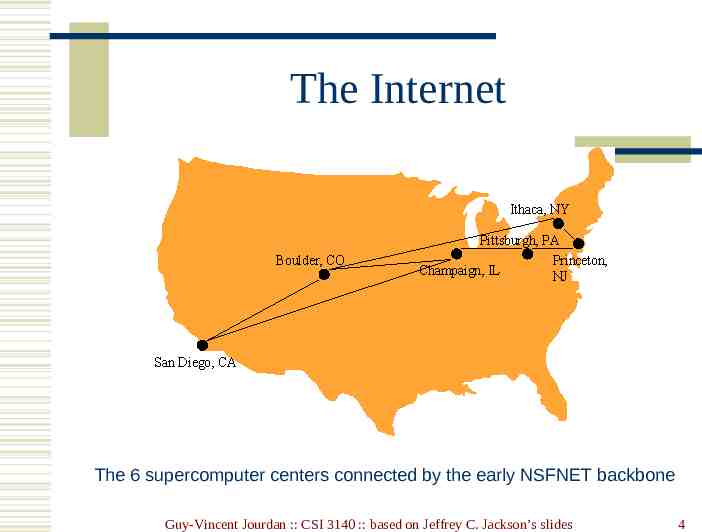
The Internet The 6 supercomputer centers connected by the early NSFNET backbone Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 4
The Internet Original NSFNET backbone speed: 56 kbit/s Upgraded to 1.5 Mbit/s (T1) in 1988 Upgraded to 45 Mbit/s (T3) in 1991 In 1988, networks in Canada and France connected to NSFNET In 1990, ARPANET is decommissioned, NSFNET the center of the internet Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 5
The Internet Internet: the network of networks connected via the public backbone and communicating using TCP/IP communication protocol Backbone initially supplied by NSFNET, privately funded (ISP fees) beginning in 1995 Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 6
Internet Protocols Communication protocol: how computers talk Cf. telephone “protocol”: how you answer and end call, what language you speak, etc. Internet protocols developed as part of ARPANET research ARPANET began using TCP/IP in 1982 Designed for use both within local area networks (LAN’s) and between networks Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 7
Internet Protocol (IP) IP is the fundamental protocol defining the Internet (as the name implies!) IP address: 32-bit number (in IPv4) Associated with at most one device at a time (although device may have more than one) Written as four dot-separated bytes, e.g. 192.0.34.166 Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 8
IP IP function: transfer data from source device to destination device IP source software creates a packet representing the data Header: source and destination IP addresses, length of data, etc. Data itself If destination is on another LAN, packet is sent to a gateway that connects to more than one network Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 9
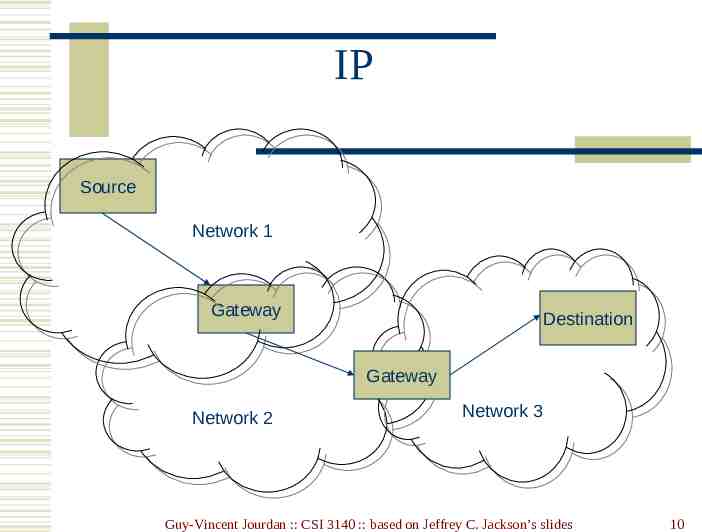
IP Source Network 1 Gateway Destination Gateway Network 2 Network 3 Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 10
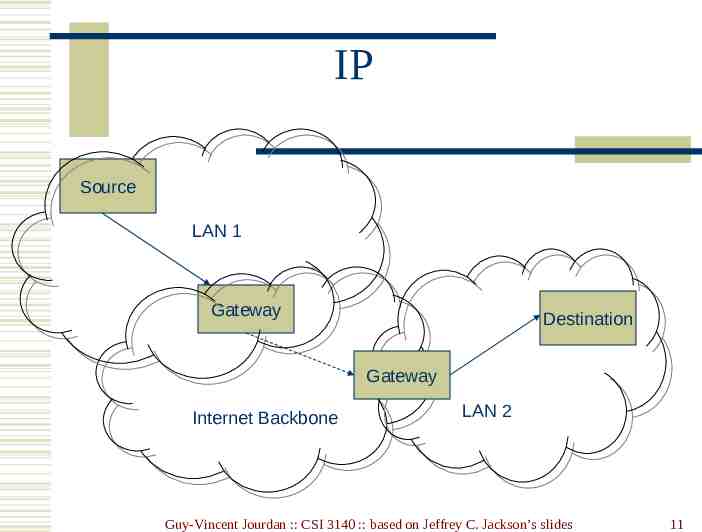
IP Source LAN 1 Gateway Destination Gateway Internet Backbone LAN 2 Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 11
Transmission Control Protocol (TCP) Limitations of IP: No guarantee of packet delivery (packets can be dropped) Communication is one-way (source to destination) TCP adds concept of a connection on top of IP Provides guarantee that packets delivered Provide two-way (full duplex) communication Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 12
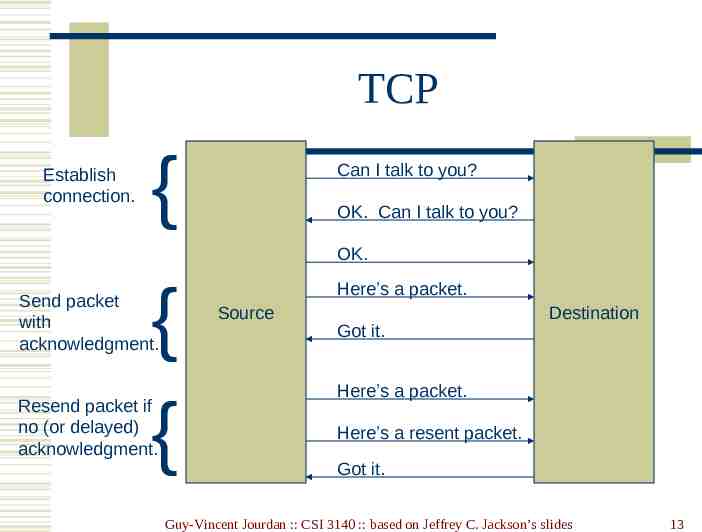
TCP Establish connection. { Can I talk to you? OK. Can I talk to you? OK. { { Send packet with acknowledgment. Resend packet if no (or delayed) acknowledgment. Here’s a packet. Source Got it. Destination Here’s a packet. Here’s a resent packet. Got it. Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 13
TCP TCP also adds concept of a port TCP header contains port number representing an application program on the destination computer Some port numbers have standard meanings Example: port 25 is normally used for email transmitted using the Simple Mail Transfer Protocol (SMTP) Other port numbers are available first-come-first served to any application Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 14
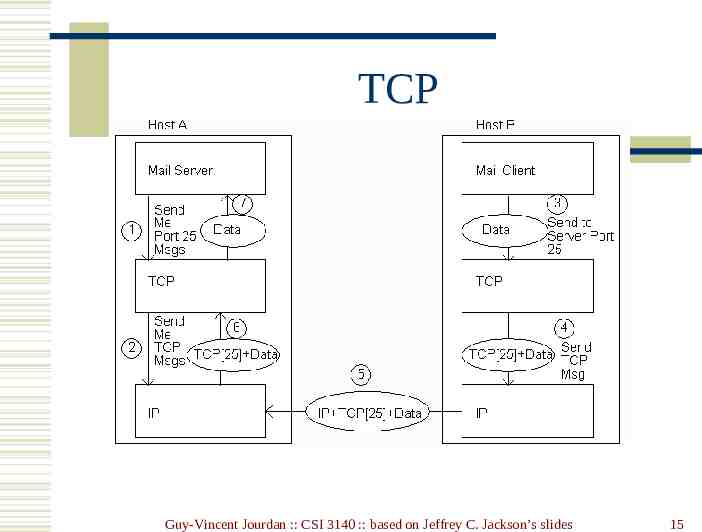
TCP Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 15
User Datagram Protocol (UDP) Like TCP in that: Builds on IP Provides port concept Unlike TCP in that: No connection concept No transmission guarantee Advantage of UDP vs. TCP: Lightweight, so faster for one-time messages Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 16
Domain Name Service (DNS) DNS is the “phone book” for the Internet Map between host names and IP addresses DNS often uses UDP for communication Host names Labels separated by dots, e.g., www.example.org Final label is top-level domain Generic: .com, .org, etc. Country-code: .us, .il, etc. Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 17
DNS Domains are divided into second-level domains, which can be further divided into subdomains, etc. E.g., in www.example.com, example is a second-level domain A host name plus domain name information is called the fully qualified domain name of the computer Above, www is the host name, www.example.com is the FQDN Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 18
DNS nslookup program provides command-line access to DNS (on most systems) looking up a host name given an IP address is known as a reverse lookup Recall that single host may have multiple IP addresses. Address returned is the canonical IP address specified in the DNS system. Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 19
DNS ipconfig (on windows) can be used to find the IP address (addresses) of your machine ipconfig /displaydns displays the contents of the DNS Resolver Cache (ipconfig /flushdns to flush it) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 20
Analogy to Telephone Network IP the telephone network TCP calling someone who answers, having a conversation, and hanging up UDP calling someone and leaving a message DNS directory assistance Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 21
Higher-level Protocols Many protocols build on TCP Telephone analogy: TCP specifies how we initiate and terminate the phone call, but some other protocol specifies how we carry on the actual conversation Some examples: SMTP (email) (25) FTP (file transfer) (21) HTTP (transfer of Web documents) (80) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 22
World Wide Web Originally, one of several systems for organizing Internet-based information Competitors: WAIS, Gopher, ARCHIE Distinctive feature of Web: support for hypertext (text containing links) Communication via Hypertext Transport Protocol (HTTP) Document representation using Hypertext Markup Language (HTML) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 23
World Wide Web The Web is the collection of machines (Web servers) on the Internet that provide information, particularly HTML documents, via HTTP. Machines that access information on the Web are known as Web clients. A Web browser is software used by an end user to access the Web. Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 24
Hypertext Transport Protocol (HTTP) HTTP is based on the request-response communication model: Client sends a request Server sends a response HTTP is a stateless protocol: The protocol does not require the server to remember anything about the client between requests. Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 25
HTTP Normally implemented over a TCP connection (80 is standard port number for HTTP) Typical browser-server interaction: User enters Web address in browser Browser uses DNS to locate IP address Browser opens TCP connection to server Browser sends HTTP request over connection Server sends HTTP response to browser over connection Browser displays body of response in the client area of the browser window Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 26
HTTP The information transmitted using HTTP is often entirely text Can use the Internet’s Telnet protocol to simulate browser request and view server response Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 27
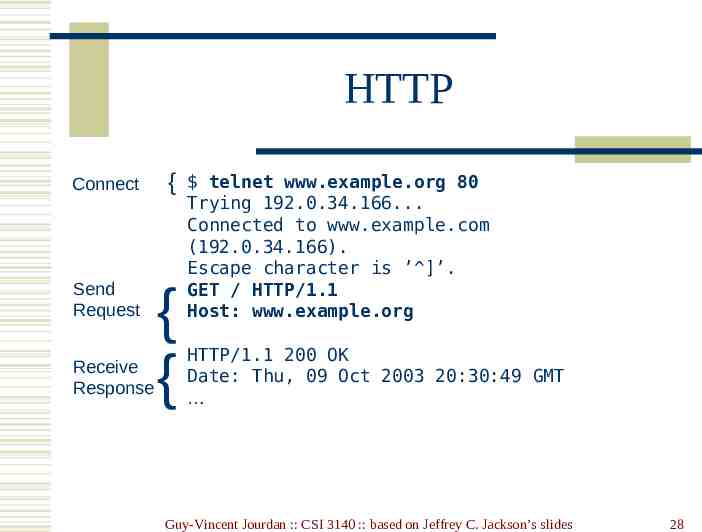
HTTP Connect { Send Request { { Receive Response telnet www.example.org 80 Trying 192.0.34.166. Connected to www.example.com (192.0.34.166). Escape character is ’ ]’. GET / HTTP/1.1 Host: www.example.org HTTP/1.1 200 OK Date: Thu, 09 Oct 2003 20:30:49 GMT Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 28
HTTP Request Structure of the request: start line header field(s) blank line optional body Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 29
HTTP Request Structure of the request: start line header field(s) blank line optional body Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 30
HTTP Request Start line Example: GET / HTTP/1.1 Three space-separated parts: HTTP request method Request-URI (Uniform Resource Identifier) HTTP version Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 31
HTTP Request Start line Example: GET / HTTP/1.1 Three space-separated parts: HTTP request method Request-URI HTTP version We will cover 1.1, in which version part of start line must be exactly as shown Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 32
HTTP Request Start line Example: GET / HTTP/1.1 Three space-separated parts: HTTP request method Request-URI HTTP version Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 33
HTTP Request Uniform Resource Identifier (URI) Syntax: scheme : scheme-depend-part In http://www.example.com/ the scheme is http Ex: Request-URI is the portion of the requested URI that follows the host name (which is supplied by the required Host header field) / is Request-URI portion of http://www.example.com/ Ex: Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 34
URI URI’s are of two types: Uniform Resource Name (URN) Can be used to identify resources with unique names, such as books (which have unique ISBN’s) Scheme is urn Uniform Resource Locator (URL) Specifies location at which a resource can be found In addition to http, some other URL schemes are https, ftp, mailto, and file Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 35
HTTP Request Start line Example: GET / HTTP/1.1 Three space-separated parts: HTTP request method Request-URI HTTP version Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 36
HTTP Request Common request methods: GET Used if link is clicked or address typed in browser No body in request with GET method POST Used when submit button is clicked on a form Form information contained in body of request HEAD Requests response that only header fields (no body) be returned in the Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 37
HTTP Request Structure of the request: start line header field(s) blank line optional body Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 38
HTTP Request Header field structure: field name : field value Syntax Field name is not case sensitive Field value may continue on multiple lines by starting continuation lines with white space Field values may contain MIME types, quality values, and wildcard characters (*’s) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 39
Multipurpose Internet Mail Extensions (MIME) Convention for specifying content type of a message In HTTP, typically used to specify content type of the body of the response MIME content type syntax: top-level type / subtype Examples: text/html, image/jpeg Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 40
HTTP Quality Values and Wildcards Example header field with quality values: accept: text/xml,text/html;q 0.9, text/plain;q 0.8, image/jpeg, image/gif;q 0.2,*/*;q 0.1 Quality value applies to all preceding items Higher the value, higher the preference Note use of wildcards to specify quality 0.1 for any MIME type not specified earlier Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 41
HTTP Request Common header fields: Host: host name from URL (required) User-Agent: type of browser sending request Accept: MIME types of acceptable documents Connection: value close tells server to close connection after single request/response Content-Type: MIME type of (POST) body, normally application/x-www-form-urlencoded Content-Length: bytes in body Referer: URL of document containing link that supplied URI for this HTTP request Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 42
HTTP Response Structure of the response: status line header field(s) blank line optional body Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 43
HTTP Response Structure of the response: status line header field(s) blank line optional body Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 44
HTTP Response Status line Example: HTTP/1.1 200 OK Three space-separated parts: HTTP version status code reason phrase (intended for human use) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 45
HTTP Response Status code Three-digit number First digit is class of the status code: 1 Informational 2 Success 3 Redirection (alternate URL is supplied) 4 Client Error 5 Server Error Other two digits provide additional information See http://www.w3.org/Protocols/rfc2616/rfc2616-sec10.html Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 46
HTTP Response Structure of the response: status line header field(s) blank line optional body Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 47
HTTP Response Common header fields: Connection, Content-Type, Content-Length Date: date and time at which response was generated (required) Location: alternate URI if status is redirection Last-Modified: date and time the requested resource was last modified on the server Expires: date and time after which the client’s copy of the resource will be out-of-date ETag: a unique identifier for this version of the requested resource (changes if resource changes) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 48
Client Caching A cache is a local copy of information obtained from some other source Most web browsers use cache to store requested resources so that subsequent requests to the same resource will not necessarily require an HTTP request/response Ex: icon appearing multiple times in a Web page Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 49
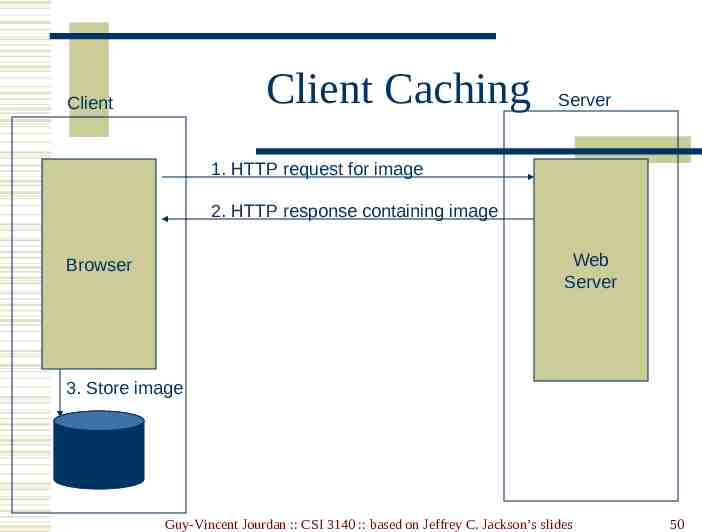
Client Caching Client Server 1. HTTP request for image 2. HTTP response containing image Web Server Browser 3. Store image Cache Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 50
Client Browser I need that image again Client Caching Server Web Server Cache Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 51
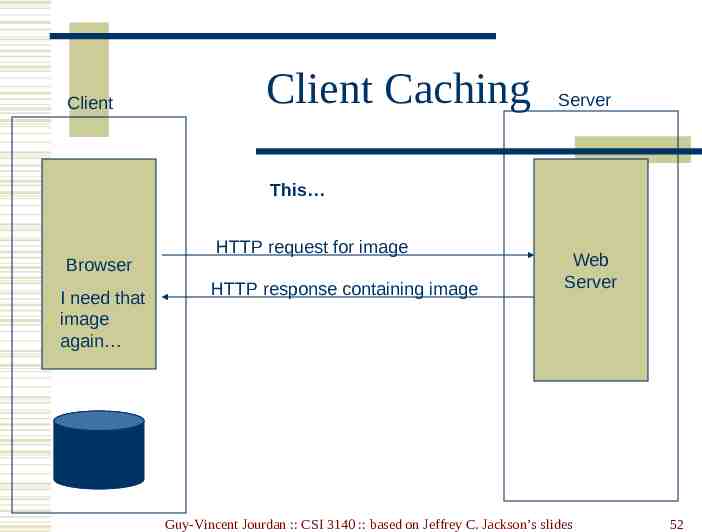
Client Client Caching Server This Browser I need that image again HTTP request for image HTTP response containing image Web Server Cache Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 52
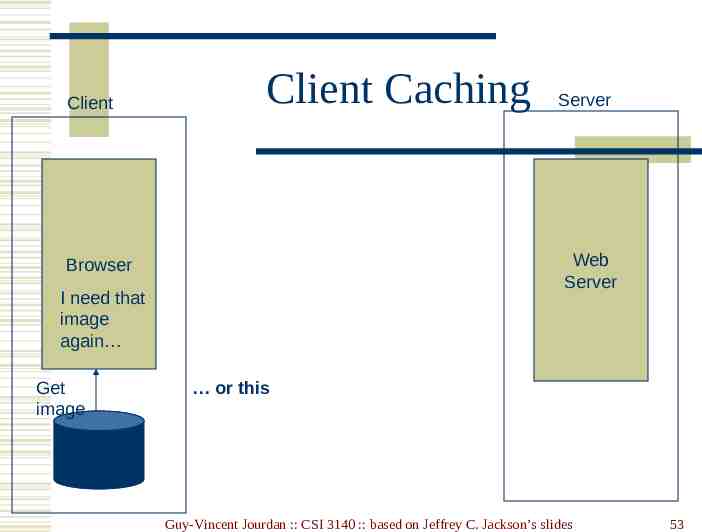
Client Client Caching Web Server Browser I need that image again Get image Server or this Cache Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 53
Client Caching Cache advantages (Much) faster than HTTP request/response Less network traffic Less load on server Cache disadvantage Cached copy of resource may be invalid (inconsistent with remote version) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 54
Client Caching Validating cached resource: Send HTTP HEAD request and check LastModified or ETag header in response Compare current date/time with Expires header sent in response containing resource If no Expires header was sent, use heuristic algorithm to estimate value for Expires Ex: Expires 0.01 * (Date – Last-Modified) Date Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 55
Character Sets Every document is represented by a string of integer values (code points) The mapping from code points to characters is defined by a character set Some header fields have character set values: Accept-Charset: request header listing character sets that the client can recognize Ex: accept-charset: ISO-8859-1,utf-8;q 0.7,*;q 0.5 Content-Type: can include character set used to represent the body of the HTTP message Ex: Content-Type: text/html; charset UTF-8 Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 56
Character Sets Technically, many “character sets” are actually character encodings An encoding represents code points using variablelength byte strings Most common examples are Unicode-based encodings UTF-8 and UTF-16 IANA maintains complete list of Internetrecognized character sets/encodings Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 57
Character Sets Typical US PC produces ASCII documents US-ASCII character set can be used for such documents, but is not recommended UTF-8 and ISO-8859-1 are supersets of US-ASCII and provide international compatibility UTF-8 can represent all ASCII characters using a single byte each and arbitrary Unicode characters using up to 4 bytes each ISO-8859-1 is 1-byte code that has many characters common in Western European languages, such as é Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 58
Web Clients Many possible web clients: Text-only “browser” (lynx) Mobile phones Robots (software-only clients, e.g., search engine “crawlers”) etc. We will focus on traditional web browsers Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 59
Web Browsers First graphical browser running on generalpurpose platforms: Mosaic (1993) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 60
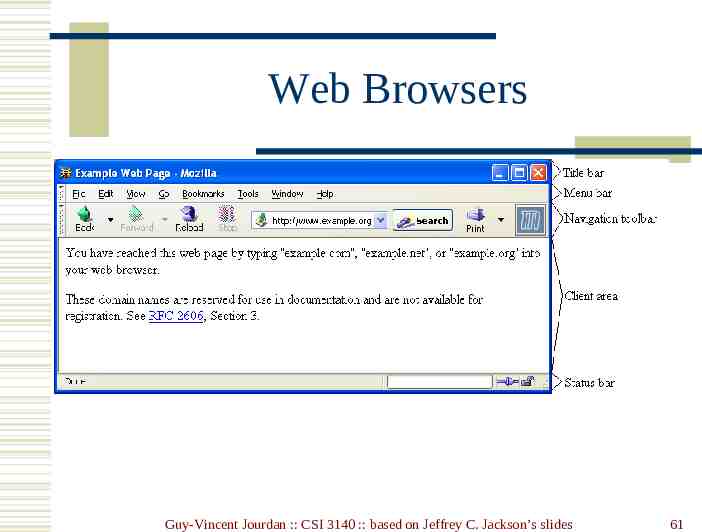
Web Browsers Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 61
Web Browsers Primary tasks: Convert web addresses (URL’s) to HTTP requests Communicate with web servers via HTTP Render (appropriately display) documents returned by a server Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 62
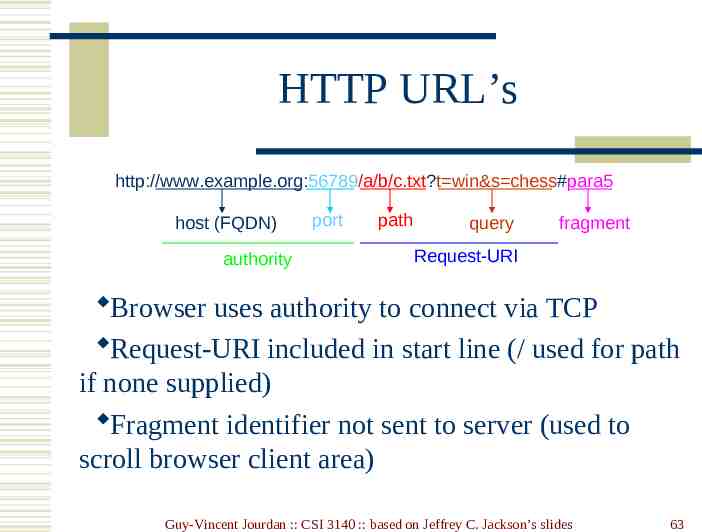
HTTP URL’s http://www.example.org:56789/a/b/c.txt?t win&s chess#para5 host (FQDN) authority port path query fragment Request-URI Browser uses authority to connect via TCP Request-URI included in start line (/ used for path if none supplied) Fragment identifier not sent to server (used to scroll browser client area) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 63
Web Browsers Standard features Save web page to disk Find string in page Fill forms automatically (passwords, CC numbers, ) Set preferences (language, character set, cache and HTTP parameters) Modify display style (e.g., increase font sizes) Display raw HTML and HTTP header info (e.g., Last-Modified) Choose browser themes (skins) View history of web addresses visited Bookmark favorite pages for easy return Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 64
Web Browsers Additional functionality: Execution of scripts (e.g., drop-down menus) Event handling (e.g., mouse clicks) GUI for controls (e.g., buttons) Secure communication with servers Display of non-HTML documents (e.g., PDF) via plug-ins Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 65
Web Servers Basic functionality: Receive HTTP request via TCP Map Host header to specific virtual host (one of many host names sharing an IP address) Map Request-URI to specific resource associated with the virtual host File: Return file in HTTP response Program: Run program and return output in HTTP response Map type of resource to appropriate MIME type and use to set Content-Type header in HTTP response Log information about the request and response Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 66
Web Servers httpd: UIUC, primary Web server c. 1995 Apache: “A patchy” version of httpd, now the most popular server (esp. on Linux platforms) IIS: Microsoft Internet Information Server Tomcat: Java-based Provides container (Catalina) for running Java servlets (HTML-generating programs) as back-end to Apache or IIS Can run stand-alone using Coyote HTTP front-end Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 67
Web Servers Some Coyote communication parameters: Allowed/blocked IP addresses Max. simultaneous active TCP connections Max. queued TCP connection requests “Keep-alive” time for inactive TCP connections Modify parameters to tune server performance Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 68
Web Servers Some Catalina container parameters: Virtual host names and associated ports Logging preferences Mapping from Request-URI’s to server resources Password protection of resources Use of server-side caching Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 69
Tomcat Web Server HTML-based server administration Browse to http://localhost:8080 and click on Server Administration link localhost is a special host name that means “this machine” Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 70
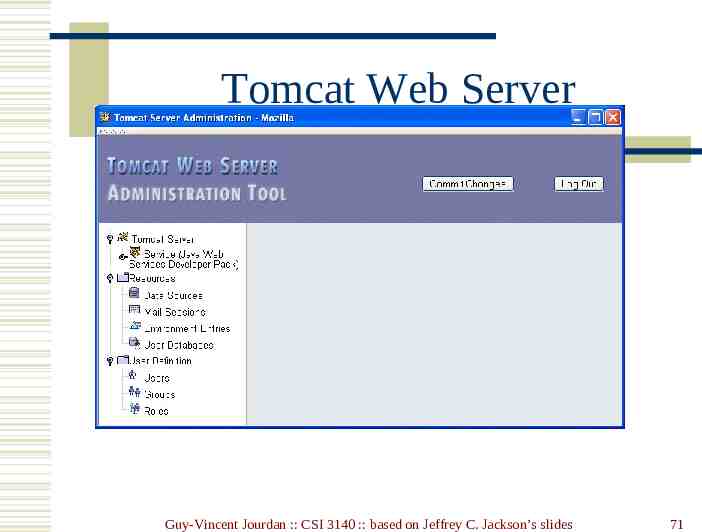
Tomcat Web Server Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 71
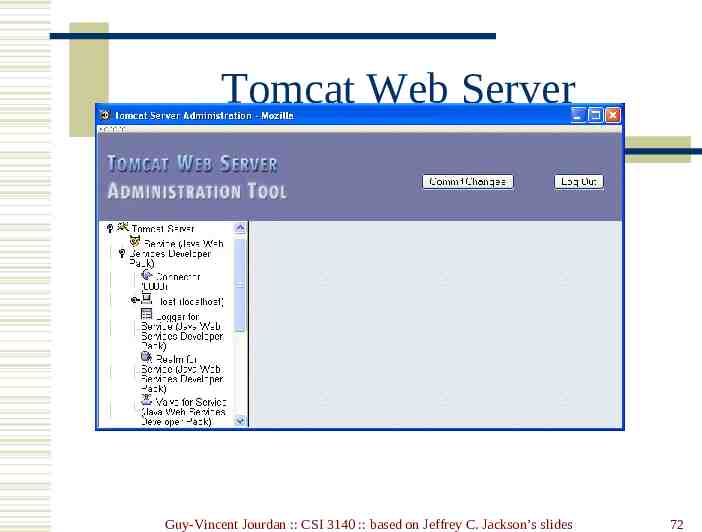
Tomcat Web Server Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 72
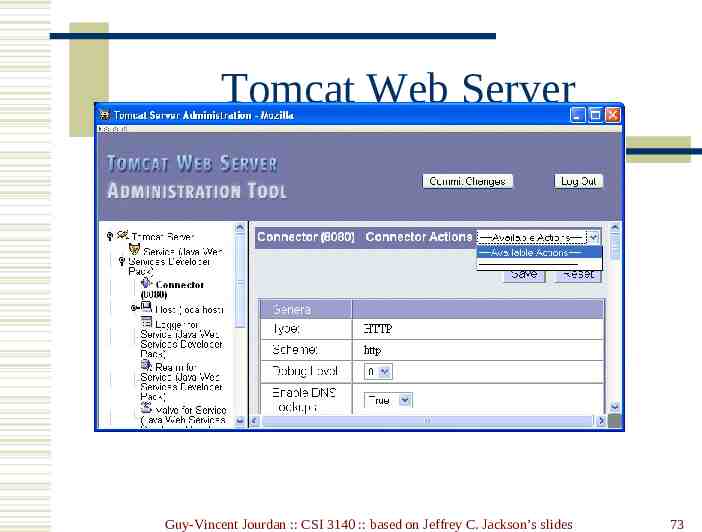
Tomcat Web Server Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 73
Tomcat Web Server Some Connector fields: Port Number: port “owned” by this connector Max Threads: max connections processed simultaneously Connection Timeout: keep-alive time Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 74
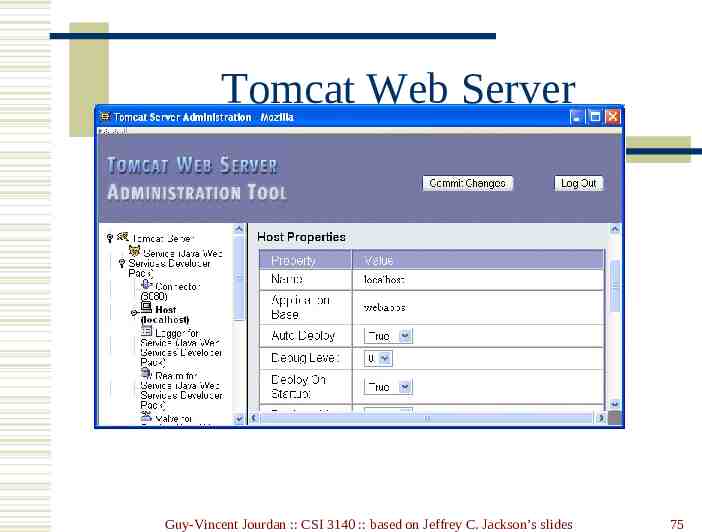
Tomcat Web Server Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 75
Tomcat Web Server Each Host is a virtual host (can have multiple per Connector) Some fields: Host: localhost or a fully qualified domain name Application Base: directory (may be path relative to JWSDP installation directory) containing resources associated with this Host Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 76
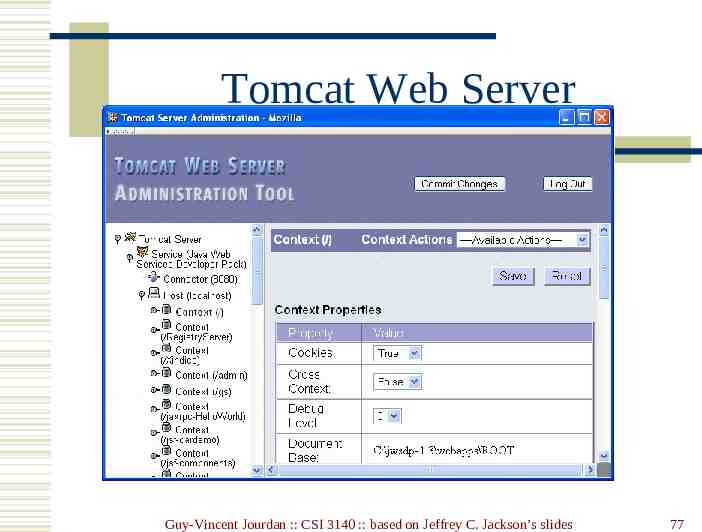
Tomcat Web Server Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 77
Tomcat Web Server Context provides mapping from Request-URI path to a web application Document Base field is directory (possibly relative to Application Base) that contains resources for this web application For this example, browsing to http://localhost:8080/ returns resource from c:\jwsdp-1.3\webapps\ROOT Returns index.html (standard welcome file) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 78
Tomcat Web Server Access log records HTTP requests Parameters set using AccessLogValve Default location: logs/access log.* under JWSDP installation directory Example “common” log format entry (one line): www.example.org - admin [20/Jul/2005:08:03:22 -0500] "GET /admin/frameset.jsp HTTP/1.1" 200 920 Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 79
Tomcat Web Server Other logs provided by default in JWSDP: Message log messages sent to log service by web applications or Tomcat itself logs/jwsdp log.*: default message log logs/localhost admin log.*: message log for web apps within /admin context System.out and System.err output (exception traces often found here): logs/launcher.server.log Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 80
Tomcat Web Server Access control: Password protection (e.g., admin pages) Users and roles defined in conf/tomcat-users.xml Deny access to machines Useful for denying access to certain users by denying access from the machines they use List of denied machines maintained in RemoteHostValve (deny by host name) or RemoteAddressValve (deny by IP address) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 81
Secure Servers Since HTTP messages typically travel over a public network, private information (such as credit card numbers) should be encrypted to prevent eavesdropping https URL scheme tells browser to use encryption Common encryption standards: Secure Socket Layer (SSL) Transport Layer Security (TLS) Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 82
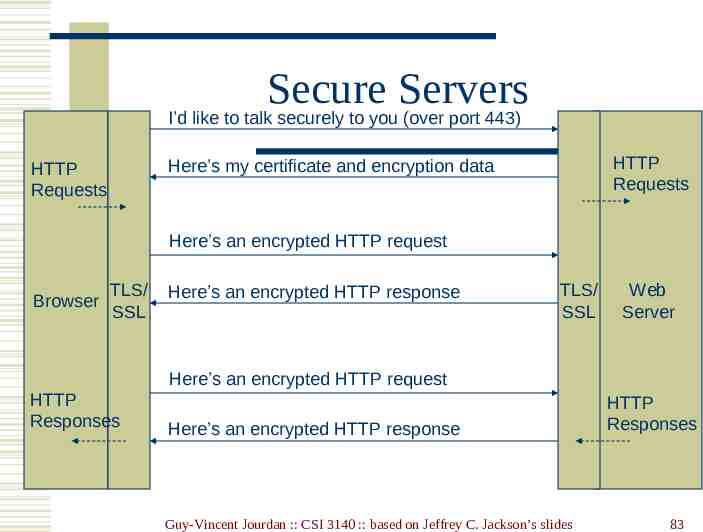
Secure Servers I’d like to talk securely to you (over port 443) HTTP Requests Here’s my certificate and encryption data HTTP Requests Here’s an encrypted HTTP request Browser TLS/ SSL Here’s an encrypted HTTP response TLS/ SSL Web Server Here’s an encrypted HTTP request HTTP Responses Here’s an encrypted HTTP response Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides HTTP Responses 83
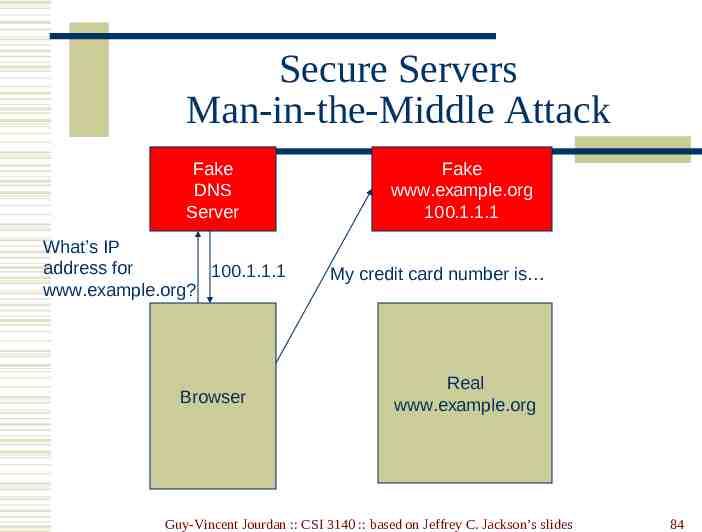
Secure Servers Man-in-the-Middle Attack Fake DNS Server What’s IP address for 100.1.1.1 www.example.org? Browser Fake www.example.org 100.1.1.1 My credit card number is Real www.example.org Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 84
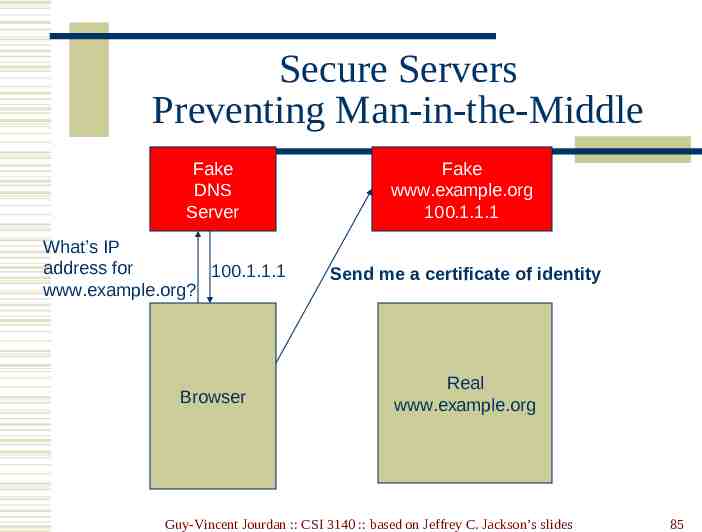
Secure Servers Preventing Man-in-the-Middle Fake DNS Server What’s IP address for 100.1.1.1 www.example.org? Browser Fake www.example.org 100.1.1.1 Send me a certificate of identity Real www.example.org Guy-Vincent Jourdan :: CSI 3140 :: based on Jeffrey C. Jackson’s slides 85