Understanding Android Security Yinshu Wu William Enck, Machigar
23 Slides807.50 KB
Understanding Android Security Yinshu Wu William Enck, Machigar Ongtang, and PatrickMcDaniel Pennsylvania State University
Outline I. II. III. IV. V. Introduction Android Applications Security Enforcement Security Refinements Lessons in Defining Policy
Introduction Next generation open operation system will be developed on small mobile devices. Android (Google) -a widely anticipated open source operating system for mobile devices -it provide base operation system, application middleware layer, Java software development kit and a collection of system applications.
Introduction (cont.) Feature of Android 1. Doesn’t support applications developed for other platforms 2. Restricts application interaction to its special APIs by running each application as its own user identity 3. Uses a simple permission label assignment model to restrict access to resources and other applications
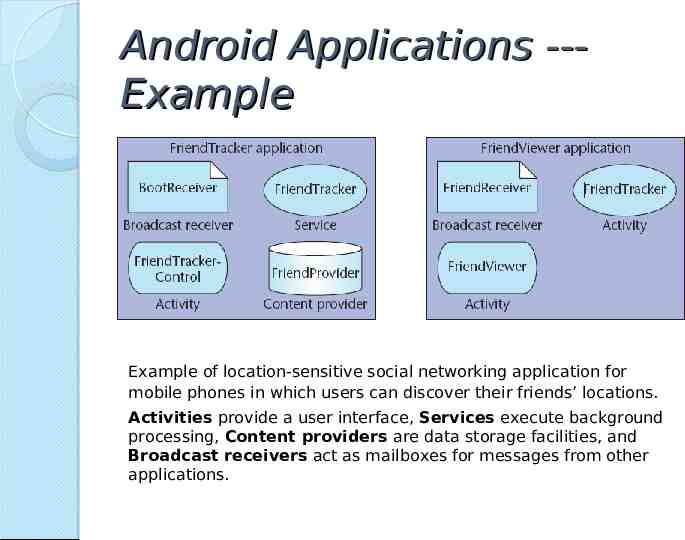
Android Applications --Example Example of location-sensitive social networking application for mobile phones in which users can discover their friends’ locations. Activities provide a user interface, Services execute background processing, Content providers are data storage facilities, and Broadcast receivers act as mailboxes for messages from other applications.
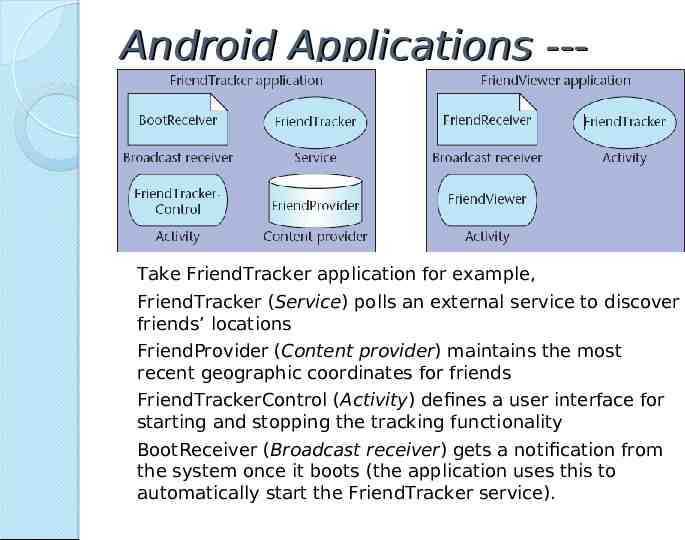
Android Applications --Example Application(cont.) Take FriendTracker application for example, FriendTracker (Service) polls an external service to discover friends’ locations FriendProvider (Content provider) maintains the most recent geographic coordinates for friends FriendTrackerControl (Activity) defines a user interface for starting and stopping the tracking functionality BootReceiver (Broadcast receiver) gets a notification from the system once it boots (the application uses this to automatically start the FriendTracker service).
Android Applications--Component Interaction Intent - is the primary mechanism for component interaction, which is simply a message object containing a destination component address and data Action - the process of intercomponents communication
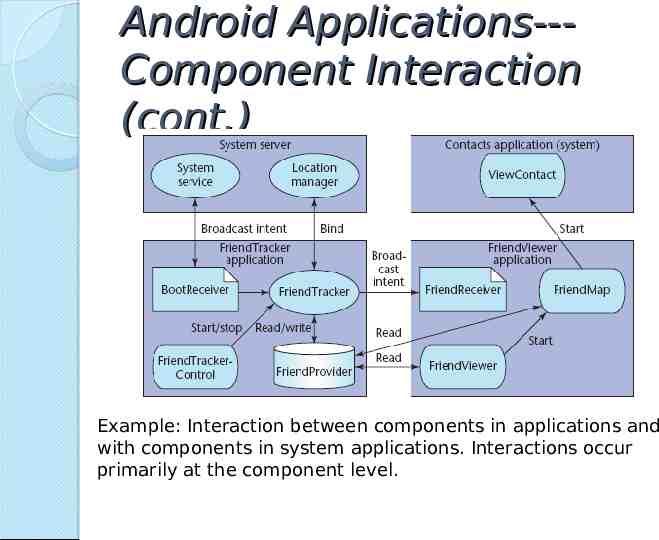
Android Applications--Component Interaction (cont.) Example: Interaction between components in applications and with components in system applications. Interactions occur primarily at the component level.
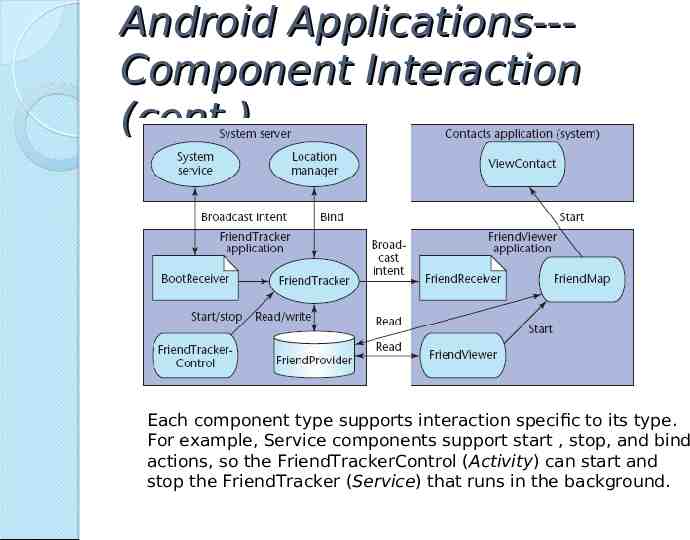
Android Applications--Component Interaction (cont.) Each component type supports interaction specific to its type. For example, Service components support start , stop, and bind actions, so the FriendTrackerControl (Activity) can start and stop the FriendTracker (Service) that runs in the background.
Security Enforcement Android protect application at system level and at the Inter-component communication (ICC) level. This article focus on the ICC level enforcement. Each application runs as a unique user identity, which lets Android limit the potential damage of programming flaws.
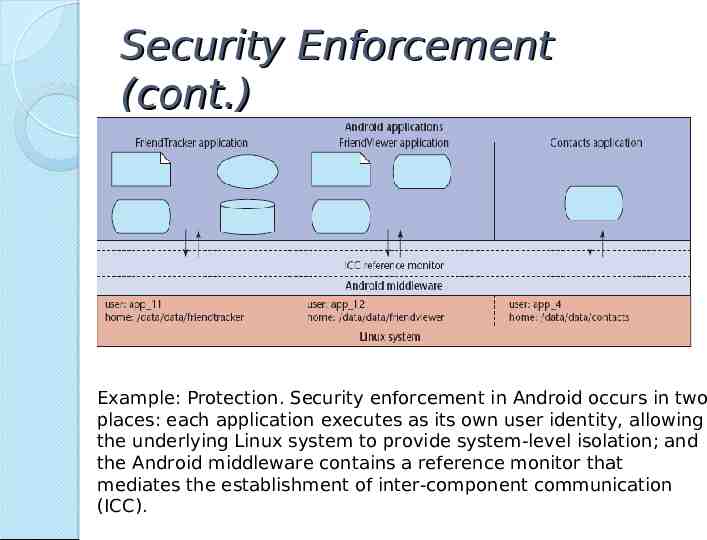
Security Enforcement (cont.) Example: Protection. Security enforcement in Android occurs in two places: each application executes as its own user identity, allowing the underlying Linux system to provide system-level isolation; and the Android middleware contains a reference monitor that mediates the establishment of inter-component communication (ICC).
Security Enforcement (cont.) Core idea of Android security enforcement labels assignment to applications and components A reference monitor provides mandatory access control (MAC) enforcement of how applications access components. Access to each component is restricted by assigning it an access permission label; applications are assigned collections of permission labels. When a component initiates ICC, the reference monitor looks at the permission labels assigned to its containing application and— if the target component’s access permission label is in that collection— allows ICC establishment to proceed.
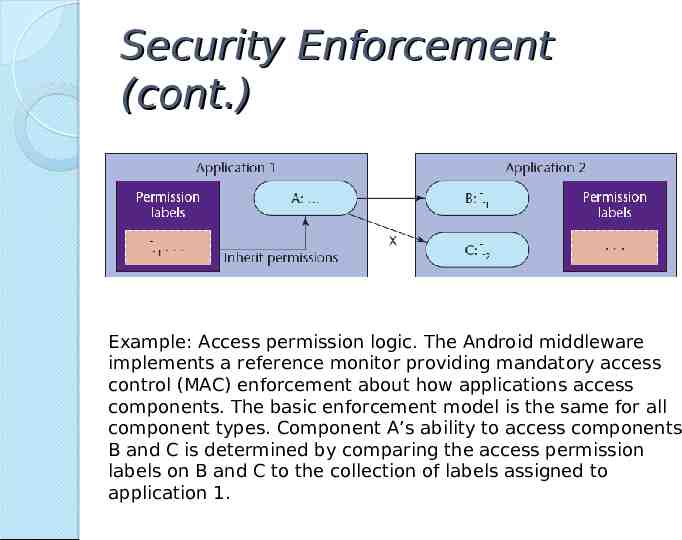
Security Enforcement (cont.) Example: Access permission logic. The Android middleware implements a reference monitor providing mandatory access control (MAC) enforcement about how applications access components. The basic enforcement model is the same for all component types. Component A’s ability to access components B and C is determined by comparing the access permission labels on B and C to the collection of labels assigned to application 1.
Security Enforcement Conclusion Assigning permission labels to an application specifies its protection domain. Assigning permissions to the components in an application specifies an access policy to protect its resources. Android’s policy enforcement is mandatory, all permission labels are set at install time and can’t change until the application is reinstalled. Android’s permission label model only restricts access to components and doesn’t currently provide information flow guarantees.
Security Refinements --Public vs. Private Components Applications often contain components that another application should never access. For example, component related to password storing. The solution is to define private component. This significantly reduces the attack surface for many applications.
Security Refinements --Implicitly Open Components At development time, if the decision of access permission is unclear, The developer can permit the functionality by not assigning an access permission to it. If a public component doesn’t explicitly have an access permission listed in its manifest definition, Android permits any application to access it.
Security Refinements --Broadcast Intent Permissions Sending the unprotected intent is a privacy risk. Android API for broadcasting intents optionally allows the developer to specify a permission label to restrict access to the intent object.
Security Refinements --Content Provider Permissions If the developer want his application to be the only one to update the contents but for other applications to be able to read them. Android allows such a security policy assigning read or write permissions.
Security Refinements --Protected APIs Not all system resources(for example, network) are accessed through components—instead, Android provides direct API access. Android protects these sensitive APIs with additional permission label checks: an application must declare a corresponding permission label in its manifest file to use them.
Security Refinements --Permission Protection Levels The permission protection levels provide a means of controlling how developers assign permission labels. Signature permissions ensure that only the framework developer can use the specific functionality (only Google applications can directly interface the telephony API, for example).
Security Refinements --Pending Intents Pending intent - a developer defines an intent object to perform an action. However, instead of performing the action, the developer passes the intent to a special method that creates a PendingIntent object corresponding to the desired action. The PendingIntent object is simply a reference pointer that can pass to another application. Pending intents allow applications included with the framework to integrate better with third-party applications.
Lessons in Defining Policy Android security policy begins with a relatively easy-to-understand MAC enforcement model, but the number and subtlety of refinements make it difficult to discover an application’s policy. The label itself is merely a text string, but its assignment to an application provides access to potentially limitless resources.
Thanks!