BlackHat Briefings July 12 2001 Computer Forensics: A Critical
84 Slides3.28 MB
BlackHat Briefings July 12 2001 Computer Forensics: A Critical Process in Your Incident Response Plan Version 2.0
Gregory S. Miles, Ph.D. Director – JAWZ Cyber Crime Unit COO – Security Horizon Inc. Information Technology – 14 Years Information Security – 10 Years e-mail: [email protected] [email protected] Web: www.jawzinc.com www.securityhorizon.com Version 2.0
Agenda Incident Response Overview Computer Forensics Defined Contemporary Issues in Computer Forensics Forensic Process Forensic Tools Forensic Problems The Future of Computer Forensics Version 2.0
Incident Response Version 2.0 4
Incident Response – Why is it Critical? Resolve the problem – Find out what happened – How it happened – Who did it Create a record of the incident for later use Create a record to observe trends Create a record to improve processes Avoid confusion Version 2.0
Elements of Incident Response Preparation Identification Containment Eradication Recovery Follow-up Version 2.0
Preparation Without adequate preparation, it is extremely likely that response efforts to an incident will be disorganized and that there will be considerable confusion among personnel. Preparation limits the potential for damage by ensuring response actions are known and coordinated. Version 2.0
Identification The process of determining whether or not an incident has occurred and the nature of an incident. Identification may occur through the use of automated network intrusion equipment or by a user or SA. Identification is a difficult process. Noticing the symptoms of an incident is often difficult. There are many false positives. However, noticing an anomaly should drive the observer to investigate further. Version 2.0
Who can identify an Incident Users – My system is slow, my mail is missing, my files have changed System support personnel – servers locked up, files missing, accounts add/deleted, weird stuff happening , anomalies in the logs Intrusion Detection Systems and Firewalls – Automatically ID violations to policies Version 2.0
Possible Incident Classifications Unauthorized Privileged (root) Access – Access gained to a system and the use of root privileges without authorization. Unauthorized Limited (user) Access – Access gained to a system and the use of user privileges without authorization. Unauthorized Unsuccessful Attempted Access – Repeated attempt to gain access as root or user on the same host, service, or system with a certain number of connections from the same source. Version 2.0 10
Possible Incident Classifications (cont.) Unauthorized Probe – Any attempt to gather information about a system or user on-line by scanning a site and accessing ports through operating system vulnerabilities. Poor Security Practices – Bad passwords, direct privileged logins, etc, which are collected from network monitor systems. Denial of Service (DOS) Attacks – Any action that preempts or degrades performance of a system or network affecting the mission, business, or function of an organization. Version 2.0 11
Possible Incident Classifications (cont.) Malicious Logic – Self-replicating software that is viral in nature; is disseminated by attaching to or mimicking authorized computer system files; or acts as a trojan horse, worm, malicious scripting, or a logic bomb. Usually hidden and some may replicate. Effects can range from simple monitoring of traffic to complicated automated backdoor with full system rights. Version 2.0 12
Possible Incident Classifications (cont.) Hardware/Software Failure – Nonmalicious failure of HW or SW assets. Infrastructure Failure – Non-malicious failure of supporting infrastructure to include power failure, natural disasters, forced evacuation, and service providers failure to deliver services. Unauthorized Utilization of Services – This can include game play, relaying mail without approval, creating dial-up access, use organizational equipment for personal gain, and personal servers on the network. Version 2.0 13
Containment The process of limiting the scope and magnitude of an incident. As soon as it is recognized that an incident has occurred or is occurring, steps should immediately be taken to contain the incident. Version 2.0 14
Containment - Example Incidents involving using malicious code are common, and since malicious code incidents can spread rapidly, massive destruction and compromise of information is possible. It is not uncommon to find every workstation connected to a LAN infected when there is a virus outbreak. – Internet Worm of 1988 attacked 6,000 computers in the U.S. in one day. – LoveBug Virus affected over 10Million computers with damage estimated between 2.5B- 10B US – Kournikova worm affects still being analyzed Version 2.0 15
Eradication The process of removing the cause of the incident. – For a virus – anti-virus software is best – For a network may involve block/filter IP address at the router/firewall – Ideally, but difficult, best eradicated by bringing the perpetrators into legal custody and convicting them in a court of law. Version 2.0 16
Recovery The process of restoring a system to its normal operating status – Unsuccessful incidents – assure system operation and data not affected – Complex and/or successful incidents – May require complete restoration from known clean system backups. Essential to assure the backups integrity and to verify restore operation was successful Version 2.0 17
Follow-Up Critical Helps to improve incident handling procedures Address efforts to prosecute perpetrators Activities Include: – – – – Version 2.0 Analyze the Incident and the Response Analyze the Cost of the Incident Prepare a Report Revise Policies and Procedures 18

Computer Forensics Version 2.0 19
What is Computer Forensics? Computer Forensics can be defined simply, as a process of applying scientific and analytical techniques to computer Operating Systems and File Structures in determining the potential for Legal Evidence. Version 2.0 20
Why is Evidence important? In the legal world, Evidence is EVERYTHING. Evidence is used to establish facts. The Forensic Examiner is not biased. Version 2.0 21
Who needs Computer Forensics? The Victim! Law Enforcement Insurance Carriers Ultimately the Legal System Version 2.0 22
Who are the Victims? Private Business Government Private Individuals Version 2.0 23

Version 2.0 24

Version 2.0 25

Version 2.0 26
Reasons for a Forensic Analysis ID the perpetrator. ID the method/vulnerability of the network that allowed the perpetrator to gain access into the system. Conduct a damage assessment of the victimized network. Preserve the Evidence for Judicial action. Version 2.0 27
Types of Computer Forensics Version 2.0 Disk Forensics Network Forensics E-mail Forensics Internet (Web) Forensics Source Code Forensics
Disk Forensics Disk forensics is the process of acquiring and analyzing the data stored on some form of physical storage media. – Includes the recovery of hidden and deleted data. – Includes file identification, which is the process used to identify who created a particular file or message. Melissa Virus Version 2.0 29
Network Forensics Network forensics is the process of examining network traffic. It includes: – After the fact analysis of transaction logs – Real-time analysis via network monitoring Sniffers Real-time tracing Version 2.0 30
E-mail Forensics E-mail forensics is the study of source and content of electronic mail as evidence. – It includes the process of identifying the actual sender and recipient of a message, the date and time it was sent, and where it was sent from. – E-mail has turned out to be the Achilles Heal for many individuals and organizations. – Many time issues of sexual harassment, racial and religious prejudice, or unauthorized activity are tied to e-mail. Version 2.0 31
Internet Forensics Internet or Web forensics is the process of piecing together where and when a user has been on the Internet. – For example, it is used to determine whether the download of pornography was accidental or not. Version 2.0 32
Source Code Forensics Source code forensics is used to determine software ownership or software liability issues. – It is not merely a review of the actual source code. – It is an examination of the entire development process, including development procedures, review of developer time sheets, documentation review and the review of source code revision practices. Version 2.0 33
Technological Progress The Population is More Computer Literate The World is Networked, Yet Users Can Retain a Sense of Anonymity The Use of Encryption is Becoming Common Network Bandwidth is Increasing while Cost is Decreasing Disks are Less Expensive and have Higher Capacities – More Data Available On-Line Version 2.0 34
Technological Progress Albert Einstein said “Technological progress is like an axe in the hands of a pathological criminal.” Version 2.0 35
Technological Progress Computers are Tools and Targets – Instrumentality – Data Repository Many Criminals Are Using Computers in the Normal Course of Business Computer Crime Today – – – – Version 2.0 Crime Without Punishment Media Sensationalism Public Apathy Easy to Commit 36
What is Cyber Crime? A crime in which technology plays an important, and often a necessary, part. – The computer is: the target of an attack the tool used in an attack used to store data related to criminal activity Version 2.0 37
Types of Cyber Crime Version 2.0 Unauthorized Access Denial of Service Extortion Theft Sabotage Espionage Computer Fraud Embezzlement Copyright Violation Forgery and Counterfeiting Internet Fraud – “Imposter Sites” SEC Fraud and Stock Manipulation Child Pornography Stalking & Harassment Credit Card Fraud & Skimming 38
Contemporary Issues in Computer Forensics Criminal Justice System is not Prepared to Handle High-Tech Crime – Shortage of Trained Investigators & Analysts – Lack of Forensic Standards Too Much Data! – Large Disk Drives and Disk Arrays – High Speed Network Connections Issues Relating to Time Version 2.0 39
Contemporary Issues in Computer Forensics Evidence Collection and Examination Must not Violate the following: – 4th Amendment – Privacy Protection Act – Electronic Communications Privacy Act Version 2.0 40
Forensics Process Preparation Protection Imaging Examination Documentation Version 2.0 41
Preparation Confirm the authority to conduct analysis/search of media. Verify the purpose of the analysis and the clearly defined desired results. Ensure that sterile media is available and utilized for imaging. (ie.Free of virus, Nonessential files, and verified before use.) Ensure that all software tools utilized for the analysis are tested and widely accepted for use in the forensics community. Version 2.0 42
Legal Overview Employer Searches in Private-Sector Workplaces Warrantless workplace searches by private employers rarely violate the Fourth Amendment. So long as the employer is not acting as an instrument or agent of the Government at the time of the search, the search is a private search and the Fourth Amendment does not apply. See Skinner v. Railway Labor Executives’ Ass’n, 489 U.S. 602, 614 (1989). Version 2.0 Consult with your Legal 43
Protection Protect the integrity of the evidence. Maintain control until final disposition. Prior to Booting target computer, DISCONNECT HDD and verify CMOS. When Booting a machine for Analysis, utilize HD Lock software. Version 2.0 44
Imaging Utilize disk “imaging” software to make an exact image of the target media. Verify the image. When conducting an analysis of target media, utilize the restored image of the target media; never utilize the actual target media. Version 2.0 45
Examination The Operating System Services Applications/processes Hardware LOGFILES! System, Security, and Application File System Version 2.0 46
Examination (Cont) Deleted/Hidden Files/NTFS Streams Software Encryption Software Published Shares/Permissions Password Files SIDS Network Architecture/Trusted Relationships Version 2.0 47
Off-Site Storage “X-Drives” FTP Links FTP Logs Shares on internal networks Version 2.0 48
Documentation Document EVERYTHING Reason for Examination “The Scene” Utilize Screen Capture/Copy Suspected files All apps for Analysis/apps on Examined system. Version 2.0 49
Forensic Tools Forensic Tool Kit Forensic Computer System Forensic Software Version 2.0

Forensic Tool Kit Version 2.0 51
Forensic System Hardware Main Systems – Pentium-based Computer – Multiple O/S UNIX, Windows, MAC Media Options Removable Media (REM-KIT) Disk Imaging Hardware – Image MASSter 500 & 1000 Static-Dissipative Grounding Kit w/Wrist Strap UPS Version 2.0 52
Media Options Your Forensic System should have plenty of room for expansion and external media. This is usually best supported by SCSI Systems. Version 2.0 53
Media Options Internal Hard Disk Tape Media – QIC Tape Drive – Travan Tape Drive – DAT Optical Media – CD-ROM – CD-Writer – DVD Version 2.0 54
Removable Media Hard Drives ZIP Drives Jazz Drives PCMCIA Flash Disks Version 2.0 55
Disk Imaging Hardware Supports IDE & SCSI Sector by Sector Copy – DOS, Windows 3.1, – Windows 95, NT, SCO, – UNIX, OS/2 & Mac O/S Full Read/Write Verification & Reporting Logging Capability No Writing to Master Disk Version 2.0 56
Forensic Software Clean Operating System(s) Disk Image Backup Software Search & Recovery Utilities File Viewing Utilities Cracking Software Archive & Compression Utilities Version 2.0 57
Validate Software Determine Functionality – Verify operation – Identify limitations – Identify bugs Court Presentation – Testify from own experience Version 2.0 58
Disk Imaging Software Bit Level Copy of the Disk, not File Level Not Operating System Dependent Must have Logging or Error Reporting Must Copy Deleted Files and Slackspace Tools – EnCase – SafeBack – SnapBack Version 2.0 59
Search Utilities Forensic Software – EnCase – The Coroners Tool Kit File System Utilities – DOS, Windows, NT, UNIX Norton Utilities Version 2.0 60
File Viewing Utilities Quick View Plus Drag & View Thumbs Plus Version 2.0 61
Forensic Analysis Computer Forensics – – – – Lock the Disk Create an Image of the Disk(s) File System Authentication List Disk Directories and File Systems – Locate Hidden or Obscured Data – Cluster Analysis Version 2.0
File System Authentication Integrity of data related to any seizure is essential Message Digest - One-way Hash Algorithm – CRC32 (32 bits) – MD5 (128 bits) – SHA (160 bits) Create MD for system directories and files Version 2.0 63
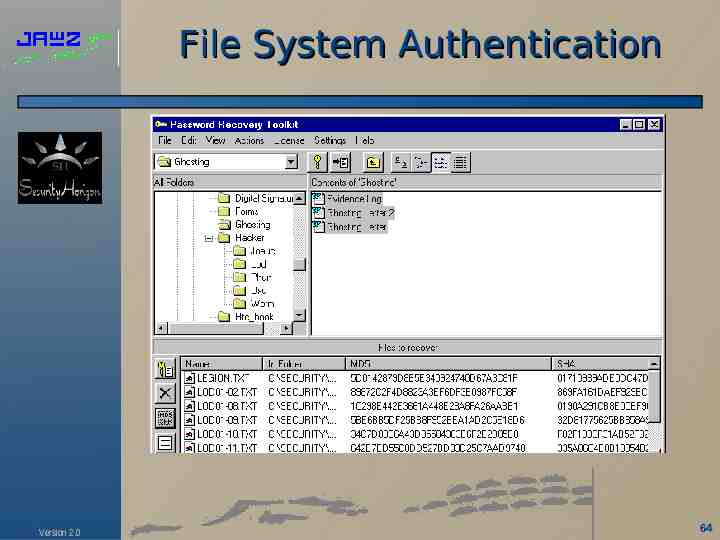
File System Authentication Version 2.0 64
List Directories and Files Create Hierarchical Directory Listing (Tree) Identify Suspect Files Inventory All Files on the Disk Search Communications Programs Registry Files Last Files Accessed Document Association Version 2.0 65
Identify Suspect Files File Name Search based on Case Characteristics Key Word Search based on Case Characteristics Modified File Extensions that Do Not Match the File Type Hidden or Deleted Files Version 2.0 66
Hidden & Obscure Data Hidden File Attributes Hidden Directories Temporary Directories Deleted Files Slack Space Unallocated Space Swap Space Steganography Version 2.0 67
Steganography The Art of Hiding Communications While Encryption Conceals the Data, Steganography Denies the Data Exists Files Can Be Hidden within an Image Disguising Data as Innocent Text Version 2.0 68
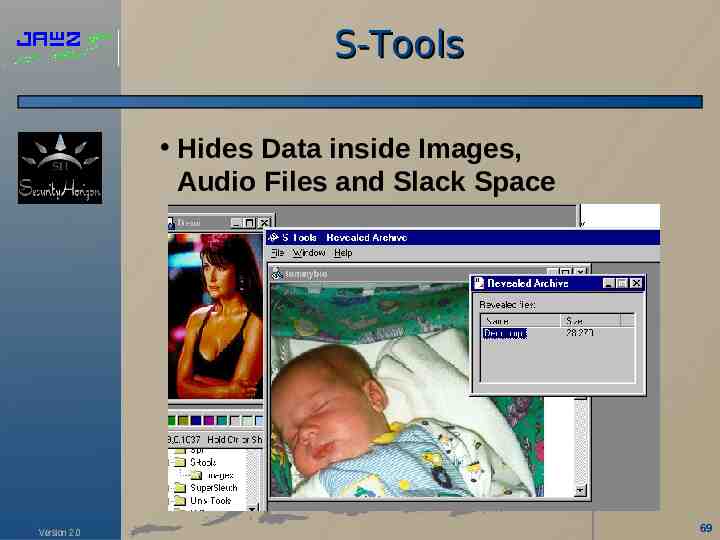
S-Tools Hides Data inside Images, Audio Files and Slack Space Version 2.0 69
Ghosting White letters on a white background, or black letters on a black background Version 2.0 70
Ghosting White letters on a white background, or black letters on a black background. Version 2.0 71
Cluster Analysis Cluster Analysis Criteria – Content, Location and Condition Identifies System Usage & History – Initial Load of the System – Defragmentation “Repacks” data files w/o Changing Date/Times – System Wipes and Reloads All Slack Space and Unallocated Blocks set to Zero All Date/Times close to the same Version 2.0 72
Analysis Problems Searching Access Controlled Systems Virus Infection Formatted Disk Corrupted Disk DiskWipe or Degaussed Media Defragmented Disk Cluster Boundaries Evidence Eliminator Version 2.0 73
Evidence Protection Transparent Static Shielding Bags – Provides shielding from electrostatic discharge by safely enveloping static sensitive devices in a humidity-independent Faraday cage. The nickel shielding layer creates a Faraday type shield. Meets MIL-B81705 and DoD-STD-1686A Foam-Filled Disk Transport Box EMF Warning Labels Version 2.0 74
Evidence Protection Version 2.0 75
Network Forensics Analyze Packet Traces – Establish a Sequence of Events – Goal is Identify the Intruder Tools – Network Sniffer – System Logs – NTSC Adapter Version 2.0 76
Network Forensics IP Spoofing Hijacking Password Attacks – Social Engineering – Cracking Passwords – Sniffers Distributed-Coordinated Attacks Identity Concealed by Connection Laundering Version 2.0 77
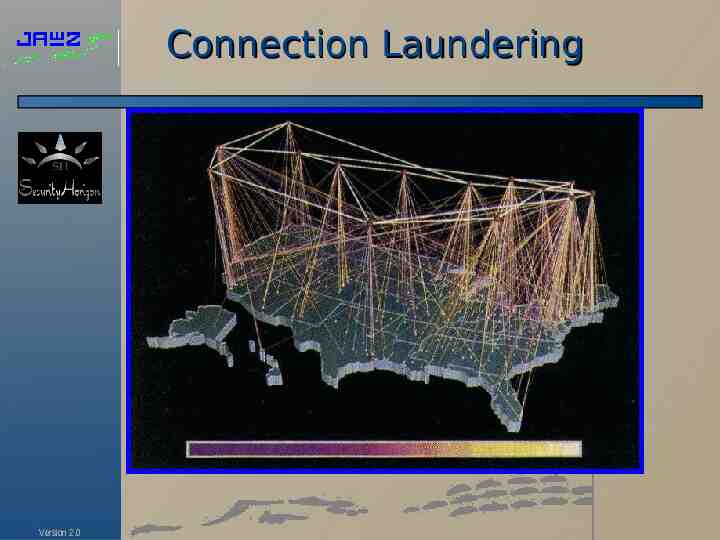
Connection Laundering Version 2.0
E-mail Forensics E-mail Usage in 2000 – 108 Million E-mail Subscribers – 25.2 Billion Message Daily E-mail is a asynchronous communications mechanisms that allows venting. People have a tendency to include more in an e-mail message than they would say in person of over the phone. E-mail Spoofing Version 2.0 79
E-mail Spoofing Requires Only: – Mail Relay Server – Knowledge of Mail Commands Version 2.0 telnet relay server helo mail from: [email protected] rcpt to: [email protected] Data message 80
The Future Forensics Crimes and Methods to Hide Crimes are becoming more Sophisticated, thus Investigators and Analyst must become more Technical – Specialist are Needed – More Training is needed in both the Public and Private Sectors Encryption will Continue to be an Issue, but Only Time will Tell Version 2.0 81
The Future Forensics Forensic Tools – Must Become Automated – Forensic Search Engines Must include Fuzzy Logic and Intelligence to handle Cluster Boundaries – UNIX Tools Must be Developed – Better Network Analysis Tools need to be Developed – Tools to Analyze Distributed Applications such as Java, COM, and DCOM will need to be Developed. Version 2.0 82
Conclusions Computer forensics is an integral function within incident response Processes are the most important aspects of computer forensics The future of cyber crime will lead to an increased need for computer forensic capabilities Version 2.0 83
Questions ? Version 2.0 84