Open Source Software (OSS or FLOSS) and the U.S. Department of
60 Slides579.00 KB
Open Source Software (OSS or FLOSS) and the U.S. Department of Defense (DoD) David A. Wheeler November 4, 2009 http://www.dwheeler.com/ This presentation contains the views of the author and does not indicate endorsement by IDA, the U.S. government, or the U.S. Department of Defense. 1
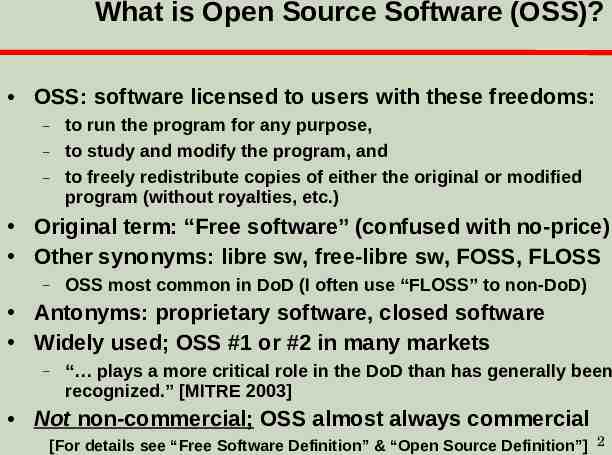
What is Open Source Software (OSS)? OSS: software licensed to users with these freedoms: – – – to run the program for any purpose, to study and modify the program, and to freely redistribute copies of either the original or modified program (without royalties, etc.) Original term: “Free software” (confused with no-price) Other synonyms: libre sw, free-libre sw, FOSS, FLOSS – OSS most common in DoD (I often use “FLOSS” to non-DoD) Antonyms: proprietary software, closed software Widely used; OSS #1 or #2 in many markets – “ plays a more critical role in the DoD than has generally been recognized.” [MITRE 2003] Not non-commercial; OSS almost always commercial [For details see “Free Software Definition” & “Open Source Definition”] 2
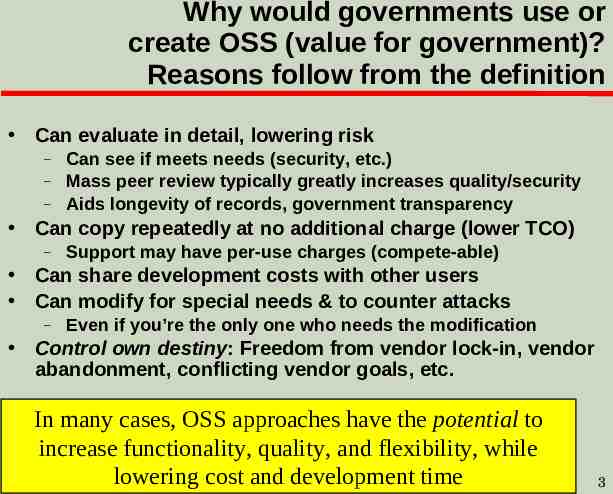
Why would governments use or create OSS (value for government)? Reasons follow from the definition Can evaluate in detail, lowering risk – – – Can see if meets needs (security, etc.) Mass peer review typically greatly increases quality/security Aids longevity of records, government transparency Can copy repeatedly at no additional charge (lower TCO) – Support may have per-use charges (compete-able) Can share development costs with other users Can modify for special needs & to counter attacks – Even if you’re the only one who needs the modification Control own destiny: Freedom from vendor lock-in, vendor abandonment, conflicting vendor goals, etc. In many cases, OSS approaches have the potential to increase functionality, quality, and flexibility, while lowering cost and development time 3
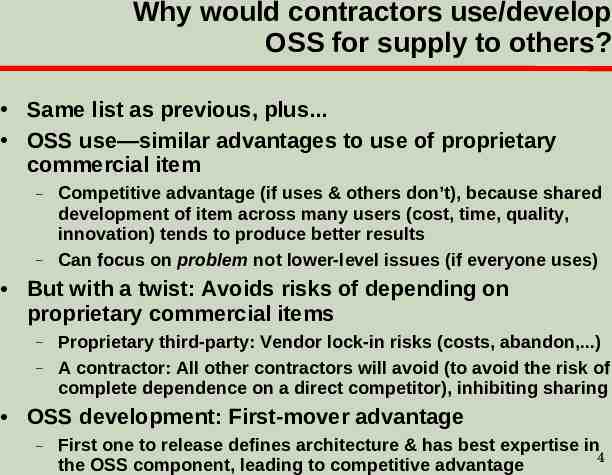
Why would contractors use/develop OSS for supply to others? Same list as previous, plus. OSS use—similar advantages to use of proprietary commercial item – – Competitive advantage (if uses & others don’t), because shared development of item across many users (cost, time, quality, innovation) tends to produce better results Can focus on problem not lower-level issues (if everyone uses) But with a twist: Avoids risks of depending on proprietary commercial items – – Proprietary third-party: Vendor lock-in risks (costs, abandon,.) A contractor: All other contractors will avoid (to avoid the risk of complete dependence on a direct competitor), inhibiting sharing OSS development: First-mover advantage – First one to release defines architecture & has best expertise in 4 the OSS component, leading to competitive advantage
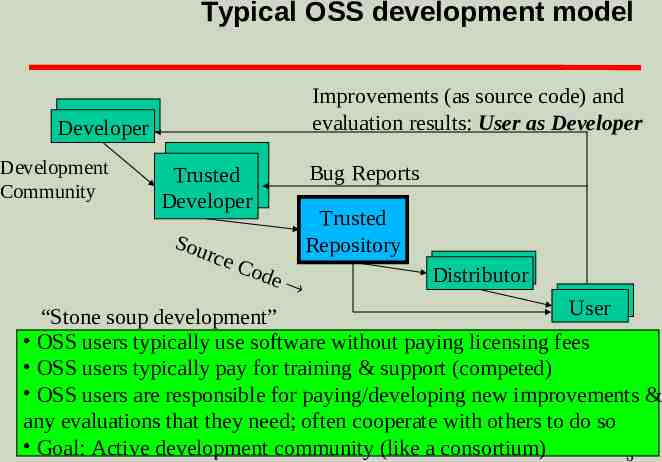
Typical OSS development model Improvements (as source code) and evaluation results: User as Developer Developer Development Community Bug Reports Trusted Developer Sou rc e Co Trusted Repository de Distributor User “Stone soup development” OSS users typically use software without paying licensing fees OSS users typically pay for training & support (competed) OSS users are responsible for paying/developing new improvements & any evaluations that they need; often cooperate with others to do so Goal: Active development community (like a consortium) 5
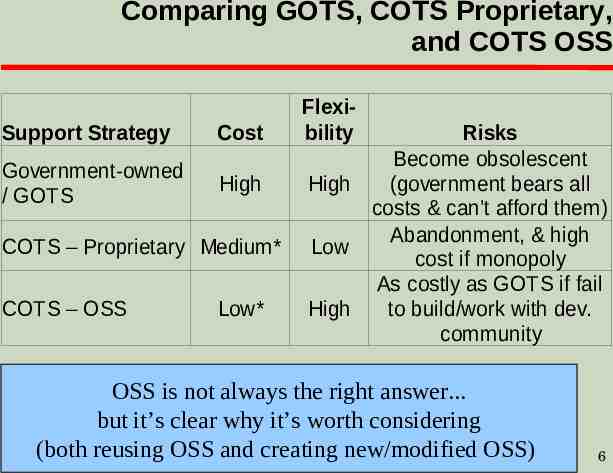
Comparing GOTS, COTS Proprietary, and COTS OSS Support Strategy Cost Government-owned / GOTS High COTS – Proprietary Medium* COTS – OSS Low* Flexibility Risks Become obsolescent High (government bears all costs & can’t afford them) Abandonment, & high Low cost if monopoly As costly as GOTS if fail High to build/work with dev. community OSS is not always the right answer. but it’s clear why it’s worth considering (both reusing OSS and creating new/modified OSS) 6
Outline Myths about Open Source Software (OSS) – Myth: OSS same as open systems/standards – Myth: OSS is non-commercial – Myth: OSS is unreliable – Myth: OSS forbidden by DoD policy – Some other myths OSS and security Evaluating COTS OSS & proprietary – same, different OSS & Government/DoD contracting OSS licenses Starting OSS project – Inc. how to select a license when writing OSS OSS non-challenges, challenges, & bottom line 7
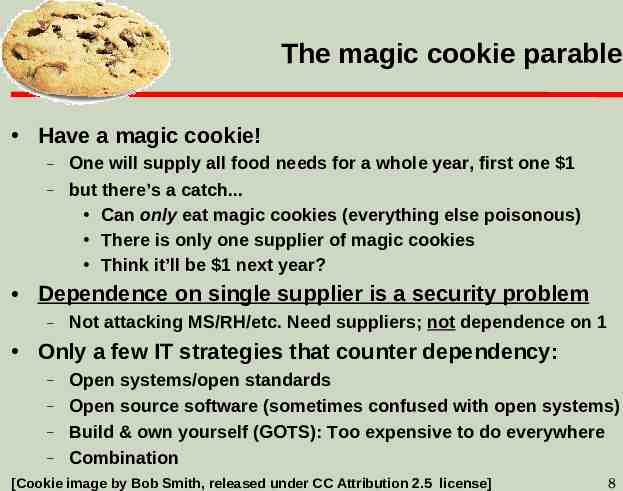
The magic cookie parable Have a magic cookie! – – One will supply all food needs for a whole year, first one 1 but there’s a catch. Can only eat magic cookies (everything else poisonous) There is only one supplier of magic cookies Think it’ll be 1 next year? Dependence on single supplier is a security problem – Not attacking MS/RH/etc. Need suppliers; not dependence on 1 Only a few IT strategies that counter dependency: – – – – Open systems/open standards Open source software (sometimes confused with open systems) Build & own yourself (GOTS): Too expensive to do everywhere Combination [Cookie image by Bob Smith, released under CC Attribution 2.5 license] 8
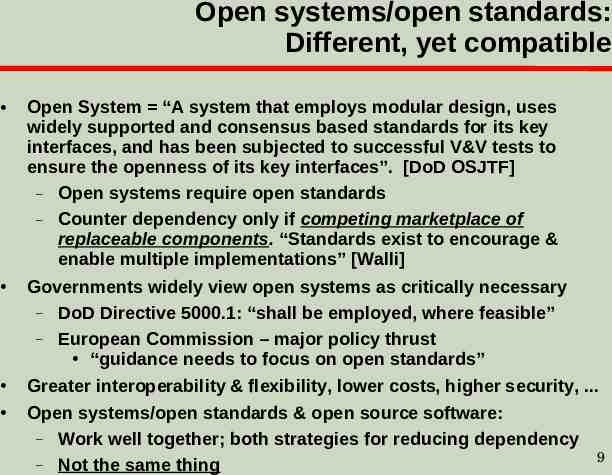
Open systems/open standards: Different, yet compatible Open System “A system that employs modular design, uses widely supported and consensus based standards for its key interfaces, and has been subjected to successful V&V tests to ensure the openness of its key interfaces”. [DoD OSJTF] – Open systems require open standards – Counter dependency only if competing marketplace of replaceable components. “Standards exist to encourage & enable multiple implementations” [Walli] Governments widely view open systems as critically necessary – DoD Directive 5000.1: “shall be employed, where feasible” – European Commission – major policy thrust “guidance needs to focus on open standards” Greater interoperability & flexibility, lower costs, higher security, . Open systems/open standards & open source software: – Work well together; both strategies for reducing dependency – Not the same thing 9
Nearly all OSS are commercial items / COTS Nearly all OSS are commercial items, & if extant, COTS U.S. Law (41 USC 403), FAR, & DFARS: OSS is commercial! – Commercial item is “(1) Any item, other than real property, that is of a type customarily used by the general public or by non-governmental entities for purposes [not government-unique], and (i) Has been sold, leased, or licensed to the general public; or (ii) Has been offered for sale, lease, or license to the general public. (3) [Above with] (i) Modifications of a type customarily available in the commercial marketplace; or (ii) Minor modifications made to meet Federal Government requirements.” – Intentionally broad; "enables the Government to take greater advantage of the commercial marketplace” [DoD AT&L] Confirmed by DoD “Clarifying Guidance Regarding OSS” (Oct 16, 2009) & Navy “OSS Guidance” (June 5, 2007) OSS projects seek improvements financial gain per – 17 USC 101: “financial gain” inc. “receipt, or expectation of receipt, of anything of value, including the receipt of other copyrighted works.” OMB Memo M-03-14: Commercial software, OSS support Important because U.S. Law (41 USC 403), FAR, DFARS require preference of commercial items (inc. COTS) & NDI: – Agencies must “(a) Conduct market research to determine [if] commercial items or nondevelopmental items are available (b) Acquire [them when available] (c) Require prime contractors and subcontractors at all tiers to incorporate, to the maximum extent practicable, [them] as components.”10
OSS is clearly commercial by other measures too Many OSS projects supported by commercial companies – IBM, Sun, Red Hat (solely OSS, market cap 4.3B), Novell, Microsoft (WiX, IronPython, SFU, Codeplex site) Big money in OSS companies – – – Citrix bought XenSource ( 500 million), Sun buying MySQL ( 1 billion), Red Hat bought JBoss ( 350 million), . IBM reports invested 1B in 2001, made it back in 2002 Venture capital invested 1.44B in OSS 2001-2006 [InfoWorld] Paid developers – Linux: 37K/38K changes; Apache: 1000 committers, 1 unpaid OSS licenses/projects approve of commercial support Sell service/hw, commoditize complements, avoid costs Use COTS/NDI because users share costs – OSS does! [See http://www.dwheeler.com/essays/commercial-floss.html] 11
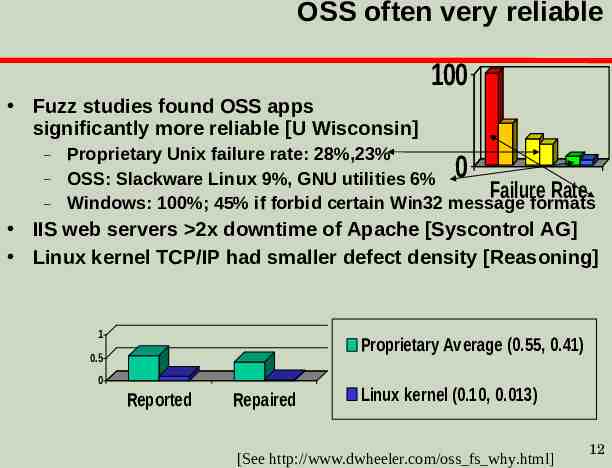
OSS often very reliable 100 Fuzz studies found OSS apps significantly more reliable [U Wisconsin] – – – Proprietary Unix failure rate: 28%,23% OSS: Slackware Linux 9%, GNU utilities 6% Failure Rate Windows: 100%; 45% if forbid certain Win32 message formats 0 IIS web servers 2x downtime of Apache [Syscontrol AG] Linux kernel TCP/IP had smaller defect density [Reasoning] 1 Proprietary Average (0.55, 0.41) 0.5 0 Reported Repaired Linux kernel (0.10, 0.013) [See http://www.dwheeler.com/oss fs why.html] 12
OSS consistent with DoD policy DoD memo “Clarifying Guidance Regarding OSS” (Oct 16, 2009) – – – – – – OSS is commercial, commercial must be preferred DoD must develop/update capabilities faster; OSS advantages Include OSS in market research, consider OSS positive aspects Source code is “data” per DODD 8320.02; must share in DoD DoD-developed software should be released to the public under certain conditions Updates DoD memo "Open Source Software (OSS) in the Department of Defense (DoD)" (2003), which also stated that OSS is fine as long as it meets usual software requirements OMB M-04-16 “Software Acquisition” (July 1, 2004) Dept. of the Navy “OSS Guidance” (June 5, 2007) Some misunderstood DoDD 8500.1/DoDI 8500.2 DCPD-1 13 as forbidding OSS.
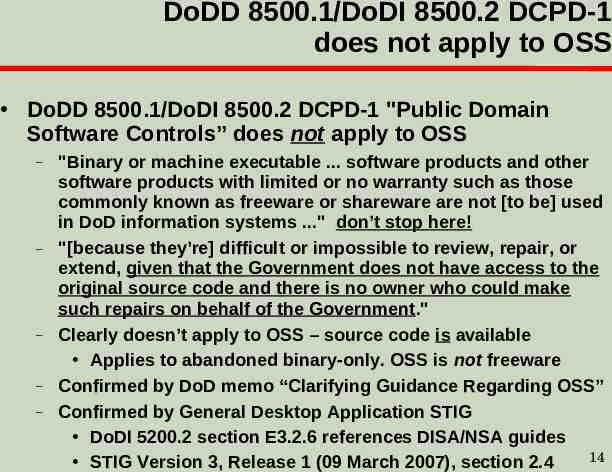
DoDD 8500.1/DoDI 8500.2 DCPD-1 does not apply to OSS DoDD 8500.1/DoDI 8500.2 DCPD-1 "Public Domain Software Controls” does not apply to OSS – – – – – "Binary or machine executable . software products and other software products with limited or no warranty such as those commonly known as freeware or shareware are not [to be] used in DoD information systems ." don’t stop here! "[because they’re] difficult or impossible to review, repair, or extend, given that the Government does not have access to the original source code and there is no owner who could make such repairs on behalf of the Government." Clearly doesn’t apply to OSS – source code is available Applies to abandoned binary-only. OSS is not freeware Confirmed by DoD memo “Clarifying Guidance Regarding OSS” Confirmed by General Desktop Application STIG DoDI 5200.2 section E3.2.6 references DISA/NSA guides 14 STIG Version 3, Release 1 (09 March 2007), section 2.4
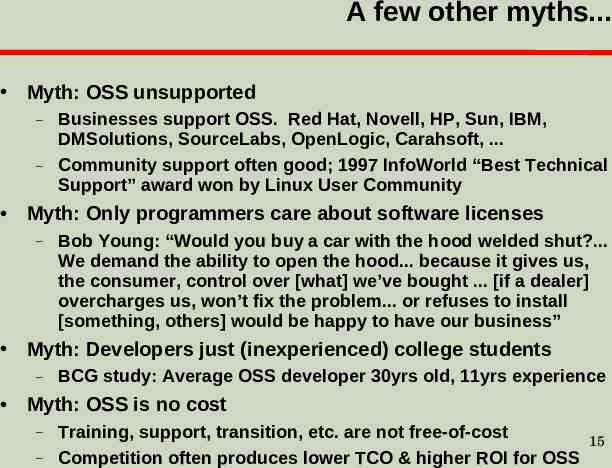
A few other myths. Myth: OSS unsupported – – Businesses support OSS. Red Hat, Novell, HP, Sun, IBM, DMSolutions, SourceLabs, OpenLogic, Carahsoft, . Community support often good; 1997 InfoWorld “Best Technical Support” award won by Linux User Community Myth: Only programmers care about software licenses – Bob Young: “Would you buy a car with the hood welded shut?. We demand the ability to open the hood. because it gives us, the consumer, control over [what] we’ve bought . [if a dealer] overcharges us, won’t fix the problem. or refuses to install [something, others] would be happy to have our business” Myth: Developers just (inexperienced) college students – BCG study: Average OSS developer 30yrs old, 11yrs experience Myth: OSS is no cost – – Training, support, transition, etc. are not free-of-cost Competition often produces lower TCO & higher ROI for OSS 15
Extreme security claims for OSS Extreme claims – “OSS is always more secure” – “Proprietary is always more secure” Reality: Neither OSS nor proprietary always better – Some specific OSS programs are more secure than their competing proprietary competitors – Include OSS options when acquiring, then evaluate There is a principle that gives OSS a potential advantage 16
Open design: A security fundamental Saltzer & Schroeder [1974/1975] - Open design principle – the protection mechanism must not depend on attacker ignorance OSS better fulfills this principle Security experts perceive OSS advantage – – – Bruce Schneier: “demand OSS for anything related to security” Vincent Rijmen (AES): “forces people to write more clear code & adhere to standards” Whitfield Diffie: “it’s simply unrealistic to depend on secrecy for security” 17
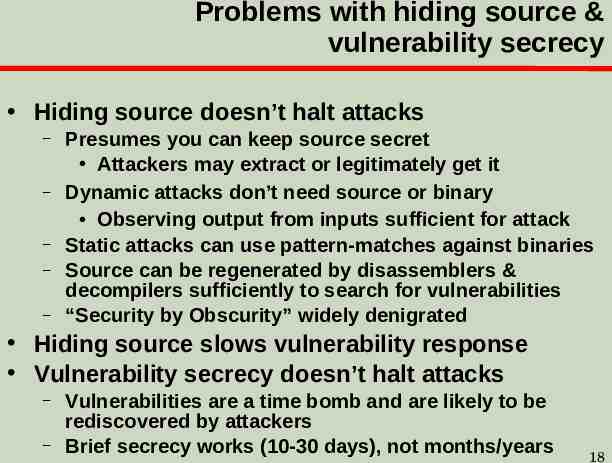
Problems with hiding source & vulnerability secrecy Hiding source doesn’t halt attacks – – – – – Presumes you can keep source secret Attackers may extract or legitimately get it Dynamic attacks don’t need source or binary Observing output from inputs sufficient for attack Static attacks can use pattern-matches against binaries Source can be regenerated by disassemblers & decompilers sufficiently to search for vulnerabilities “Security by Obscurity” widely denigrated Hiding source slows vulnerability response Vulnerability secrecy doesn’t halt attacks – – Vulnerabilities are a time bomb and are likely to be rediscovered by attackers Brief secrecy works (10-30 days), not months/years 18
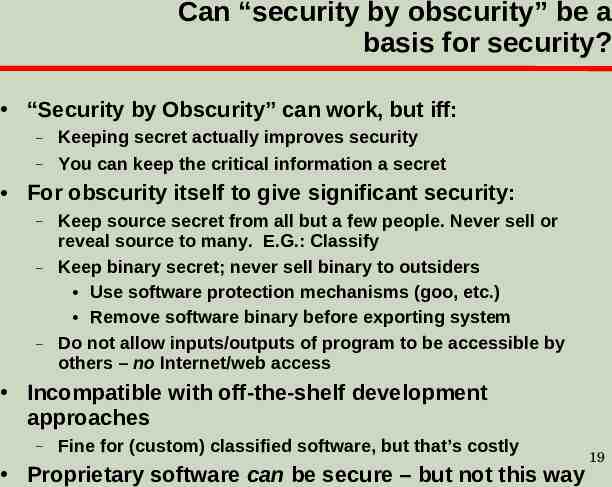
Can “security by obscurity” be a basis for security? “Security by Obscurity” can work, but iff: – – Keeping secret actually improves security You can keep the critical information a secret For obscurity itself to give significant security: – – – Keep source secret from all but a few people. Never sell or reveal source to many. E.G.: Classify Keep binary secret; never sell binary to outsiders Use software protection mechanisms (goo, etc.) Remove software binary before exporting system Do not allow inputs/outputs of program to be accessible by others – no Internet/web access Incompatible with off-the-shelf development approaches – Fine for (custom) classified software, but that’s costly Proprietary software can be secure – but not this way 19
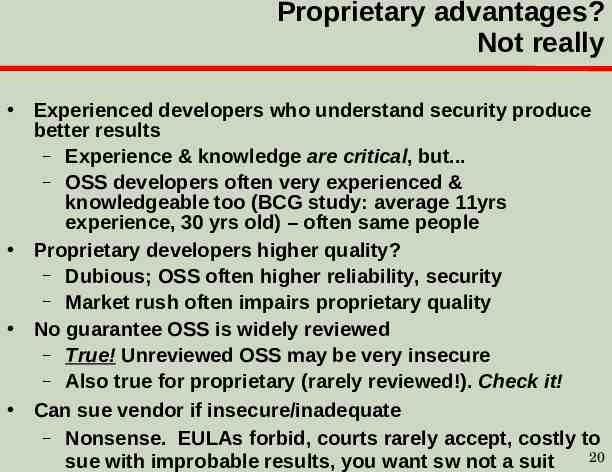
Proprietary advantages? Not really Experienced developers who understand security produce better results – Experience & knowledge are critical, but. – OSS developers often very experienced & knowledgeable too (BCG study: average 11yrs experience, 30 yrs old) – often same people Proprietary developers higher quality? – Dubious; OSS often higher reliability, security – Market rush often impairs proprietary quality No guarantee OSS is widely reviewed – True! Unreviewed OSS may be very insecure – Also true for proprietary (rarely reviewed!). Check it! Can sue vendor if insecure/inadequate – Nonsense. EULAs forbid, courts rarely accept, costly to 20 sue with improbable results, you want sw not a suit
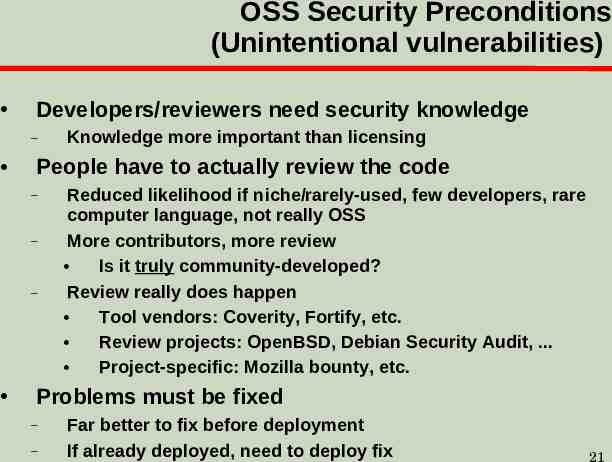
OSS Security Preconditions (Unintentional vulnerabilities) Developers/reviewers need security knowledge – People have to actually review the code – – – Knowledge more important than licensing Reduced likelihood if niche/rarely-used, few developers, rare computer language, not really OSS More contributors, more review Is it truly community-developed? Review really does happen Tool vendors: Coverity, Fortify, etc. Review projects: OpenBSD, Debian Security Audit, . Project-specific: Mozilla bounty, etc. Problems must be fixed – – Far better to fix before deployment If already deployed, need to deploy fix 21
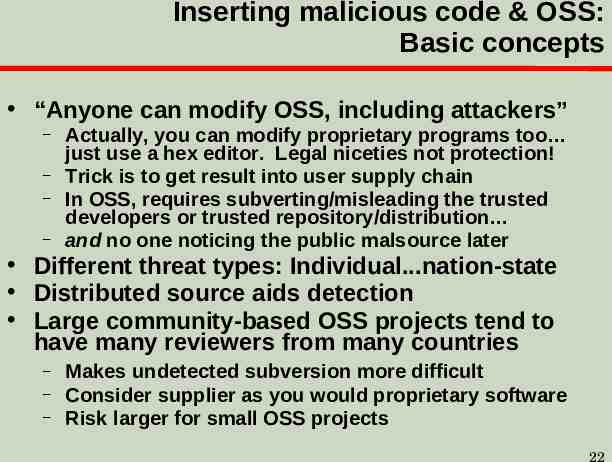
Inserting malicious code & OSS: Basic concepts “Anyone can modify OSS, including attackers” – – – – Actually, you can modify proprietary programs too just use a hex editor. Legal niceties not protection! Trick is to get result into user supply chain In OSS, requires subverting/misleading the trusted developers or trusted repository/distribution and no one noticing the public malsource later Different threat types: Individual.nation-state Distributed source aids detection Large community-based OSS projects tend to have many reviewers from many countries – – – Makes undetected subversion more difficult Consider supplier as you would proprietary software Risk larger for small OSS projects 22
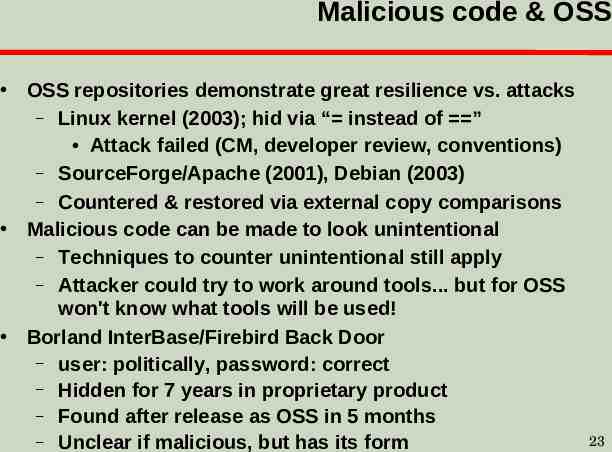
Malicious code & OSS OSS repositories demonstrate great resilience vs. attacks – Linux kernel (2003); hid via “ instead of ” Attack failed (CM, developer review, conventions) – SourceForge/Apache (2001), Debian (2003) – Countered & restored via external copy comparisons Malicious code can be made to look unintentional – Techniques to counter unintentional still apply – Attacker could try to work around tools. but for OSS won't know what tools will be used! Borland InterBase/Firebird Back Door – user: politically, password: correct – Hidden for 7 years in proprietary product – Found after release as OSS in 5 months – Unclear if malicious, but has its form 23
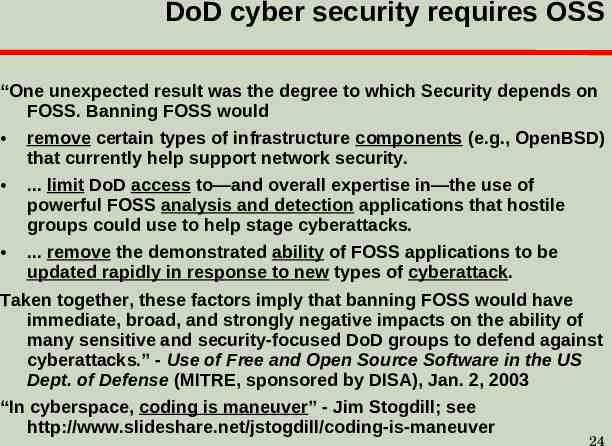
DoD cyber security requires OSS “One unexpected result was the degree to which Security depends on FOSS. Banning FOSS would remove certain types of infrastructure components (e.g., OpenBSD) that currently help support network security. . limit DoD access to—and overall expertise in—the use of powerful FOSS analysis and detection applications that hostile groups could use to help stage cyberattacks. . remove the demonstrated ability of FOSS applications to be updated rapidly in response to new types of cyberattack. Taken together, these factors imply that banning FOSS would have immediate, broad, and strongly negative impacts on the ability of many sensitive and security-focused DoD groups to defend against cyberattacks.” - Use of Free and Open Source Software in the US Dept. of Defense (MITRE, sponsored by DISA), Jan. 2, 2003 “In cyberspace, coding is maneuver” - Jim Stogdill; see http://www.slideshare.net/jstogdill/coding-is-maneuver 24
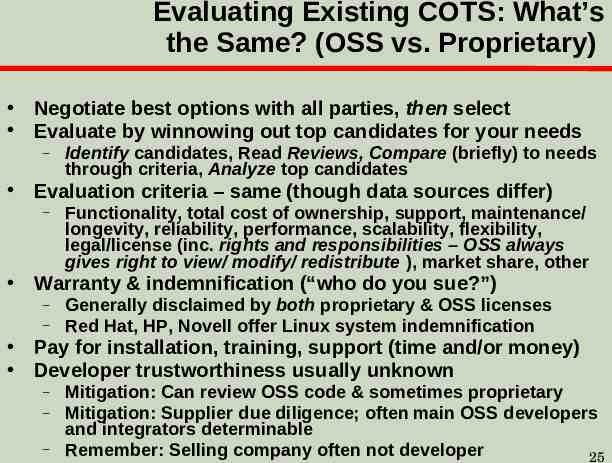
Evaluating Existing COTS: What’s the Same? (OSS vs. Proprietary) Negotiate best options with all parties, then select Evaluate by winnowing out top candidates for your needs – Identify candidates, Read Reviews, Compare (briefly) to needs through criteria, Analyze top candidates Evaluation criteria – same (though data sources differ) – Functionality, total cost of ownership, support, maintenance/ longevity, reliability, performance, scalability, flexibility, legal/license (inc. rights and responsibilities – OSS always gives right to view/ modify/ redistribute ), market share, other Warranty & indemnification (“who do you sue?”) – – Generally disclaimed by both proprietary & OSS licenses Red Hat, HP, Novell offer Linux system indemnification Pay for installation, training, support (time and/or money) Developer trustworthiness usually unknown – – – Mitigation: Can review OSS code & sometimes proprietary Mitigation: Supplier due diligence; often main OSS developers and integrators determinable Remember: Selling company often not developer 25
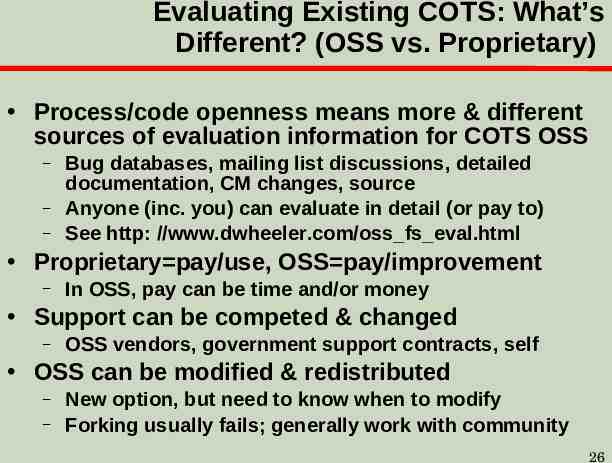
Evaluating Existing COTS: What’s Different? (OSS vs. Proprietary) Process/code openness means more & different sources of evaluation information for COTS OSS – – – Bug databases, mailing list discussions, detailed documentation, CM changes, source Anyone (inc. you) can evaluate in detail (or pay to) See http: //www.dwheeler.com/oss fs eval.html Proprietary pay/use, OSS pay/improvement – In OSS, pay can be time and/or money Support can be competed & changed – OSS vendors, government support contracts, self OSS can be modified & redistributed – – New option, but need to know when to modify Forking usually fails; generally work with community 26
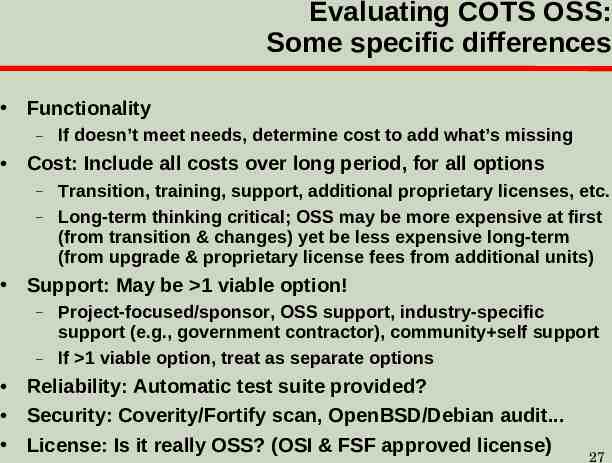
Evaluating COTS OSS: Some specific differences Functionality – If doesn’t meet needs, determine cost to add what’s missing Cost: Include all costs over long period, for all options – – Transition, training, support, additional proprietary licenses, etc. Long-term thinking critical; OSS may be more expensive at first (from transition & changes) yet be less expensive long-term (from upgrade & proprietary license fees from additional units) Support: May be 1 viable option! – – Project-focused/sponsor, OSS support, industry-specific support (e.g., government contractor), community self support If 1 viable option, treat as separate options Reliability: Automatic test suite provided? Security: Coverity/Fortify scan, OpenBSD/Debian audit. License: Is it really OSS? (OSI & FSF approved license) 27
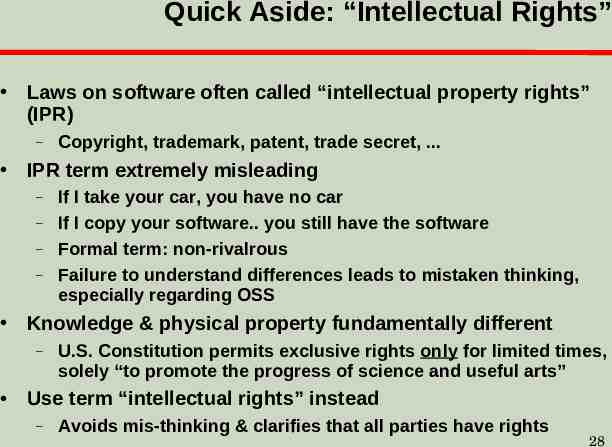
Quick Aside: “Intellectual Rights” Laws on software often called “intellectual property rights” (IPR) – Copyright, trademark, patent, trade secret, . IPR term extremely misleading – – – – If I take your car, you have no car If I copy your software. you still have the software Formal term: non-rivalrous Failure to understand differences leads to mistaken thinking, especially regarding OSS Knowledge & physical property fundamentally different – U.S. Constitution permits exclusive rights only for limited times, solely “to promote the progress of science and useful arts” Use term “intellectual rights” instead – Avoids mis-thinking & clarifies that all parties have rights 28
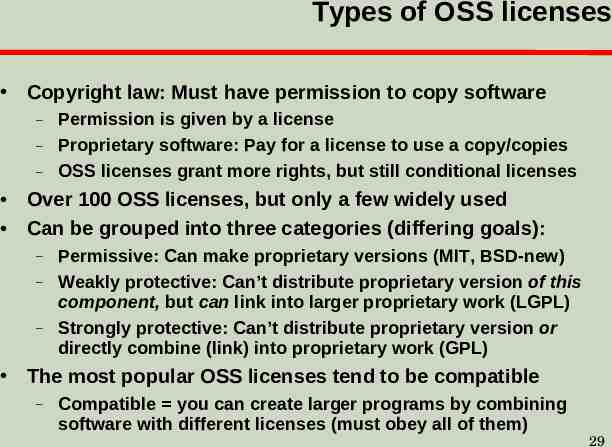
Types of OSS licenses Copyright law: Must have permission to copy software – – – Permission is given by a license Proprietary software: Pay for a license to use a copy/copies OSS licenses grant more rights, but still conditional licenses Over 100 OSS licenses, but only a few widely used Can be grouped into three categories (differing goals): – – – Permissive: Can make proprietary versions (MIT, BSD-new) Weakly protective: Can’t distribute proprietary version of this component, but can link into larger proprietary work (LGPL) Strongly protective: Can’t distribute proprietary version or directly combine (link) into proprietary work (GPL) The most popular OSS licenses tend to be compatible – Compatible you can create larger programs by combining software with different licenses (must obey all of them) 29
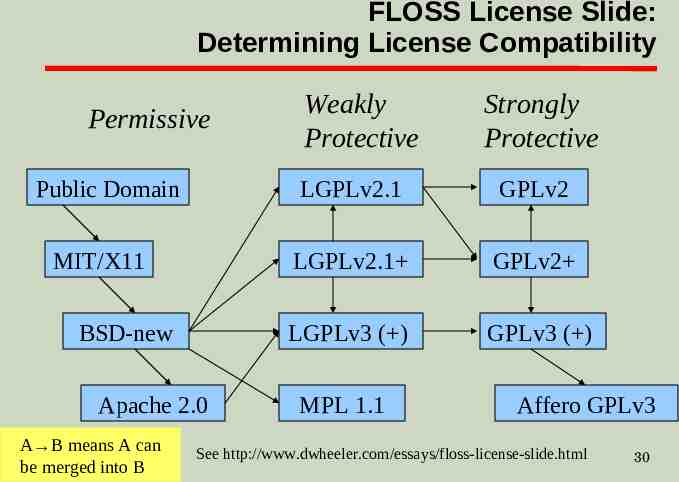
FLOSS License Slide: Determining License Compatibility Permissive Public Domain MIT/X11 BSD-new Apache 2.0 A B means A can be merged into B Weakly Protective Strongly Protective LGPLv2.1 GPLv2 LGPLv2.1 GPLv2 LGPLv3 ( ) GPLv3 ( ) MPL 1.1 Affero GPLv3 See http://www.dwheeler.com/essays/floss-license-slide.html 30
Starting OSS Project Check usual project-start requirements – – Is there a need, no/better solution, TCO, etc. Examine OSS approach; similar to GOTS; greater opportunity for cost-sharing, greater openness Lower cost & time, higher quality, more innovation Goal: co-develop, so remove barriers to entry – – – – – – – Use common license well-known to be OSS (GPL, LGPL, MIT/X, BSD-new) – don’t write your own license, it’s a common road to failure & very hard to overcome Establish project website (mailing list, tracker, source) Document scope, major decisions Use typical infrastructure, tools, etc. (e.g., SCM) Maximize portability, avoid proprietary langs/libraries Must run - Small-but-running better than big-and-not Establish vetting process(es) before government use Government-paid lead? Testing? Same issues: proprietary31 Many articles & books on subject
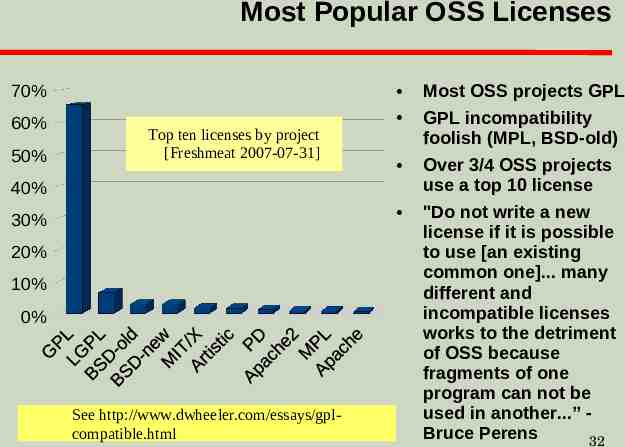
Most Popular OSS Licenses 70% 60% 50% Top ten licenses by project [Freshmeat 2007-07-31] 40% 30% 20% 10% 0% See http://www.dwheeler.com/essays/gplcompatible.html Most OSS projects GPL GPL incompatibility foolish (MPL, BSD-old) Over 3/4 OSS projects use a top 10 license "Do not write a new license if it is possible to use [an existing common one]. many different and incompatible licenses works to the detriment of OSS because fragments of one program can not be used in another.” Bruce Perens 32
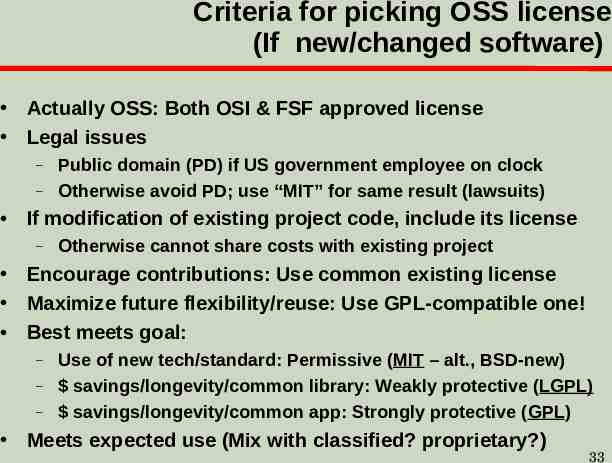
Criteria for picking OSS license (If new/changed software) Actually OSS: Both OSI & FSF approved license Legal issues – – Public domain (PD) if US government employee on clock Otherwise avoid PD; use “MIT” for same result (lawsuits) If modification of existing project code, include its license – Otherwise cannot share costs with existing project Encourage contributions: Use common existing license Maximize future flexibility/reuse: Use GPL-compatible one! Best meets goal: – – – Use of new tech/standard: Permissive (MIT – alt., BSD-new) savings/longevity/common library: Weakly protective (LGPL) savings/longevity/common app: Strongly protective (GPL) Meets expected use (Mix with classified? proprietary?) 33
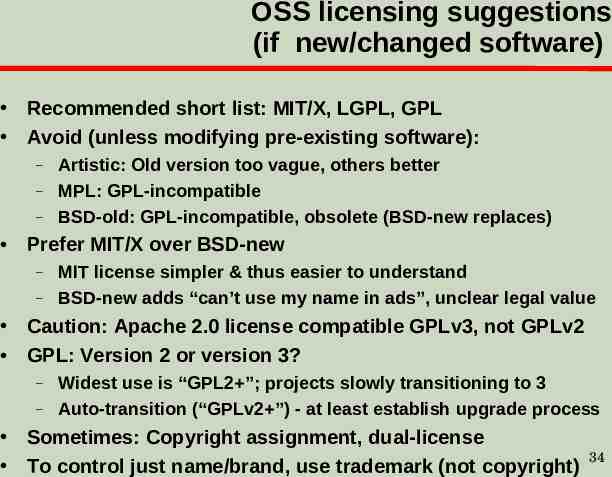
OSS licensing suggestions (if new/changed software) Recommended short list: MIT/X, LGPL, GPL Avoid (unless modifying pre-existing software): – – – Artistic: Old version too vague, others better MPL: GPL-incompatible BSD-old: GPL-incompatible, obsolete (BSD-new replaces) Prefer MIT/X over BSD-new – – MIT license simpler & thus easier to understand BSD-new adds “can’t use my name in ads”, unclear legal value Caution: Apache 2.0 license compatible GPLv3, not GPLv2 GPL: Version 2 or version 3? – – Widest use is “GPL2 ”; projects slowly transitioning to 3 Auto-transition (“GPLv2 ”) - at least establish upgrade process Sometimes: Copyright assignment, dual-license To control just name/brand, use trademark (not copyright) 34
OSS & Government/DoD contracting: Can government/contractors use OSS? Yes. If already licensed to the public, it’s commercial software per U.S. law/regulation Must comply with all other rules, as normal 35
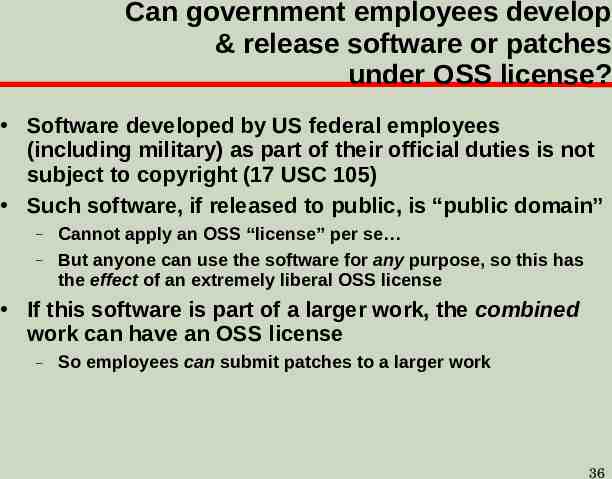
Can government employees develop & release software or patches under OSS license? Software developed by US federal employees (including military) as part of their official duties is not subject to copyright (17 USC 105) Such software, if released to public, is “public domain” – – Cannot apply an OSS “license” per se But anyone can use the software for any purpose, so this has the effect of an extremely liberal OSS license If this software is part of a larger work, the combined work can have an OSS license – So employees can submit patches to a larger work 36
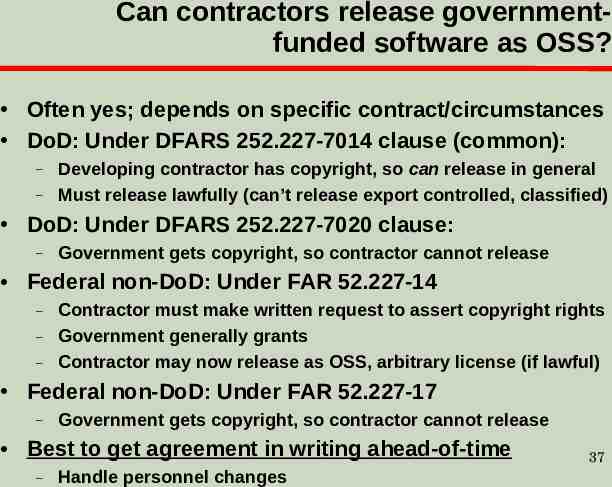
Can contractors release governmentfunded software as OSS? Often yes; depends on specific contract/circumstances DoD: Under DFARS 252.227-7014 clause (common): – – Developing contractor has copyright, so can release in general Must release lawfully (can’t release export controlled, classified) DoD: Under DFARS 252.227-7020 clause: – Government gets copyright, so contractor cannot release Federal non-DoD: Under FAR 52.227-14 – – – Contractor must make written request to assert copyright rights Government generally grants Contractor may now release as OSS, arbitrary license (if lawful) Federal non-DoD: Under FAR 52.227-17 – Government gets copyright, so contractor cannot release Best to get agreement in writing ahead-of-time – Handle personnel changes 37
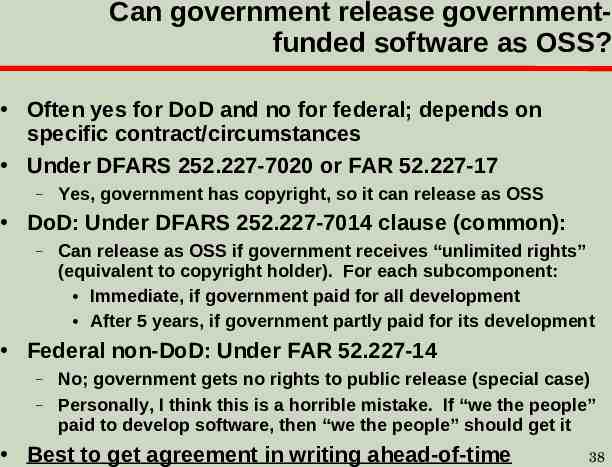
Can government release governmentfunded software as OSS? Often yes for DoD and no for federal; depends on specific contract/circumstances Under DFARS 252.227-7020 or FAR 52.227-17 – Yes, government has copyright, so it can release as OSS DoD: Under DFARS 252.227-7014 clause (common): – Can release as OSS if government receives “unlimited rights” (equivalent to copyright holder). For each subcomponent: Immediate, if government paid for all development After 5 years, if government partly paid for its development Federal non-DoD: Under FAR 52.227-14 – – No; government gets no rights to public release (special case) Personally, I think this is a horrible mistake. If “we the people” paid to develop software, then “we the people” should get it Best to get agreement in writing ahead-of-time 38
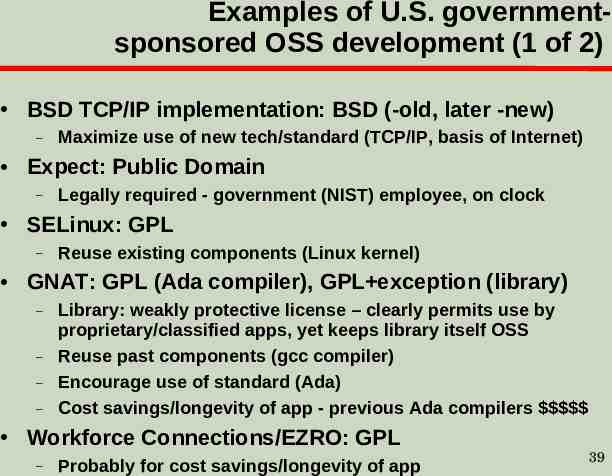
Examples of U.S. governmentsponsored OSS development (1 of 2) BSD TCP/IP implementation: BSD (-old, later -new) – Maximize use of new tech/standard (TCP/IP, basis of Internet) Expect: Public Domain – Legally required - government (NIST) employee, on clock SELinux: GPL – Reuse existing components (Linux kernel) GNAT: GPL (Ada compiler), GPL exception (library) – – – – Library: weakly protective license – clearly permits use by proprietary/classified apps, yet keeps library itself OSS Reuse past components (gcc compiler) Encourage use of standard (Ada) Cost savings/longevity of app - previous Ada compilers Workforce Connections/EZRO: GPL – Probably for cost savings/longevity of app 39
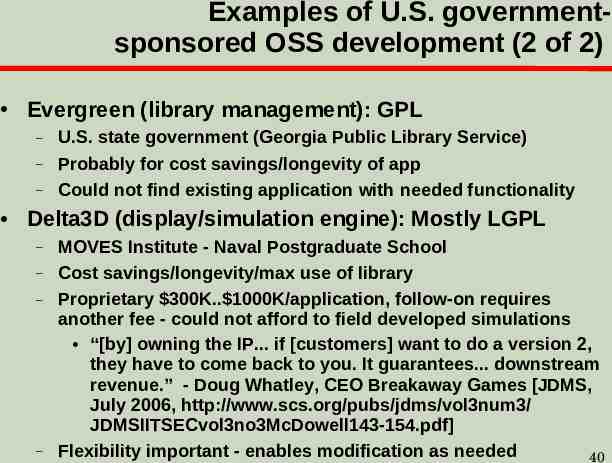
Examples of U.S. governmentsponsored OSS development (2 of 2) Evergreen (library management): GPL – – – U.S. state government (Georgia Public Library Service) Probably for cost savings/longevity of app Could not find existing application with needed functionality Delta3D (display/simulation engine): Mostly LGPL – – – – MOVES Institute - Naval Postgraduate School Cost savings/longevity/max use of library Proprietary 300K. 1000K/application, follow-on requires another fee - could not afford to field developed simulations “[by] owning the IP. if [customers] want to do a version 2, they have to come back to you. It guarantees. downstream revenue.” - Doug Whatley, CEO Breakaway Games [JDMS, July 2006, http://www.scs.org/pubs/jdms/vol3num3/ JDMSIITSECvol3no3McDowell143-154.pdf] Flexibility important - enables modification as needed 40
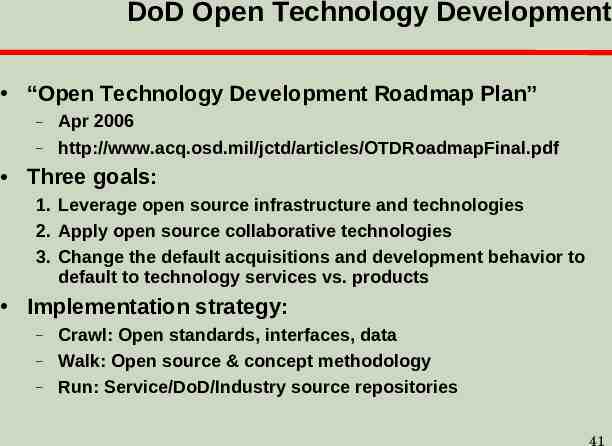
DoD Open Technology Development “Open Technology Development Roadmap Plan” – – Apr 2006 http://www.acq.osd.mil/jctd/articles/OTDRoadmapFinal.pdf Three goals: 1. Leverage open source infrastructure and technologies 2. Apply open source collaborative technologies 3. Change the default acquisitions and development behavior to default to technology services vs. products Implementation strategy: – – – Crawl: Open standards, interfaces, data Walk: Open source & concept methodology Run: Service/DoD/Industry source repositories 41
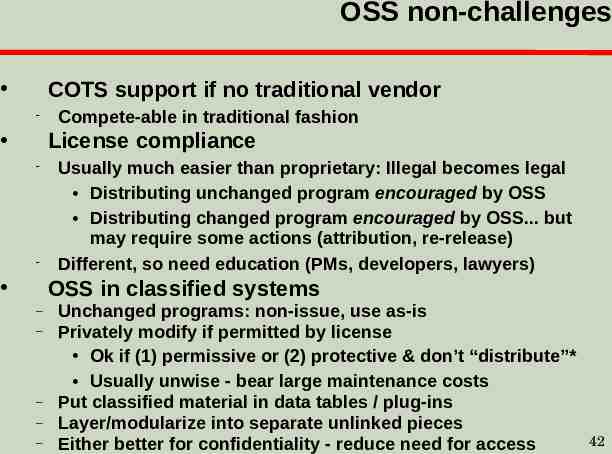
OSS non-challenges COTS support if no traditional vendor Compete-able in traditional fashion License compliance Usually much easier than proprietary: Illegal becomes legal Distributing unchanged program encouraged by OSS Distributing changed program encouraged by OSS. but may require some actions (attribution, re-release) Different, so need education (PMs, developers, lawyers) OSS in classified systems – – – – – Unchanged programs: non-issue, use as-is Privately modify if permitted by license Ok if (1) permissive or (2) protective & don’t “distribute”* Usually unwise - bear large maintenance costs Put classified material in data tables / plug-ins Layer/modularize into separate unlinked pieces Either better for confidentiality - reduce need for access 42
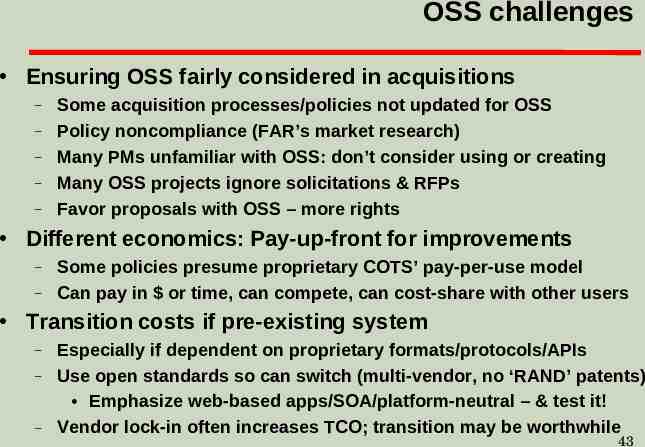
OSS challenges Ensuring OSS fairly considered in acquisitions – – – – – Some acquisition processes/policies not updated for OSS Policy noncompliance (FAR’s market research) Many PMs unfamiliar with OSS: don’t consider using or creating Many OSS projects ignore solicitations & RFPs Favor proposals with OSS – more rights Different economics: Pay-up-front for improvements – – Some policies presume proprietary COTS’ pay-per-use model Can pay in or time, can compete, can cost-share with other users Transition costs if pre-existing system – – – Especially if dependent on proprietary formats/protocols/APIs Use open standards so can switch (multi-vendor, no ‘RAND’ patents) Emphasize web-based apps/SOA/platform-neutral – & test it! Vendor lock-in often increases TCO; transition may be worthwhile 43
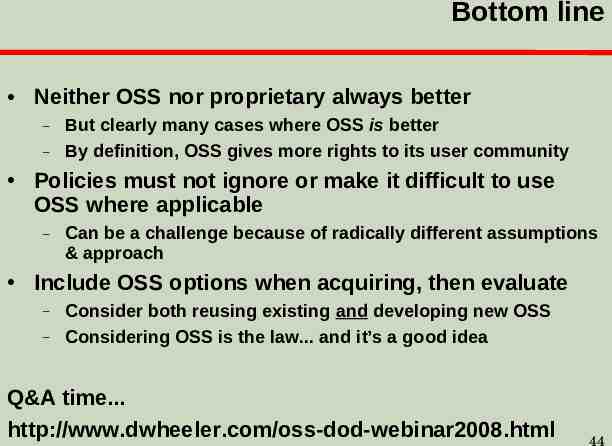
Bottom line Neither OSS nor proprietary always better – – But clearly many cases where OSS is better By definition, OSS gives more rights to its user community Policies must not ignore or make it difficult to use OSS where applicable – Can be a challenge because of radically different assumptions & approach Include OSS options when acquiring, then evaluate – – Consider both reusing existing and developing new OSS Considering OSS is the law. and it’s a good idea Q&A time. http://www.dwheeler.com/oss-dod-webinar2008.html 44
Backup slides 45
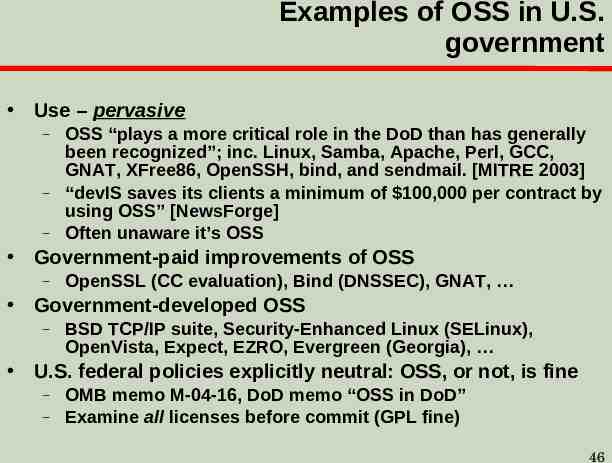
Examples of OSS in U.S. government Use – pervasive – – – OSS “plays a more critical role in the DoD than has generally been recognized”; inc. Linux, Samba, Apache, Perl, GCC, GNAT, XFree86, OpenSSH, bind, and sendmail. [MITRE 2003] “devIS saves its clients a minimum of 100,000 per contract by using OSS” [NewsForge] Often unaware it’s OSS Government-paid improvements of OSS – OpenSSL (CC evaluation), Bind (DNSSEC), GNAT, Government-developed OSS – BSD TCP/IP suite, Security-Enhanced Linux (SELinux), OpenVista, Expect, EZRO, Evergreen (Georgia), U.S. federal policies explicitly neutral: OSS, or not, is fine – – OMB memo M-04-16, DoD memo “OSS in DoD” Examine all licenses before commit (GPL fine) 46
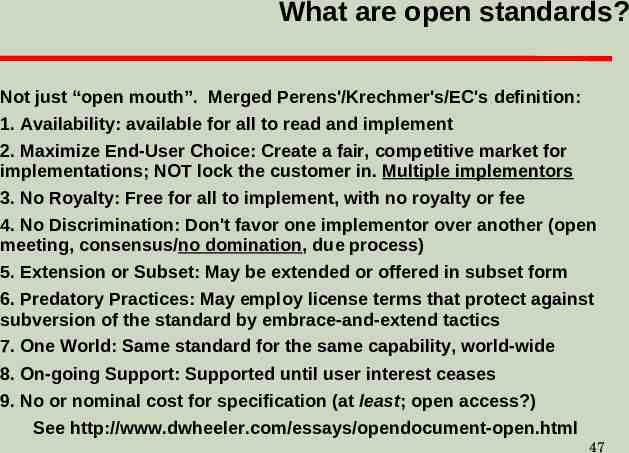
What are open standards? Not just “open mouth”. Merged Perens'/Krechmer's/EC's definition: 1. Availability: available for all to read and implement 2. Maximize End-User Choice: Create a fair, competitive market for implementations; NOT lock the customer in. Multiple implementors 3. No Royalty: Free for all to implement, with no royalty or fee 4. No Discrimination: Don't favor one implementor over another (open meeting, consensus/no domination, due process) 5. Extension or Subset: May be extended or offered in subset form 6. Predatory Practices: May employ license terms that protect against subversion of the standard by embrace-and-extend tactics 7. One World: Same standard for the same capability, world-wide 8. On-going Support: Supported until user interest ceases 9. No or nominal cost for specification (at least; open access?) See http://www.dwheeler.com/essays/opendocument-open.html 47
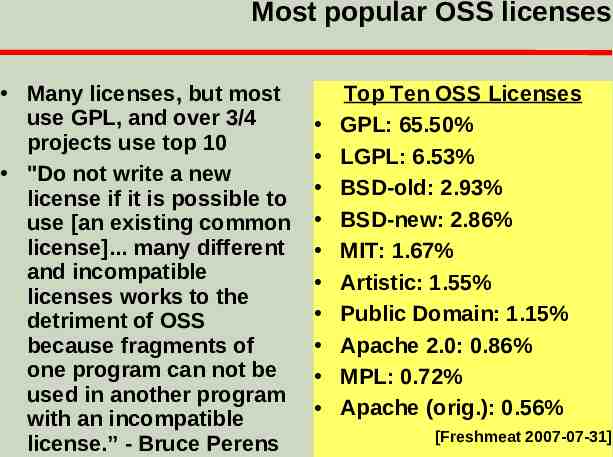
Most popular OSS licenses Many licenses, but most use GPL, and over 3/4 projects use top 10 "Do not write a new license if it is possible to use [an existing common license]. many different and incompatible licenses works to the detriment of OSS because fragments of one program can not be used in another program with an incompatible license.” - Bruce Perens Top Ten OSS Licenses GPL: 65.50% LGPL: 6.53% BSD-old: 2.93% BSD-new: 2.86% MIT: 1.67% Artistic: 1.55% Public Domain: 1.15% Apache 2.0: 0.86% MPL: 0.72% Apache (orig.): 0.56% [Freshmeat 2007-07-31] 48
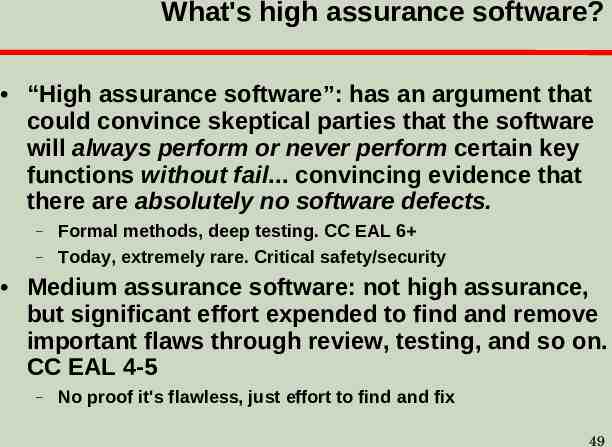
What's high assurance software? “High assurance software”: has an argument that could convince skeptical parties that the software will always perform or never perform certain key functions without fail. convincing evidence that there are absolutely no software defects. – – Formal methods, deep testing. CC EAL 6 Today, extremely rare. Critical safety/security Medium assurance software: not high assurance, but significant effort expended to find and remove important flaws through review, testing, and so on. CC EAL 4-5 – No proof it's flawless, just effort to find and fix 49
High assurance Many OSS tools that support developing HA – – – – – CM: CVS, Subversion (SVN), git, Mercurial, . Testing: opensourcetesting.org lists 275 tools Apr 2006, inc. Bugzilla (tracking), DejaGnu (framework), gcov (coverage), . Formal methods: ACL2, PVS, Prover9/Mace4, Isabelle, Alloy, . Analysis implementation: Common LISP (GNU Common LISP (GCL), CMUCL, GNU CLISP), Prolog (GNU Prolog, SWI-Prolog, Ciao Prolog, YAP), Standard ML, Haskell (GHC, Hugs), . Code implementation: C (gcc), Ada (gcc GNAT), . HA OSS: Almost never tried (proprietary rare too) OSS should be better for HA – hope to see in future – In mathematics, proofs are often wrong, so only peer review of proofs valid [De Millo,Lipton,Perlis]. OSS! 50
Formal methods & OSS Formal methods applicable to OSS & proprietary Difference: OSS allows public peer review – – – In mathematics, peer review often finds problems in proofs; many publicly-published proofs are later invalidated Expect true for software-related proofs, even with proofcheckers (invalid models/translation, invalid assumptions/proof methods) Proprietary sw generally forbids public peer review Formal methods challenges same – – – Few understand formal methods (anywhere) Scaling up to “real” systems difficult Costs of applying formal methods—who pays? May be even harder for OSS Not easy for proprietary either 51
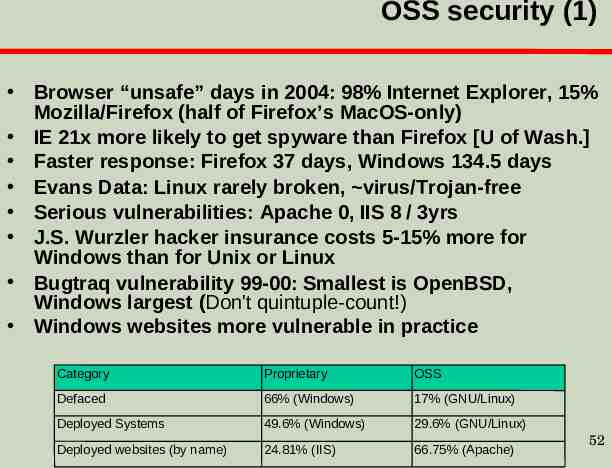
OSS security (1) Browser “unsafe” days in 2004: 98% Internet Explorer, 15% Mozilla/Firefox (half of Firefox’s MacOS-only) IE 21x more likely to get spyware than Firefox [U of Wash.] Faster response: Firefox 37 days, Windows 134.5 days Evans Data: Linux rarely broken, virus/Trojan-free Serious vulnerabilities: Apache 0, IIS 8 / 3yrs J.S. Wurzler hacker insurance costs 5-15% more for Windows than for Unix or Linux Bugtraq vulnerability 99-00: Smallest is OpenBSD, Windows largest (Don't quintuple-count!) Windows websites more vulnerable in practice Category Proprietary OSS Defaced 66% (Windows) 17% (GNU/Linux) Deployed Systems 49.6% (Windows) 29.6% (GNU/Linux) Deployed websites (by name) 24.81% (IIS) 66.75% (Apache) 52
OSS security (2) Unpatched networked systems: 3 months Linux, hours Windows (variance minutes . months) [Honeynet.org, Dec 2004] – Windows SP2 believed to be better than previous versions of Windows 50% Windows vulnerabilities are critical, vs. 10% in Red Hat [Nicholas Petreley, Oct 2004] Viruses primarily Windows phenomenon – 60,000 Windows, 40 Macintosh, 5 for commercial Unix versions, 40 for Linux 91% broadband users have spyware on their home computers (proprietary OS) [National Cyber Security Alliance, May 2003] vs. 0% on OSS 53
OSS security (3) OSS systems scored better on security [Payne, Information Systems Journal 2002] Survey of 6,344 software development managers April 2005 favored OSS [BZ Research] 54
Common Criteria & OSS Common Criteria (CC) can be used on OSS – Red Hat Linux, Novell/SuSE Linux, OpenSSL CC matches OSS imperfectly – – – CC developed before rise of OSS Doesn’t credit mass peer review or detailed code review Requires mass creation of documentation not normally used in OSS development Government policies discriminate against OSS – – – Presume that vendor will pay hundreds of thousands or millions for a CC evaluation (“big company” funding) Presumes nearly all small business & OSS insecure Presume that “without CC evaluation, it’s not secure” Need to fix policies to meet real goal: secure software Government-funded eval in exchange for free use? Multi-agency/government funding? Alternative evaluation processes? 55
Evaluating OSS? Look for evidence First, identify your security requirements Look for evidence at OSS project website – – – – – User’s/Admin Guides: discuss make/keep it secure? Process for reporting security vulnerabilities? Cryptographic signatures for current release? Developer mailing lists discuss security issues and work to keep the program secure? Active community Use other information sources where available – – E.G., CVE but absence is not necessarily good External reputation (e.g., OpenBSD) See http://www.dwheeler.com/oss fs eval.html 56
Concluding remarks OSS options should always be considered – – – Both choosing COTS OSS & creating new OSS project Components or even whole project (depending on need) Not always best choice, but foolish to ignore OSS can be very flexible & often lowers costs – Directly and as competition to non-OSS (keep options open!) OSS raises strategic questions for governments – – – – How pool users to start OSS projects when appropriate? Educating PMs on OSS, deploying fully open architectures Research: default to OSS (with some common OSS license) Eliminating software patents Projects should change to consider OSS approaches: – – – PM education: OSS differences, fears, always consider option Classified systems: separate data & program, layer programs Open standards so can change later (e.g., browser-neutral) Require & operationally demonstrate that can switch components 57
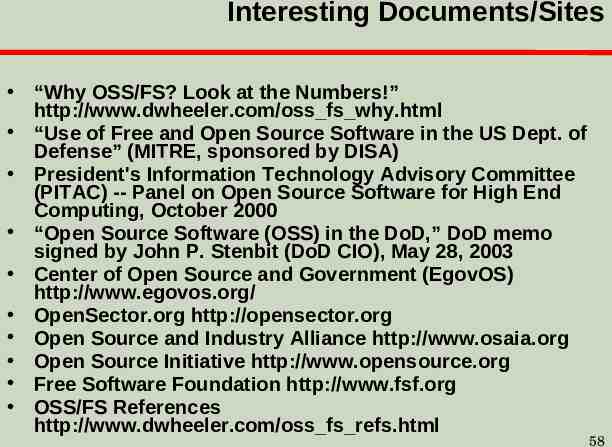
Interesting Documents/Sites “Why OSS/FS? Look at the Numbers!” http://www.dwheeler.com/oss fs why.html “Use of Free and Open Source Software in the US Dept. of Defense” (MITRE, sponsored by DISA) President's Information Technology Advisory Committee (PITAC) -- Panel on Open Source Software for High End Computing, October 2000 “Open Source Software (OSS) in the DoD,” DoD memo signed by John P. Stenbit (DoD CIO), May 28, 2003 Center of Open Source and Government (EgovOS) http://www.egovos.org/ OpenSector.org http://opensector.org Open Source and Industry Alliance http://www.osaia.org Open Source Initiative http://www.opensource.org Free Software Foundation http://www.fsf.org OSS/FS References http://www.dwheeler.com/oss fs refs.html 58
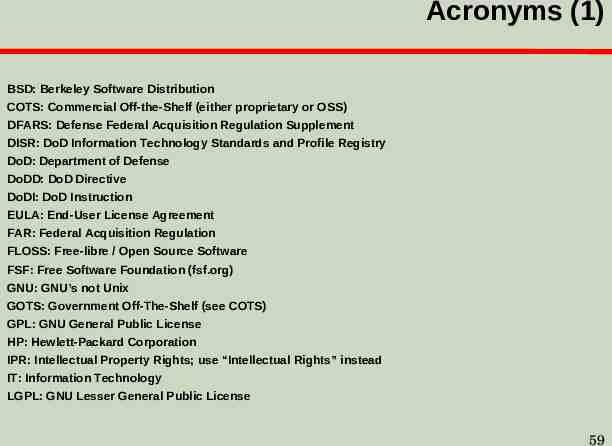
Acronyms (1) BSD: Berkeley Software Distribution COTS: Commercial Off-the-Shelf (either proprietary or OSS) DFARS: Defense Federal Acquisition Regulation Supplement DISR: DoD Information Technology Standards and Profile Registry DoD: Department of Defense DoDD: DoD Directive DoDI: DoD Instruction EULA: End-User License Agreement FAR: Federal Acquisition Regulation FLOSS: Free-libre / Open Source Software FSF: Free Software Foundation (fsf.org) GNU: GNU’s not Unix GOTS: Government Off-The-Shelf (see COTS) GPL: GNU General Public License HP: Hewlett-Packard Corporation IPR: Intellectual Property Rights; use “Intellectual Rights” instead IT: Information Technology LGPL: GNU Lesser General Public License 59
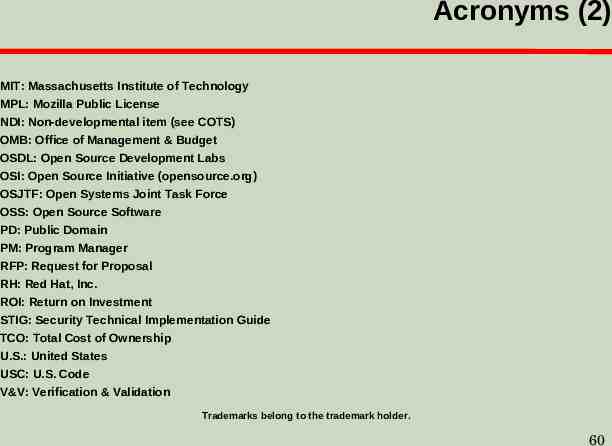
Acronyms (2) MIT: Massachusetts Institute of Technology MPL: Mozilla Public License NDI: Non-developmental item (see COTS) OMB: Office of Management & Budget OSDL: Open Source Development Labs OSI: Open Source Initiative (opensource.org) OSJTF: Open Systems Joint Task Force OSS: Open Source Software PD: Public Domain PM: Program Manager RFP: Request for Proposal RH: Red Hat, Inc. ROI: Return on Investment STIG: Security Technical Implementation Guide TCO: Total Cost of Ownership U.S.: United States USC: U.S. Code V&V: Verification & Validation Trademarks belong to the trademark holder. 60