HIPAA Privacy and Security Rules Kim C. Stanger Compliance
72 Slides9.20 MB
HIPAA Privacy and Security Rules Kim C. Stanger Compliance Bootcamp (5/15)
This presentation is similar to any other legal education materials designed to provide general information on pertinent legal topics. The statements made as part of the presentation are provided for educational purposes only. They do not constitute legal advice nor do they necessarily reflect the views of Holland & Hart LLP or any of its attorneys other than the speaker. This presentation is not intended to create an attorney-client relationship between you and Holland & Hart LLP. If you have specific questions as to the application of law to your activities, you should seek the advice of your legal counsel.
Health Insurance Portability and Accountability Act (“HIPAA”) 2003: Privacy Rules, 45 CFR 164.500 – Requires covered entities to protect privacy of protected health info (“PHI”) – Gives patients certain rights concerning their info. 2005: Security Rules, 45 CFR 164.300 – Requires covered entities to implement safeguards to protect electronic PHI. 2009: HITECH Act – Expanded and strengthened HIPAA. 2009: Breach Notification Rule, 45 CFR 164.400 – Requires covered entities to report breaches of unsecured info. 2013: HIPAA Omnibus Rule, 78 FR 5566 (1/25/13) – Implemented and finalized HITECH Act requirements.
Other Privacy Laws Must comply with other law if it is more strict than HIPAA, i.e., – Provides greater protection to patient info. – Provides patients greater rights regarding their info. Other privacy laws: – Federally funded drug and alcohol treatment programs, 42 CFR part 2 – State drug and alcohol treatment programs – Common law privacy rights. – Other?
HIPAA Enforcement Business Associates HIPAA Covered Entities
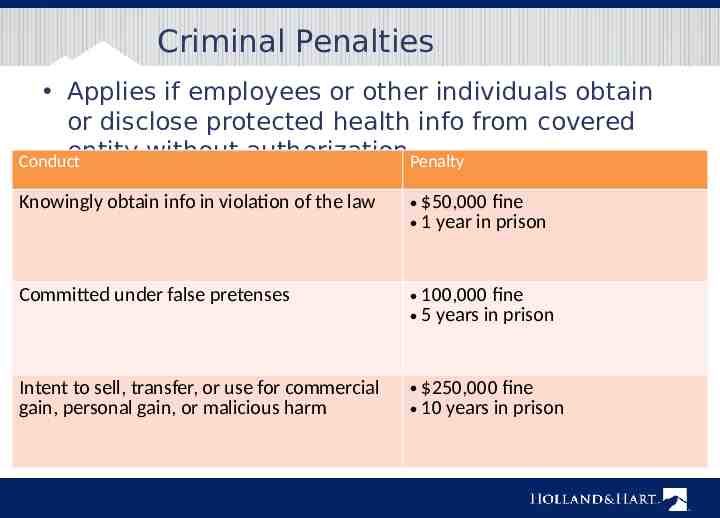
Criminal Penalties Applies if employees or other individuals obtain or disclose protected health info from covered entity without authorization.Penalty Conduct Knowingly obtain info in violation of the law 50,000 fine 1 year in prison Committed under false pretenses 100,000 fine 5 years in prison Intent to sell, transfer, or use for commercial gain, personal gain, or malicious harm 250,000 fine 10 years in prison
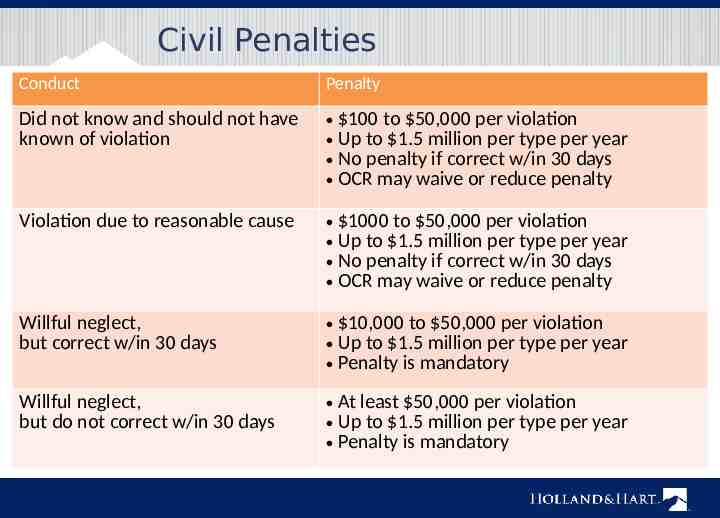
Civil Penalties Conduct Penalty Did not know and should not have known of violation 100 to 50,000 per violation Up to 1.5 million per type per year No penalty if correct w/in 30 days OCR may waive or reduce penalty Violation due to reasonable cause 1000 to 50,000 per violation Up to 1.5 million per type per year No penalty if correct w/in 30 days OCR may waive or reduce penalty Willful neglect, but correct w/in 30 days 10,000 to 50,000 per violation Up to 1.5 million per type per year Penalty is mandatory Willful neglect, but do not correct w/in 30 days At least 50,000 per violation Up to 1.5 million per type per year Penalty is mandatory
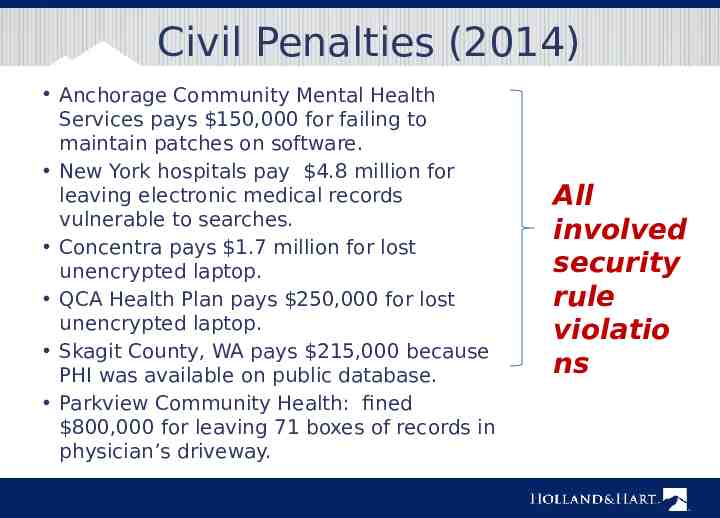
Civil Penalties (2014) Anchorage Community Mental Health Services pays 150,000 for failing to maintain patches on software. New York hospitals pay 4.8 million for leaving electronic medical records vulnerable to searches. Concentra pays 1.7 million for lost unencrypted laptop. QCA Health Plan pays 250,000 for lost unencrypted laptop. Skagit County, WA pays 215,000 because PHI was available on public database. Parkview Community Health: fined 800,000 for leaving 71 boxes of records in physician’s driveway. All involved security rule violatio ns
Enforcement State attorney general can bring lawsuit. – 25,000 fine per violation fees and costs In future, individuals may recover percentage of penalties. – Still waiting for regulations. Must sanction employees who violate HIPAA. OCR to resume compliance audits. Must self-report breaches of unsecured protected health info. – To affected individuals. – To HHS. – To media if breach involves 500 persons.
Who and What Does it Cover?
Entities Subject to HIPAA Covered entities – Health care providers who engage in certain electronic transactions. – Health plans, including employee group health plans if: 50 or more participants; or Administered by third party (e.g., TPA or insurer). – Health care clearinghouses. Business associates of covered entities – Entities with whom you share PHI to perform services on your behalf.

Protected Health Information Protected health info (“PHI”) – Individually identifiable health info, i.e., info that could be used to identify individual. – Concerns physical or mental health, health care, or payment. – Created or received by covered entity in its capacity as a healthcare provider. – Maintained in any form or medium, e.g., oral, paper, electronic, images, etc. Not de-identified info.
Prohibited Actions Unauthorized disclosure outside covered entity. Unauthorized use within covered entity. Unauthorized access within covered entity.
Use and Disclosure Rules (45 CFR 164.502-.514)
Use and Disclosure Rules Cannot use or disclose PHI unless— – For purposes of treatment, payment, or healthcare operations. – For disclosures to family members and others involved patients care or payment for care if: Patient has not objected, Disclosure appropriate under circumstances, and Limit disclosure to person’s involvement. – For certain safety or government purposes as listed in 45 CFR 164.512. – Have a valid written authorization signed by patient that complies with 45 CFR 164.508.
Treatment, Payment or Operations May use or disclose PHI without patient’s authorization for: – Treatment – Payment – Health care operations Except psychotherapy notes. If agree with patient to limit use or disclosure for treatment, payment, or healthcare operations, you must abide by that agreement except in an emergency. – Don’t agree! It increases liability. (45 CFR 164.506 and 164.522)
Persons Involved in Care May use or disclose PHI to family or others involved in patient’s care or payment for care if conditions met. – If patient present, may disclose if: Patient agrees to disclosure or has chance to object and does not object, or Reasonable to infer agreement from circumstances. – If patient unable to agree, may disclose if: Patient has not objected; and You determine it is in the best interest of patient. – Limit disclosure to scope of person’s involvement. Applies to disclosures after the patient is deceased. (45 CFR 164.510)
Safety and Govt Functions Authorization is not required if certain regulatory conditions are satisfied. – Avoid serious and imminent threat – Another law requires disclosure – Per court order, warrant or subpoena – Law enforcement if conditions satisfied – Public health activities – Health oversight activities – Workers compensation – Coroners – Persons in custody – Military purposes Check with privacy officer or 42 CFR 164.512 to determine if conditions are satisfied. (45 CFR 164.512)
Authorization May use or disclose PHI if have valid written authorization signed by patient or their personal representative. Authorization must contain elements and statements required in 45 CFR 164.508. Cannot combine HIPAA authorization with other consents or documents. Certain uses or disclosures require authorization. – Psychotherapy notes, except provider’s use of own notes for treatment purposes. – For marketing purposes. – For sale of protected info. (45 CFR 164.508)
Verification Before disclosing PHI: – Verify the identity and authority of person requesting info if he/she is not known. E.g., check the badge or papers of officers; birthdates or SSN for family; etc. – Obtain any documents, representations, or statements required to make disclosure. E.g., written satisfactory assurances accompanying a subpoena, or representations from police that they need info for immediate identification purposes. (45 CFR 164.512(f))
Minimum Necessary Standard Cannot use or disclose more than is reasonably necessary for intended purpose. Does not apply to disclosures to: – Patient – Provider for treatment – Per individual’s authorization Must have policies regarding – Role-based access – Routine disclosures and requests for info (45 CFR 164.502 and .514)
Personal Representatives Under HIPAA, you must treat the personal rep as if they were the patient. Personal reps generally have right to exercise patient rights, e.g., – Request restrictions on use or disclosure of protected info. – Access protected info. – Amend protected info. – Obtain accounting of disclosures of protected info. Personal rep persons with authority under state law to: – Make healthcare decisions for patient. – Make decisions for deceased patient’s estate. (45 CFR 164.502(g))
Personal Representatives Not required to treat personal rep of minor (i.e., do not disclose protected info to them) if: – Minor has authority to consent to care. – Minor obtains care at the direction of a court or person appointed by the court. – Parent agrees that provider may have a confidential relationship. – Provider determines that treating personal rep as the patient is not in the best interest of patient, e.g., abuse.
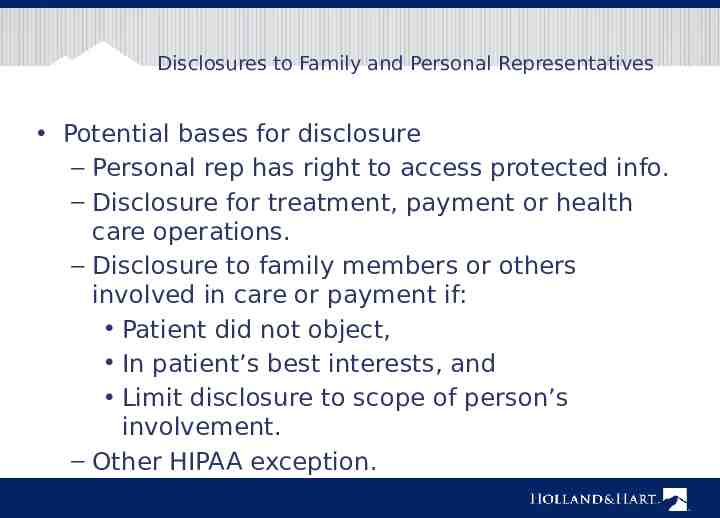
Disclosures to Family and Personal Representatives Potential bases for disclosure – Personal rep has right to access protected info. – Disclosure for treatment, payment or health care operations. – Disclosure to family members or others involved in care or payment if: Patient did not object, In patient’s best interests, and Limit disclosure to scope of person’s involvement. – Other HIPAA exception.
Business Associates (45 CFR 164.502 and .504) I am your Business Associate
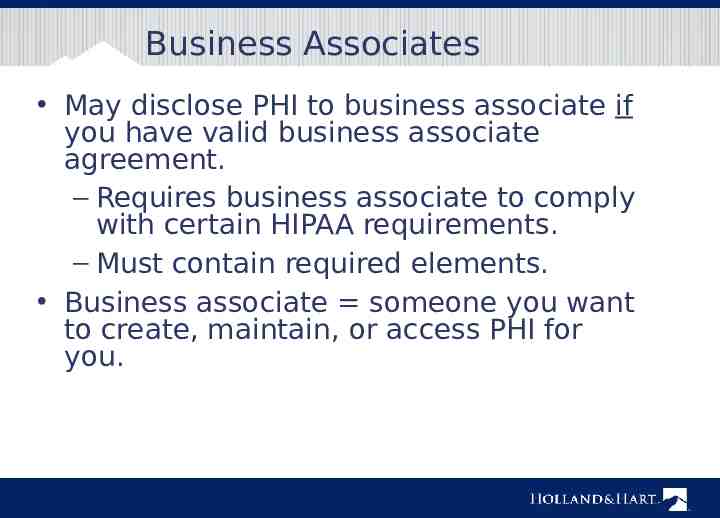
Business Associates May disclose PHI to business associate if you have valid business associate agreement. – Requires business associate to comply with certain HIPAA requirements. – Must contain required elements. Business associate someone you want to create, maintain, or access PHI for you.
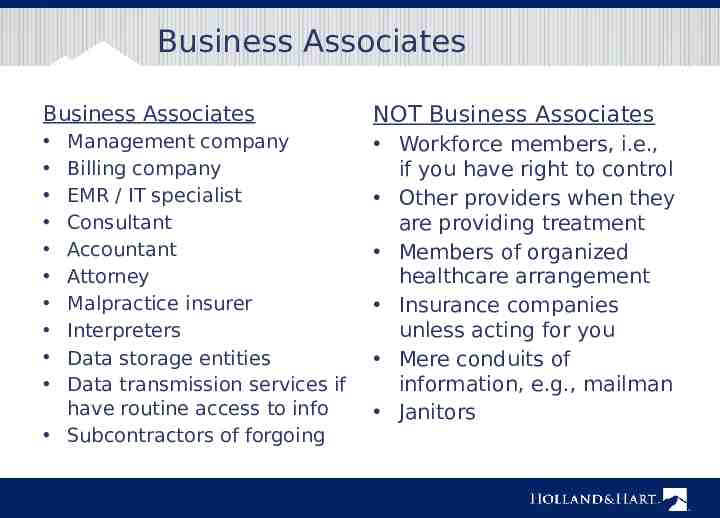
Business Associates Business Associates NOT Business Associates Workforce members, i.e., if you have right to control Other providers when they are providing treatment Members of organized healthcare arrangement Insurance companies unless acting for you Mere conduits of information, e.g., mailman Janitors Management company Billing company EMR / IT specialist Consultant Accountant Attorney Malpractice insurer Interpreters Data storage entities Data transmission services if have routine access to info Subcontractors of forgoing
Business Associates Covered entity is liable for acts of business associate if: – Knew or should know that business associate is violating HIPAA and covered entity fails to act; or – Business associate is the covered entity’s agent. Make sure business associate is an independent contractor, not an agent. – Business associate agreement should confirm same. – Make sure you do not control method and manner of business associate’s functions.
HIPAA Security Rule (45 CFR 164.300 et seq.)
Civil Penalties (2014) Anchorage Community Mental Health Services pays 150,000 for failing to maintain patches on software. New York hospitals pay 4.8 million for leaving electronic medical records vulnerable to searches. Concentra pays 1.7 million for lost unencrypted laptop. QCA Health Plan pays 250,000 for lost unencrypted laptop. Skagit County, WA pays 215,000 because PHI was available on public database. Parkview Community Health: fined 800,000 for leaving 71 boxes of records in physician’s driveway. All involved security rule violatio ns
Security Rule Conduct risk analysis. Implement safeguards. – Administrative – Technical – Physical Execute business associate Intended to ensure: Confidentiality Integrity Availability of ePHI.
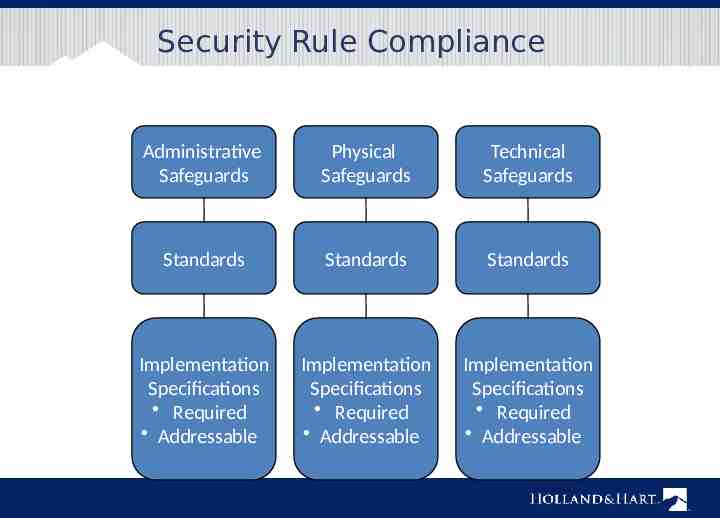
Security Rule Compliance Administrative Safeguards Physical Safeguards Technical Safeguards Standards Standards Standards Implementation Specifications Required Addressable Implementation Specifications Required Addressable Implementation Specifications Required Addressable

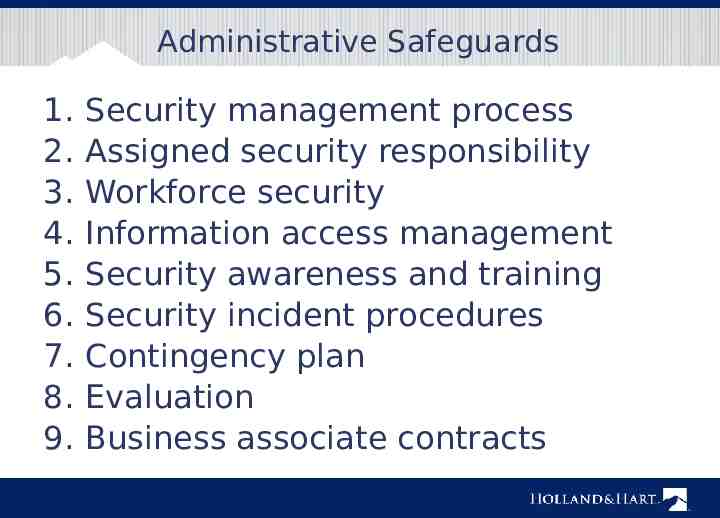
Administrative Safeguards 1. 2. 3. 4. 5. 6. 7. 8. 9. Security management process Assigned security responsibility Workforce security Information access management Security awareness and training Security incident procedures Contingency plan Evaluation Business associate contracts
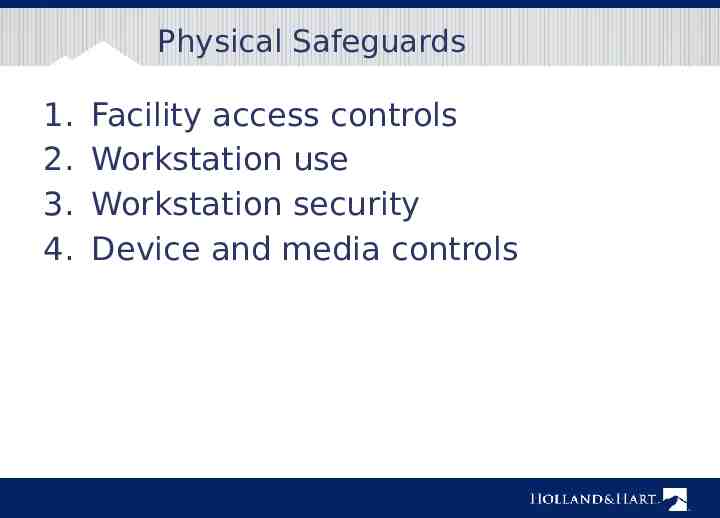
Physical Safeguards 1. 2. 3. 4. Facility access controls Workstation use Workstation security Device and media controls
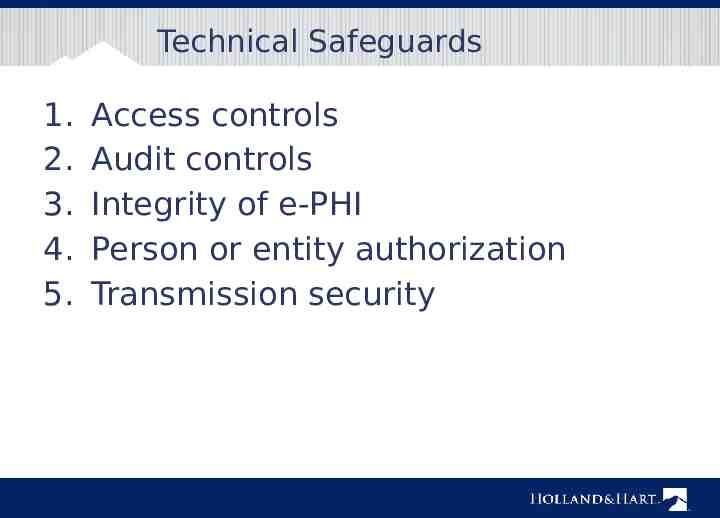
Technical Safeguards 1. 2. 3. 4. 5. Access controls Audit controls Integrity of e-PHI Person or entity authorization Transmission security
Data Privacy and Security
Risk Analysis Security rule requires that covered entities and business associates “conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity and availability of [ePHI] ” (45 CFR 164.308(a)). – Frequently cited in recent violations. Periodically reevaluate analysis. – New systems or equipment. – Every few (very few?) years. – Include mobile devices.
Risk Analysis Additional materials are available at www.hhs.gov/ocr/privacy/hipaa/admi nistrative/securityrule/securityrulegui dance.html – Final Guidance on Risk Analysis – OCR Guidance re Risk Analysis – NIST Publications
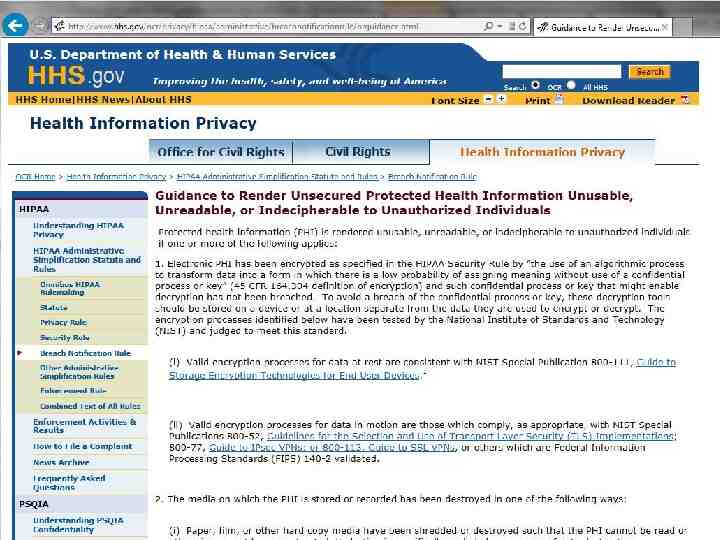
Encryption Encryption is an addressable standard per 45 CFR 164.312: (e)(1) Standard: Transmission security. Implement technical security measures to guard against unauthorized access to [ePHI] that is being transmitted over an electronic communications network. (2)(ii) Encryption (Addressable). Implement a mechanism to encrypt electronic protected health information whenever deemed appropriate. ePHI that is properly encrypted is “secured”. – Not subject to breach reporting. OCR presumes that loss of unencrypted laptop, USB, mobile device is breach.

Communicating by E-mail or Text HIPAA Privacy Rule allows patient to request communications by alternative means or at alternative locations. – Including unencrypted e-mail. (45 CFR 164.522(b)) Omnibus Rule commentary states that covered entity or business associate may communicate with patient via unsecured e-mail so long as they warn patient of risks and patient elects to communicate via unsecured e-mail to text. (78 FR 5634)
HIPAA Patient Rights (45 CFR 164.520-.528)

Individual Rights Right to receive notice of privacy practices. Right to request additional restrictions on use or disclosure for treatment, payment or operations. Right to receive information by alternative means or at alternative location. Right to access protected health information. Right to request amendment of protected health information.
Notice of Privacy Practices Notice summarizes HIPAA rules and explains how you will use the patient’s information. Direct treatment providers: – Give copy to patients by first date of treatment. – Post notice in “prominent locations” – Post notice on website. – Make good faith attempt to obtain acknowledgment of receipt. (45 CFR 164.520)

Request Restrictions on Use or Disclosure Individual has right to request additional restrictions on use or disclosure for treatment, payment and operations. Covered entity may generally decline restrictions. – DON’T AGREE! If covered entity agrees to additional restrictions, it must abide by them unless: – Emergency, or – Disclosure required by regulations. Covered entity may terminate the agreement for additional restrictions prospectively. (45 CFR 164.522)
Restrictions on Disclosures to Health Insurers Per omnibus rule, must agree to request of a patient to restrict disclosure of protected info to a health plan if: – Protected info pertains to health care item or service for which the patient, or another person on the patient’s behalf, paid the covered entity in full; and – Disclosure is for the purpose of carrying out payment or health care operations and is not otherwise required by law. Don’t ask the patient! (45 CFR 164.522)
Request Alternative Communications Must accommodate reasonable request to receive info by alternative means or at alternative locations. – May require written request. – May not require explanation. – May require info as to how payment will be handled. (45 CFR 164.522(b))
Access PHI Patient or personal rep generally has right to inspect and obtain copy of PHI in “designated record set, i.e., documents used to make decisions concerning healthcare or payment. Must respond within 30 days. Must provide records in requested form if readily producible, including electronic form. May require written request. May charge reasonable cost-based fee, i.e., cost of actual labor and materials in making copies, not administrative or retrieval fee. Check with privacy officer or review 45 CFR 164.524 before denying request. (45 CFR 164.524)

Request Amendment Individual has right to request amendment. Covered entity may deny request if: – Record not part of designated record set. – Entity did not create the record unless creator no longer available. – Record is accurate and complete. Must act on request within 60 days. If accept request, amend record accordingly. If deny request, notify patient of basis for denial. – Patient has right to have request become part of record. Check with privacy officer or review 45 CFR 164.526 when responding to requests. (45 CFR 164.526)
Accounting of Disclosures Individual may obtain accounting of certain disclosures made for prior 6 years. – Improper disclosures. – Disclosures for certain safety or govt functions under 45 CFR 164.512. Must maintain log of disclosures, including: – Date of disclosure. – Name of entity receiving disclosure. – Description of info disclosed. – Describe purpose of disclosure. Must account for disclosures by business associates. Check with privacy officer. (45 CFR 164.528)
Breach Notification (45 CFR 164.400 et seq.)
Breach Notification If there is breach of unsecured protected info, – Covered entity must notify: Each individual whose unsecured info has been or reasonably believed to have been accessed, acquired, used, or disclosed. HHS. Media, if breach involves 500 persons in a state. – Business associate must notify covered entity.
Breach Acquisition, access, use or disclosure of protected health info in violation of privacy rules is presumed to be a breach unless the covered entity or business associate demonstrates that there is a low probability that the info has been compromised based on a risk assessment of the following factors: – nature and extent of PHI involved; – unauthorized person who used or received the PHI; – whether PHI was actually acquired or viewed; and – extent to which the risk to the PHI has been mitigated.
If you think you have a breach Act immediately to mitigate or correct the breach. – Retrieve the PHI. – Confirm that PHI has not been improperly accessed, used or disclosed, or if it has, obtain assurance that no further disclosure. Notify privacy officer immediately. Correct any process that resulted in improper disclosures. Conduct additional training. Remember: prompt action may allow provider to — – Satisfy its duty to mitigate. – Avoid disclosure and breach reporting obligation.
Administrative Requirements (45 CFR 164.530)
Administrative Requirements Designate privacy and security officers. Train workforce. Implement written policies and procedures. Respond to complaints and violations. Mitigate improper disclosures. Maintain documentation for 6 years. Implement reasonable safeguards. – “Incidental disclosures” do not violate HIPAA. (45 CFR 164.530)
Action Items HIPAA Top 10 List
HIPAA Action Items 1. Assign and document HIPAA responsibility. Privacy officer Security officer 2. Ensure the officers understand the rules. 3. Review security rule compliance. Conduct and document security risk assessment. Beware electronic devices. 4. Ensure you have required policies. Privacy rule. Security rule. Breach notification rule.
HIPAA Action Items 5. Develop and use compliant forms. – Authorization, privacy notice, patient requests, etc. 6. Execute BAAs with business associates. – Ensure they are independent contractors. – Follow up if there are problems with business associate. 7. Train members of workforce and document training. – Upon hiring. – Periodically thereafter. 8. Use appropriate safeguards. – Confidentiality agreements with workforce members. – Reasonable administrative, technical and physical safeguards
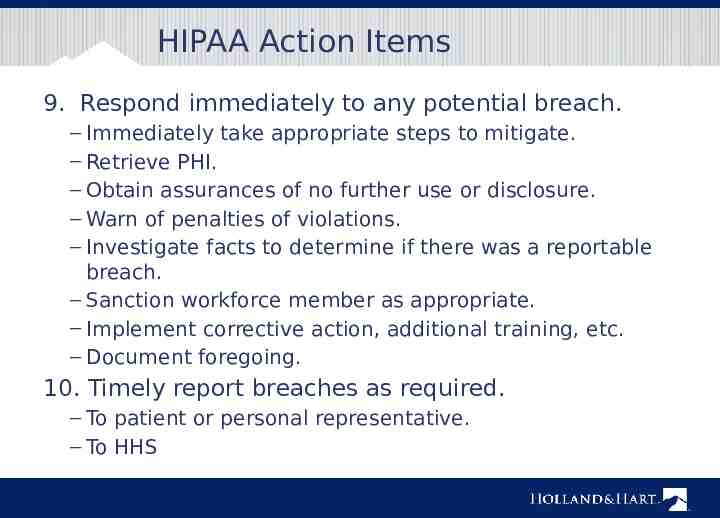
HIPAA Action Items 9. Respond immediately to any potential breach. – Immediately take appropriate steps to mitigate. – Retrieve PHI. – Obtain assurances of no further use or disclosure. – Warn of penalties of violations. – Investigate facts to determine if there was a reportable breach. – Sanction workforce member as appropriate. – Implement corrective action, additional training, etc. – Document foregoing. 10. Timely report breaches as required. – To patient or personal representative. – To HHS
Additional Resources
www.hhs.gov/ocr/privacy
Webinars Publications
Questions? Kim C. Stanger (208) 383-3913 (208) 409-7907 (cell) kcstanger@hollandhar t.com Melissa Starry (208) 383-3984 (208) 598-4001 [email protected] m