Voice over IP (VoIP) security
17 Slides515.02 KB
Voice over IP (VoIP) security
Introduction Voice over IP and IP telephony Network convergence – Telephone and IT – PoE (Power over Ethernet) Mobility and Roaming Telco – Switched - Packet (IP) – Closed world - Open world Security and privacy – IPhreakers – VoIP vs 3G
Architecture: protocols Signaling – User location – Session Setup Negotiation Modification Closing Transport – Encoding, transport, etc.
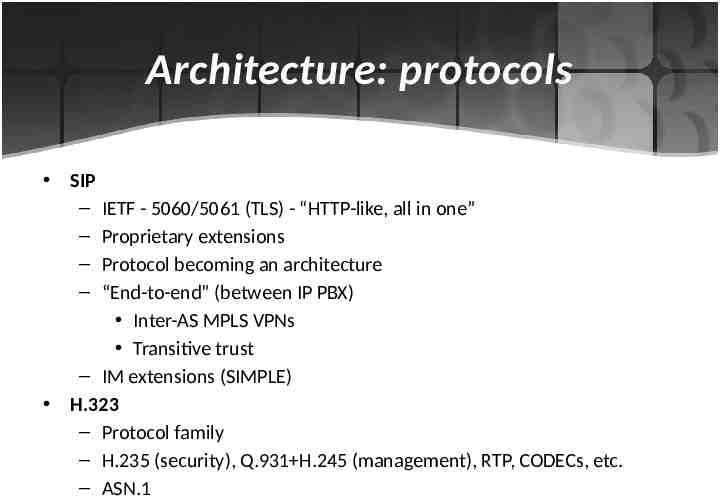
Architecture: protocols SIP – IETF - 5060/5061 (TLS) - “HTTP-like, all in one” – Proprietary extensions – Protocol becoming an architecture – “End-to-end” (between IP PBX) Inter-AS MPLS VPNs Transitive trust – IM extensions (SIMPLE) H.323 – Protocol family – H.235 (security), Q.931 H.245 (management), RTP, CODECs, etc. – ASN.1
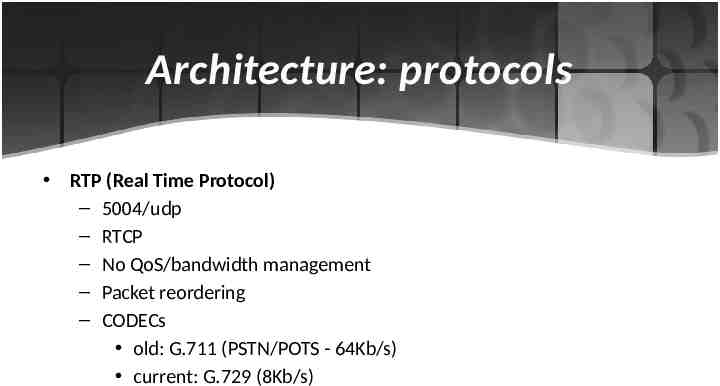
Architecture: protocols RTP (Real Time Protocol) – 5004/udp – RTCP – No QoS/bandwidth management – Packet reordering – CODECs old: G.711 (PSTN/POTS - 64Kb/s) current: G.729 (8Kb/s)
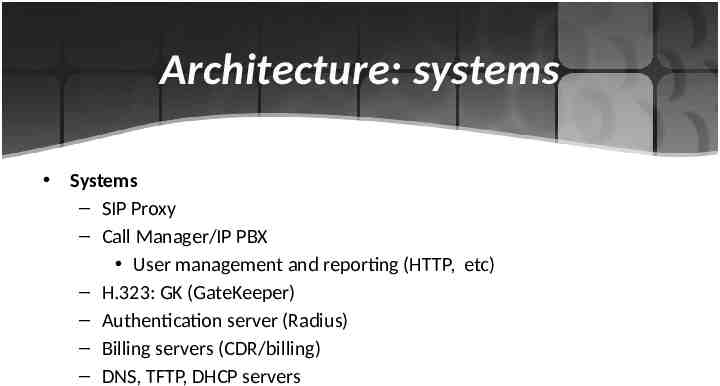
Architecture: systems Systems – SIP Proxy – Call Manager/IP PBX User management and reporting (HTTP, etc) – H.323: GK (GateKeeper) – Authentication server (Radius) – Billing servers (CDR/billing) – DNS, TFTP, DHCP servers
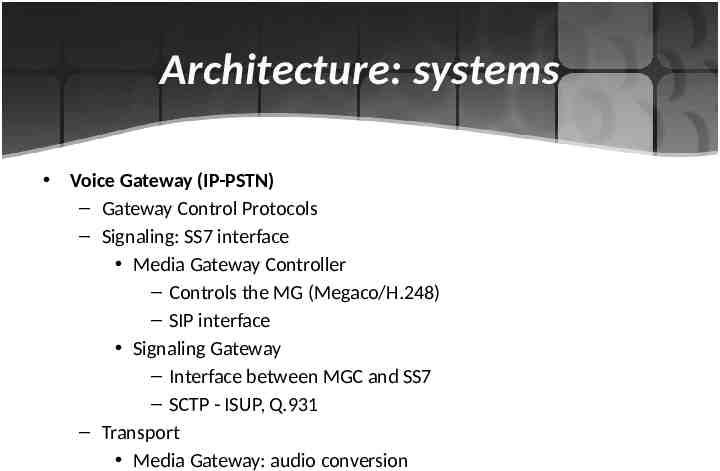
Architecture: systems Voice Gateway (IP-PSTN) – Gateway Control Protocols – Signaling: SS7 interface Media Gateway Controller – Controls the MG (Megaco/H.248) – SIP interface Signaling Gateway – Interface between MGC and SS7 – SCTP - ISUP, Q.931 – Transport Media Gateway: audio conversion
Architecture: firewall/VPN Firewall – “Non-stateful” filtering – “Stateful” filtering – Application layer filtering (ALGs) – NAT / “firewall piercing” (H.323 : 2xTCP, 4x dynamic UDP - 1719,1720) (SIP : 5060/udp) Encrypted VPN – SSL/TLS – IPsec – Where to encrypt (LAN-LAN, phone-phone, etc)?
VOIP Threats Denial of Service – ICMP Flood – IP Spoofing – Port Scans – Land Attack – IP Source Route Evasdropping or recording – In VOIP eavesdropping is a type of an attack, if an attacker able to eavesdropp a communication. Then he can launch different type of an attack like Man in the Middle attack etc. Call Hijacking and Spoofing Call Redirection Voice SPAM (Vishing, Mailbox Stuffing, Unsolicited Calling) Voicemail Hacking
VOIP Attacks Signaling Layer Attacks – SIP Registration Hijacking – Impersonating a Server – SIP Message Modification – SIP Cancel / SIP BYE attack – SIP DOS attack Media Layer Attacks – Eavesdropping – RTP insertion attack SSRC collision attacks
Signaling Layer Attacks SIP Registration attack Attacker impersonates a valid UA to a registrar himself as a valid user agent. So attacker can recieve calls for a legitmate user. Impersonating a Server When an attacker impersonates a remote server and user agent request are served by the attacker machine. SIP Message Modification If an attacker launches a man in the middle attack and modify a message. Then attacker could lead the caller to connect to malicious system. SIP CANCEL / SIP BYE SIP Denial of Service In SIP attacker creates a bogus request that contained a fake IP address and Via field in the SIP header contains the identity of the target host.
Media Layer Attacks Eavesdropping SSRC collision If an attacker eavesdropp the conversation and uses one’s peer SSRC to send RTP packet to other peer, it causes to terminate a session.
Security Solutions Two types of security solutions End-to-End security In SIP end points can ensure end-to-end security to those messages which proxy does not read, like SDP messages could be protectedusing S/MIME. Media is transferred directly, so end-to-end security is achieved by SRTP. Hop-by-hop security TLS, IPSec TLS provide transport layer security over TCP. Normally SIP URI is in the form of sip:[email protected], but if we are using TLS then SIP URI will be sips:[email protected] and signaling must be send encrypted.
Authentication Authentication means to identify a person. If we take SIP as signaling protocol in VOIP, it defines two mechanisms for authentication HTTP digest authentication S/MIME HTTP Digest Authentication HTTP digests mechanisms used between users to proxies, users to users but not between proxies to proxies. S/MIME S/MIME uses X.509 certificates to authenticate end users in the same way that web browsers use them.
Media Encryption In VOIP media is send directly between users using RTP. Encryption of media is achieved by – IPSec – Secure RTP (SRTP) It provides a framework for encryption and message authentication of RTP and RTCP. Cipher Algorithum: AES Authenitcation is an optional feature. SRTP uses Security Description for Media Streams (SDES) algorithum to negotiate session keys in SDP. – MIKKEY Mikkey provides its own authentication and integrity mechanisim. Mikkey messages carried in a SDP with a key-mgmt attritbute.
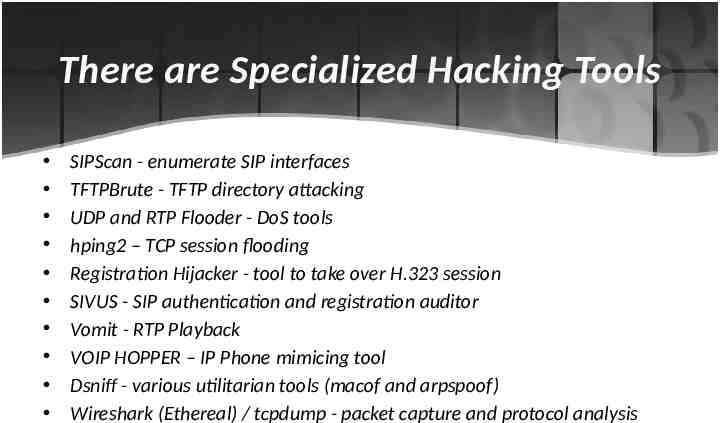
There are Specialized Hacking Tools SIPScan - enumerate SIP interfaces TFTPBrute - TFTP directory attacking UDP and RTP Flooder - DoS tools hping2 – TCP session flooding Registration Hijacker - tool to take over H.323 session SIVUS - SIP authentication and registration auditor Vomit - RTP Playback VOIP HOPPER – IP Phone mimicing tool Dsniff - various utilitarian tools (macof and arpspoof) Wireshark (Ethereal) / tcpdump - packet capture and protocol analysis

Thanks You